Automatic Bitlocker on Windows 10 during Azure AD Join
Update June 2017 - please read my post here for a workaround on all devices.
There are a lot of myths on how to automatically trigger Bitlocker on an Azure AD Joined Windows 10 device, let’s hope this post will get you some answers.
Windows 10 will automatically encrypt the local drive when joining an InstantGo capable device to Azure Active Directory (AAD). An AAD Join can either done during the “Out Of Box Experience” (OOBE) or when Window is installed by going to the “About” screen, here you have the option to Azure AD Join the device.
As an admin you can configure Azure AD in such a way that the device is automatically registered in your Mobile Device Management solution.
Important note: You cannot use Microsoft Intune (or any other MDM) to specify a policy and force Bitlocker on a Windows 10 PC. This is done automatically during an Azure AD Join.
What does “InstantGo capable device” mean?
InstantGo (formerly known as Connected Standby) is a very low power state that some devices support. It’s very like your mobile phone, it’s almost switched off but still can receive text messages, e-mails and switch to a different power state when receiving phone calls.
A growing list of devices support InstantGo, you can manually check if your device supports this powerstate as follows:
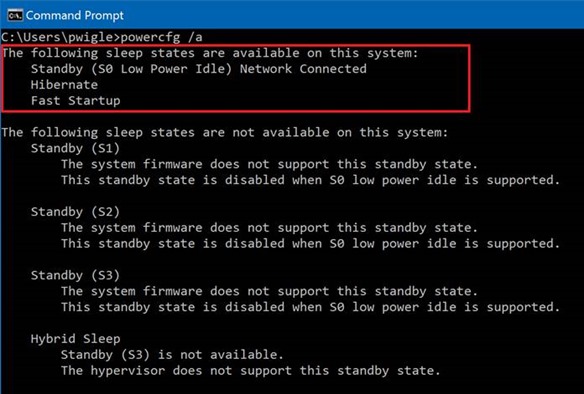
- Open a command prompt
- Type “powercfg /a”
Devices that have InstantGo support will return “Network Connected”:
If your device does not support InstantGo (and therefore: no automatic Bitlocker during Azure AD Join) you will get something similar to this: 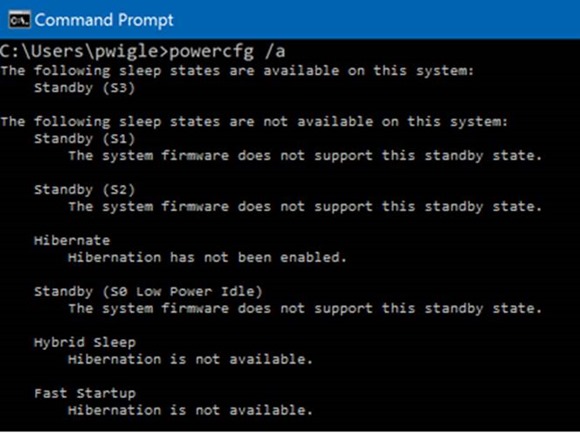
Keep in mind that this also applies to Virtual Machines. Automatic Bitlocker during Azure AD Join requires physical InstantGo Capable devices.
Where do I find the recovery key?
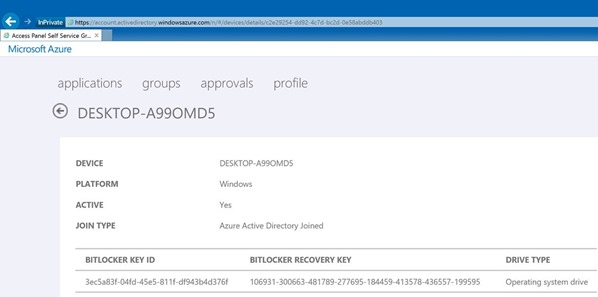
Users can retrieve their recovery key by going to https://myapps.microsoft.com, select Devices and select the device for which they would like to get the recovery key:
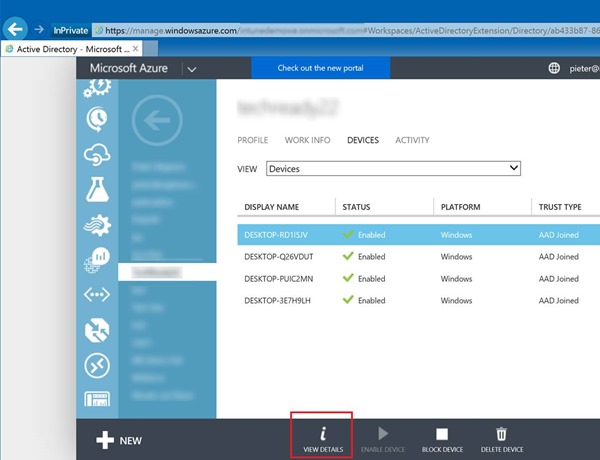
As an Azure tenant admin you can find the recovery keys for your users by going to https://manage.windowsazure.com, browse to your Active Directory, go to the Users tab and select the user who enrolled a specific device. Browse to Devices and change the dropdown list to view Devices.
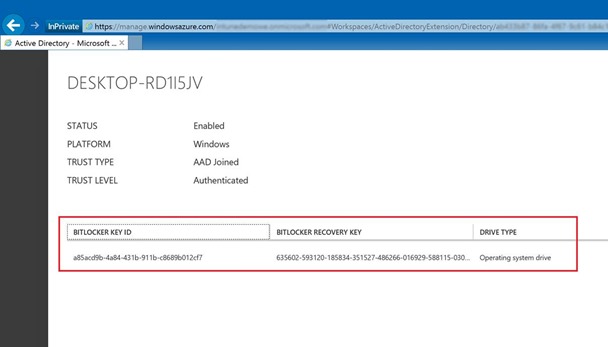
Find the device for which you would like to have the recovery key and hit Details.
“I have InstantGo capable devices but Bitlocker is not enabled automatically during an Azure AD Join”
If you are sure your device is InstantGo capable (e.g. Surface Pro 3 or Surface Pro 4) it could be that the image you are using has Automatic Bitlocker during AAD Join disabled – this is controlled by a registry key.
Update October 2016: The surface recovery image has been updated to fix this issue. Recently we have seen this issue with the Surface Pro 4 Recovery Images. Until the Recovery images are updated you can work around this by either:
Use a vanilla Windows 10 (1511) ISO or media, install Windows 10, perform the AAD Join. Either inject the Surface Pro drivers into the image in advance or install the drivers manually afterwards.
OR
During the Out Of Box Experience (OOBE) hit SHIFT-F10 on your keyboard, this will bring up a command prompt. Fire up REGEDIT and browse to
HKLM\System\CurrentControlSet\Control\Bitlocker\
Make sure that “PreventDeviceEncryption” is set to “0” 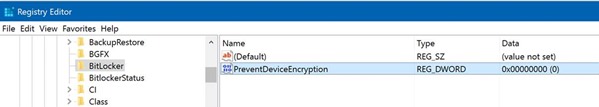
If you liked this post - please consider leaving a reply.