Keep Unsecured Machines Off Your Network (A WinIT Pro Podcast)
A couple of weeks ago, I had the opportunity to sit down with Karen Forster of Windows IT Pro magazine to record a podcast about a whole slew of things related to our network security solutions (aka policy-driven network access solutions):
Here's the synopsis Karen wrote to describe our 20 minute chat:
Imagine your network protecting itself by preventing unsecured devices from accessing your resources. Microsoft is now providing technology that ensures every device that connects to your network has up-to-date security protection (e.g., current patches, anti-virus and anti-spyware). You can keep machines that are not compliant with your security policies off your network with Network Access Control (NAC) technologies for Longhorn Server and Windows Vista. Karen Forster discusses Microsoft's recent announcements about NAC, as well as Network Access Protection (NAP), with Microsoft's Ian Hameroff. Learn how NAC and NAP work and what technologies are involved, as well as what third-party products are poised to work with these technologies, in this exclusive interview.
The chat covers things like Server and Domain Isolation and Network Access Protection, as well as Bill and Craig's keynote from RSA 2007.
Since the recording of the podcast, we've taken a big leap forward in our internal deployment of NAP (aka "The Pilot"). We're now up and running across very large (10s of thousands clients) swaths of our network here in Redmond and MSIT is already seeing benefit from the policy-enforcement mechanisms.
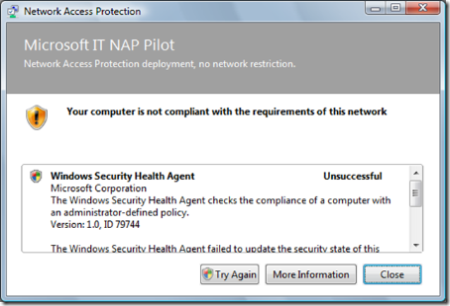
For example, I attempted to shutdown my antivirus real-time scanner service and was immediately dinged by NAP:
As soon as I restarted the service, I was deemed healthy and carried on with no issues. The neat thing with the fact the NAP agent is built into Windows Vista (we're running Windows Vista Enterprise) is I did not need to install any software or anything. In fact, I didn't even know that the "switch had been thrown" until my manager sent out a note stating such.
Anyhow, checkout this podcast and let me know if you have any questions!