Use PowerShell Functions to Authorize DHCP Servers
Summary: Microsoft Scripting Guy, Ed Wilson, talks about using functions from Windows 8 and Windows Server 2012 to authorize DHCP servers in AD DS.
Microsoft Scripting Guy, Ed Wilson, is here. Well, today it is sunny and about 70 degrees in Charlotte, North Carolina. This is a good thing because I head to Redmond, Washington, next week for a series of meetings, and I do not believe it will be sunny and warm there. In fact, according to my Get-InternationalWeather function I wrote a couple of years ago, it is 37.0 degrees F (2.0 degrees C) in Seattle right now—but at least it is not raining.
Yesterday, I talked about using Windows PowerShell to query Active Directory Domain Services (AD DS) for authorized DHCP servers. I used the Get-ADObject cmdlet from the ActiveDirectory module that is available from the Remote Server Admin Tools (RSAT)—this can be the Windows 7 RSAT or the Windows 8 RSAT. Today, I want to look at using a few cmdlets from the DHCPServer module that is in the RSAT for Windows 8 and Windows Server 2012.
Note Today’s post is a continuation of the Use PowerShell to Query AD DS for DHCP Servers post. As such, you should probably read that article before getting into today’s article. If you do not, you miss part of the plot.
One problem with querying from ADSI
When I began to query for DHCP servers by using the Get-DhcpServerInDC function, the output appeared to be a bit strange.
(Yesterday, I obtained the name of the DHCP server from AD DS through the ADSI Edit utility, and therefore, I queried using DNS.)
I did not recognize both IP addresses that it returned. When I used the Resolve-DNSName cmdlet, for the DHCP server, I found the following IP addresses registered in DNS.
PS C:\> Resolve-DnsName wds1
Name Type TTL Section IPAddress
—- —- — ——- ———
wds1.iammred.net A 1200 Answer 192.168.0.152
wds1.iammred.net A 1200 Answer 192.168.2.100
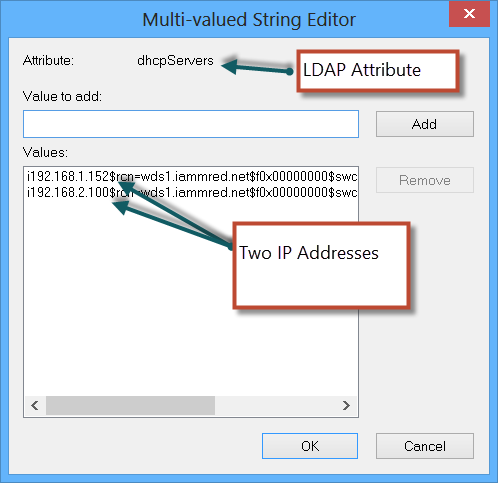
However, when I navigated to the Configuration / Services / NetServices node in ADSI Edit, I found the DHCPServers attribute on the wds1.iammred.net server. I opened up the string editor for it in ADSI Edit and found that the attribute contained two IP addresses. These addresses are seen here.
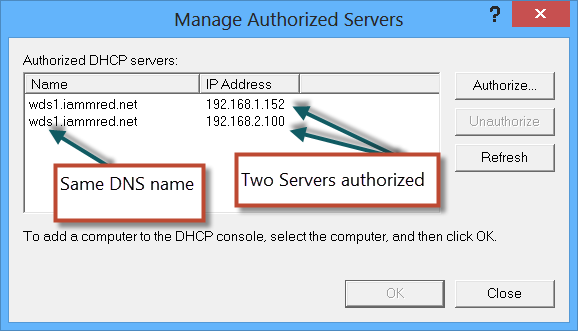
Hmm, this is strange because these are not the IP addresses used on my network. Next, I open the Manage Authorized Servers tool in the DHCP management console, and sure enough, the WDS1 server appears twice with two different addresses. This appears in the following image.
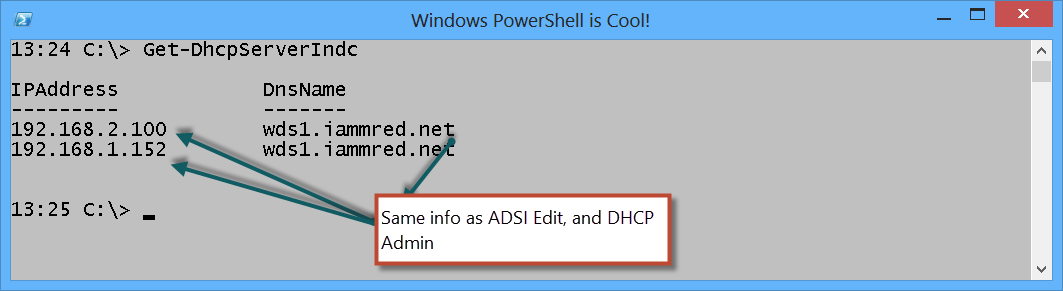
I, once again, returned to the Get-DhcpServerInDC function and typed the command again. The output was still the same (I had done nothing to change it). The output is shown here.
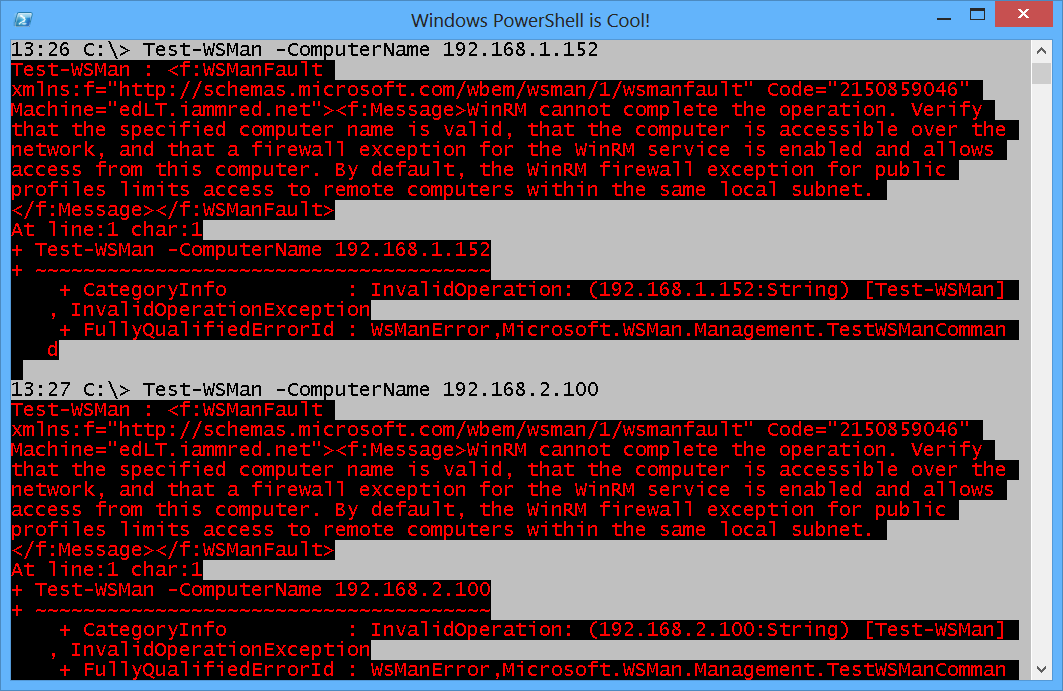
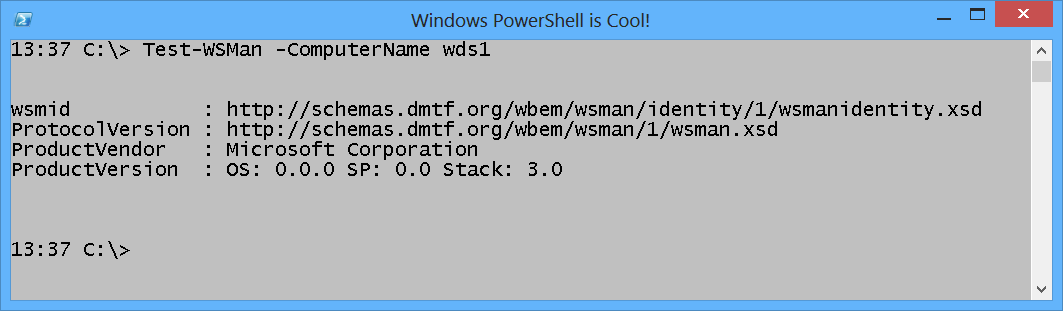
Next, I attempted to use the Test-WSMan cmdlet to check for connectivity to the remote machines. I did this because at times Ping is blocked via the Windows Firewall, but the DHCP server functions all use CIM, and that relies upon the WinRM protocol. As shown here, neither of the IP addresses listed in ADSI Edit accept connections.
Finally, I decided to use Test-WSMan to make the connection via DNS name resolution. The response came immediately back. As appears here, the connection was successful.
Therefore, I decided to unauthorized the server. I ran the Remove-DhcpServerInDC function twice, and I specified the IPAddress parameter both times. This is because, if I run the command with only the DNSName parameter filled out, DNS name resolution is used to resolve the name, and all IP addresses are filled in. But because I had bogus IP addresses registered, I felt the need to specify the IP address. Nothing returns from these commands.
Remove-DhcpServerInDC -DnsName wds1.iammred.net -IPAddress 192.168.1.152
Remove-DhcpServerInDC -DnsName wds1.iammred.net -IPAddress 192.168.2.100
Now I need to add the correct server so it will register in Active Directory. To register the DHCP server in AD DS, I use the Add-DhcpServerInDC function, as shown here.
Add-DhcpServerInDC -DnsName wds1.iammred.net -IPAddress 192.168.0.152
I check it by using the Get-DhcpServerInDC function. This is shown here.
PS C:\> Get-DhcpServerInDC
IPAddress DnsName
——— ——-
192.168.0.152 wds1.iammred.net
If I run the Add-DhcpServerInDC function a second time for a server that is already authorized in AD DS, a warning message appears—but the command also kicks off an authorization check. The command and its output are shown here.
16:03 C:\> Add-DhcpServerInDC -DnsName wds1.iammred.net -IPAddress 192.168.0.152
WARNING: The DHCP server wds1.iammred.net with IP address 192.168.0.152 is already
authorized in Active Directory. The authorization check on the DHCP server has been initiated.
Keep in mind, when viewing the action in the DHCP tool, things move really slow, and it can take several minutes before the arrows change from red (unauthorized) to green. Also, it may take running the Add-DhcpServerInDC a second time—to kick off the second authorization check (at least that was my experience). Of course, first do this in a test environment before you get too carried away on a live network.
Join me tomorrow when I will talk about cool Windows PowerShell stuff.
I invite you to follow me on Twitter and Facebook. If you have any questions, send email to me at scripter@microsoft.com, or post your questions on the Official Scripting Guys Forum. See you tomorrow. Until then, peace.
Ed Wilson, Microsoft Scripting Guy

 Light
Light Dark
Dark
0 comments