Troubleshoot WinRM with PowerShell—Part 1
Summary: Ed Wilson, Microsoft Scripting Guy, talks about using Windows PowerShell to look at WinRM logs.
 Hey, Scripting Guy! I am having problems with WinRM. When I use the Get-CimInstance cmdlet, it fails. When I specify the –DCOM protocol for Get-CimInstance, it works. I suspect I have a WinRM problem. How can I go about troubleshooting it?
Hey, Scripting Guy! I am having problems with WinRM. When I use the Get-CimInstance cmdlet, it fails. When I specify the –DCOM protocol for Get-CimInstance, it works. I suspect I have a WinRM problem. How can I go about troubleshooting it?
—TB
 Hello TB,
Hello TB,
Microsoft Scripting Guy, Ed Wilson, is here. One of the great things about Windows, regardless of the version, is that there are some awesome diagnostics and operational logs. I am not talking about the traditional event logs that have been around since the earliest versions of WinNT (System, Application, and Security logs)—rather, I am talking about the hundreds of other logs that exist.
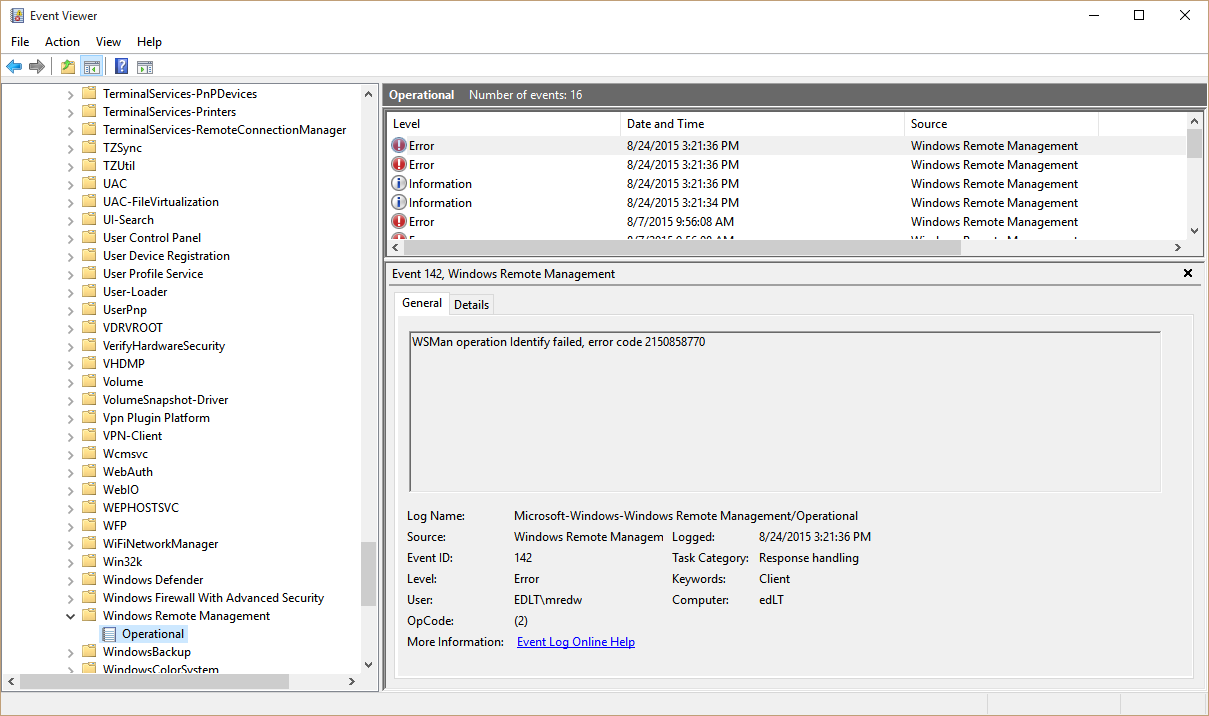
Of course, I can open the Event Viewer and go to Microsoft > Windows > Windows Remote Management, then find the Operational log:
But that is a lot of mousing around. So I can use the Get-WinEvent cmdlet, the –ListLog parameter, and a wildcard character to see all of the logs that exist:
Get-WinEvent -ListLog *
When I get through that list, I can look for the log. There is a major issue here, however. First of all, Microsoft-Windows-Windows kind of looks like an error, but, it is really there. Then the Remote Management/Operational part does not appear to exist. The good thing is that I can use wildcard characters and avoid a lot of typing. Here is the command I use:
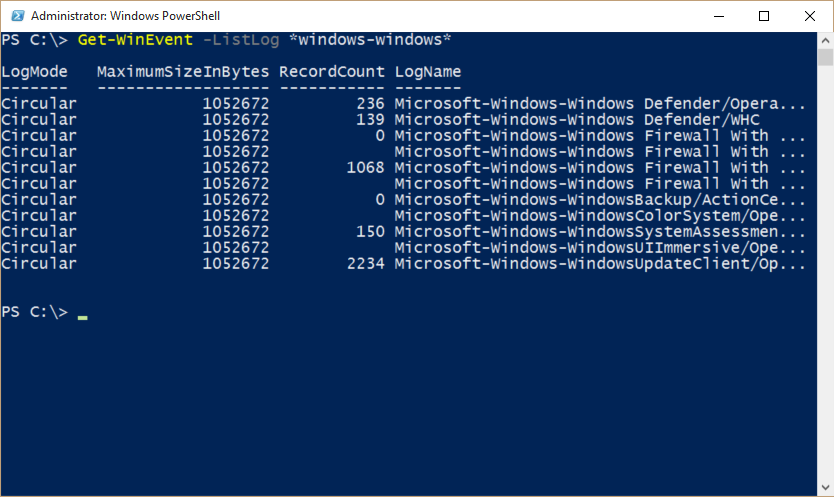
Get-WinEvent -ListLog *windows-windows*
The command and its associated output are shown here:
Nope. There is no Windows-Remote-Management anywhere to be found. Dude!
So, I am reduced to piping my log output to More, and paging through, one page at a time. Can you say time consuming, frustrating, and total waste of time? Try it. I bet you can.
Get-WinEvent -ListLog * | more
Finally, I find that (for whatever reason), they decided to rename the log name from the display name. I bet that was done to save time.
PS C:\> Get-WinEvent -ListLog *winrm*
LogMode MaximumSizeInBytes RecordCount LogName
——- —————— ———– ——-
Circular 1052672 16 Microsoft-Windows-WinRM/Operational
Clear the operational log
Windows PowerShell has a Clear-EventLog cmdlet, but that only works with traditional logs. To work with the hundreds of other event logs, I need to use the Wevtutil.exe program. Luckily, I can call this command-line tool inside Windows PowerShell, and even pipe stuff to it.
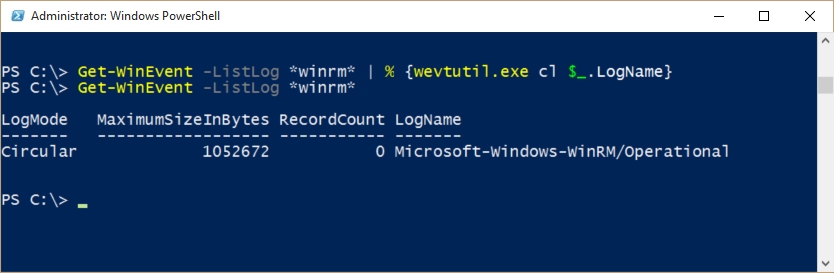
The first thing I like to do when I am troubleshooting is dump the log, and then take steps to re-create the problem. Here is the command to dump the WinRM log:
Get-WinEvent -ListLog *winrm* | % {wevtutil.exe cl $_.LogName}
Now I go back and check to ensure that the log is in fact dumped. These commands and the associated output are shown here:
I want to enable the WinRM log. To do this, again I use the Wevtutil.exe command. But because the command prompts, I need to feed it a Y (for yes). I can feed a Y to the command by using the echo command. The command to enable the log is shown here:
Get-WinEvent -ListLog *winrm* | % {echo y | wevtutil.exe sl $_.LogName /e:true}
To double-check that the log is enabled, I pipe the output from Get-WinEvent to Format-List:
PS C:\> Get-WinEvent -ListLog *winrm* | fl *
FileSize : 69632
IsLogFull : False
LastAccessTime : 8/6/2015 4:23:05 PM
LastWriteTime : 9/30/2015 4:46:32 PM
OldestRecordNumber : 0
RecordCount : 0
LogName : Microsoft-Windows-WinRM/Operational
LogType : Operational
LogIsolation : Application
IsEnabled : True
IsClassicLog : False
SecurityDescriptor : O:BAG:SYD:(A;;0x2;;;S-1-15-2-1)(A;;0xf0007;;;SY)(A;
;0x7;;;BA)(A;;0x7;;;SO)(A;;0x3;;;IU)(A;;0x3;;;SU)(A
;;0x3;;;S-1-5-3)(A;;0x3;;;S-1-5-33)(A;;0x1;;;S-1-5-
32-573)
LogFilePath : %SystemRoot%\System32\Winevt\Logs\Microsoft-Windows
-WinRM%4Operational.evtx
MaximumSizeInBytes : 1052672
LogMode : Circular
OwningProviderName : Microsoft-Windows-WinRM
ProviderNames : {Microsoft-Windows-WinRM}
ProviderLevel :
ProviderKeywords :
ProviderBufferSize : 64
ProviderMinimumNumberOfBuffers : 0
ProviderMaximumNumberOfBuffers : 64
ProviderLatency : 1000
ProviderControlGuid :
To disable the log, I set it to false. This command appears here:
Get-WinEvent -ListLog *winrm* | % {echo y | wevtutil.exe sl $_.LogName /e:false}
And, I can check the output once again with this command:
PS C:\> (Get-WinEvent -ListLog *winrm*).isenabled
False
I obviously don’t want to do all this typing, so I can put these commands in a script easily, or I can create a function and add them to a module. The cool thing is that I can also add other logs. I can even run the commands remotely by using Windows PowerShell remoting (assuming that you get it working).
TB, that is all there is to using Windows PowerShell to help troubleshoot your WinRM connection. Join me tomorrow when I will talk about more cool stuff.
I invite you to follow me on Twitter and Facebook. If you have any questions, send email to me at scripter@microsoft.com, or post your questions on the Official Scripting Guys Forum. See you tomorrow. Until then, peace.
Ed Wilson, Microsoft Scripting Guy

 Light
Light Dark
Dark
0 comments