Use PowerShell to Document Your Network Configuration
Summary: Learn how to use Windows PowerShell and Active Directory cmdlets to document your Active Directory configuration.
![]() Hey, Scripting Guy! I recently inherited an Active Directory. By this, I mean the network administrator quit. He did not give any notice, and it appears he took any documentation he may have created with him. He may have been abducted by Martians (there seems to be quite a bit of this going on at work) for all I know. Anyway, I need a good way to easily discover information about the domain and the forest. If I could easily print it out, it would be even better. I know how to use Active Directory Users and Computers, and I have been making screen shots, but there should be a better way of doing things. Help!
Hey, Scripting Guy! I recently inherited an Active Directory. By this, I mean the network administrator quit. He did not give any notice, and it appears he took any documentation he may have created with him. He may have been abducted by Martians (there seems to be quite a bit of this going on at work) for all I know. Anyway, I need a good way to easily discover information about the domain and the forest. If I could easily print it out, it would be even better. I know how to use Active Directory Users and Computers, and I have been making screen shots, but there should be a better way of doing things. Help!
—BV
![]() Hello BV,
Hello BV,
Microsoft Scripting Guy Ed Wilson here. I am sorry Martians abducted your network administrator. You did not specify which version of Windows you are running, and you did not say which version of domain controllers you have. I am guessing that perhaps you do not know. To find information about your operating system, you can use the following command in Windows PowerShell:
Get-WmiObject win32_operatingsystem
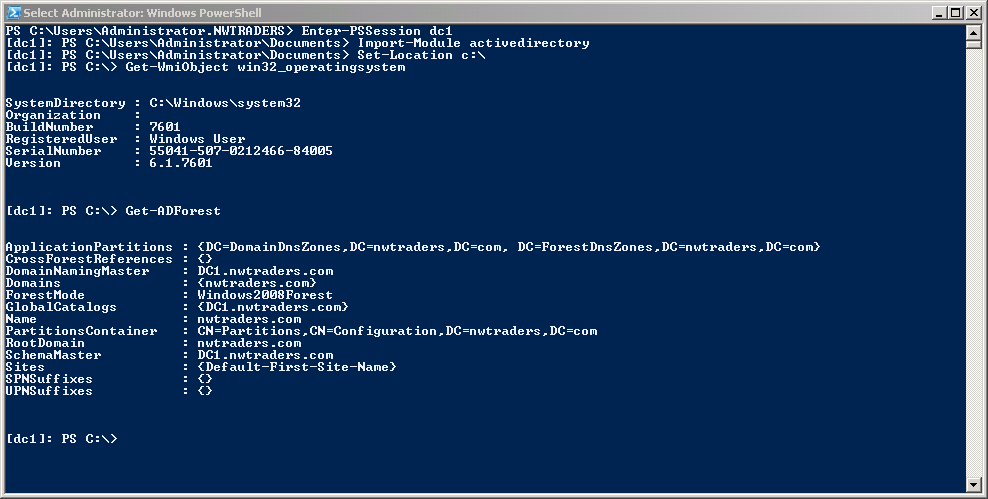
Using the Active Directory Windows PowerShell cmdlets and remoting, I can easily discover information about the forest and the domain. The first thing I need to do is to enter a PSSession on the remote computer. To do this, I use the Enter-PSSession cmdlet. Next, I import the active directory module, and set my working location to the root of the C drive. These commands are shown here:
PS C:\Users\Administrator.NWTRADERS> Enter-PSSession dc1
[dc1]: PS C:\Users\Administrator\Documents> Import-Module activedirectory
[dc1]: PS C:\Users\Administrator\Documents> Set-Location c:\
After I have connected to the remote domain controller, I can use the Get-WmiObject cmdlet to verify my operating system on that computer. This command and associated output are shown here:
[dc1]: PS C:\> Get-WmiObject win32_operatingsystem
SystemDirectory : C:\Windows\system32
Organization :
BuildNumber : 7601
RegisteredUser : Windows User
SerialNumber : 55041-507-0212466-84005
Version : 6.1.7601
Now, I want to get information about the forest. To do this, I use the Get-ADForrest cmdlet. The output from Get-ADForest includes lots of great information such as the domain naming master, forest mode, schema master, and domain controllers. This command and associated output are shown here:
[dc1]: PS C:\> Get-ADForest
ApplicationPartitions : {DC=DomainDnsZones,DC=nwtraders,DC=com, DC=ForestDnsZones,DC=nwtraders,DC=com}
CrossForestReferences : {}
DomainNamingMaster : DC1.nwtraders.com
Domains : {nwtraders.com}
ForestMode : Windows2008Forest
GlobalCatalogs : {DC1.nwtraders.com}
Name : nwtraders.com
PartitionsContainer : CN=Partitions,CN=Configuration,DC=nwtraders,DC=com
RootDomain : nwtraders.com
SchemaMaster : DC1.nwtraders.com
Sites : {Default-First-Site-Name}
SPNSuffixes : {}
UPNSuffixes : {}
The above commands and output are shown in the following figure.
Now I am interested in obtaining information about the domain. To do this, I use the Get-ADDomain cmdlet. The command returns important information such as the location of the default domain controller organizational unit, the PDC emulator, and the RID master. The command and associated output are shown here:
[dc1]: PS C:\> Get-ADDomain
AllowedDNSSuffixes : {}
ChildDomains : {}
ComputersContainer : CN=Computers,DC=nwtraders,DC=com
DeletedObjectsContainer : CN=Deleted Objects,DC=nwtraders,DC=com
DistinguishedName : DC=nwtraders,DC=com
DNSRoot : nwtraders.com
DomainControllersContainer : OU=Domain Controllers,DC=nwtraders,DC=com
DomainMode : Windows2008Domain
DomainSID : S-1-5-21-909705514-2746778377-2082649206
ForeignSecurityPrincipalsContainer : CN=ForeignSecurityPrincipals,DC=nwtraders,DC=com
Forest : nwtraders.com
InfrastructureMaster : DC1.nwtraders.com
LastLogonReplicationInterval :
LinkedGroupPolicyObjects : {CN={31B2F340-016D-11D2-945F-00C04FB984F9},CN=Policies,CN=System,DC=nwtraders,DC=com}
LostAndFoundContainer : CN=LostAndFound,DC=nwtraders,DC=com
ManagedBy :
Name : nwtraders
NetBIOSName : NWTRADERS
ObjectClass : domainDNS
ObjectGUID : 0026d1fc-2e4d-4c35-96ce-b900e9d67e7c
ParentDomain :
PDCEmulator : DC1.nwtraders.com
QuotasContainer : CN=NTDS Quotas,DC=nwtraders,DC=com
ReadOnlyReplicaDirectoryServers : {}
ReplicaDirectoryServers : {DC1.nwtraders.com}
RIDMaster : DC1.nwtraders.com
SubordinateReferences : {DC=ForestDnsZones,DC=nwtraders,DC=com, DC=DomainDnsZones,DC=nwtraders,DC=com, CN=Configuration,DC=nwtraders,DC=com}
SystemsContainer : CN=System,DC=nwtraders,DC=com
UsersContainer : CN=Users,DC=nwtraders,DC=com
From a security perspective, you should always check the domain password policy. To do this, use Get-ADDefaultDomainPasswordPolicy. Things you want to especially pay attention to are the use of complex passwords, minimum password length, password age, and password retention. Of course, you also need to check lockout policy, too. This one is important to review closely when inheriting a new network. Here are the command and associated output:
[dc1]: PS C:\> Get-ADDefaultDomainPasswordPolicy
ComplexityEnabled : True
DistinguishedName : DC=nwtraders,DC=com
LockoutDuration : 00:30:00
LockoutObservationWindow : 00:30:00
LockoutThreshold : 0
MaxPasswordAge : 42.00:00:00
MinPasswordAge : 1.00:00:00
MinPasswordLength : 7
objectClass : {domainDNS}
objectGuid : 0026d1fc-2e4d-4c35-96ce-b900e9d67e7c
PasswordHistoryCount : 24
ReversibleEncryptionEnabled : False
The last major thing to check is the domain controllers themselves. To do this, use the Get-ADDomainController cmdlet. This command returns important information such as is the domain controller read-only, a global catalog server, operations master roles held, and operating system information. Here are the command and associated output:
[dc1]: PS C:\> Get-ADDomainController -Identity dc1
ComputerObjectDN : CN=DC1,OU=Domain Controllers,DC=nwtraders,DC=com
DefaultPartition : DC=nwtraders,DC=com
Domain : nwtraders.com
Enabled : True
Forest : nwtraders.com
HostName : DC1.nwtraders.com
InvocationId : b51f625f-3f60-44e7-8577-8918f7396c2a
IPv4Address : 10.0.0.1
IPv6Address :
IsGlobalCatalog : True
IsReadOnly : False
LdapPort : 389
Name : DC1
NTDSSettingsObjectDN : CN=NTDS Settings,CN=DC1,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=nwtraders,DC=com
OperatingSystem : Windows Server 2008 R2 Enterprise
OperatingSystemHotfix :
OperatingSystemServicePack : Service Pack 1
OperatingSystemVersion : 6.1 (7601)
OperationMasterRoles : {SchemaMaster, DomainNamingMaster, PDCEmulator, RIDMaster…}
Partitions : {DC=ForestDnsZones,DC=nwtraders,DC=com, DC=DomainDnsZones,DC=nwtraders,DC=com, CN=Schema,CN=Configuration,DC=nwtraders,DC=com, CN=Configuration,DC=nwtraders,DC=com…}
ServerObjectDN : CN=DC1,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=nwtraders,DC=com
ServerObjectGuid : 5ae1fd0e-bc2f-42a7-af62-24377114e03d
Site : Default-First-Site-Name
SslPort : 636
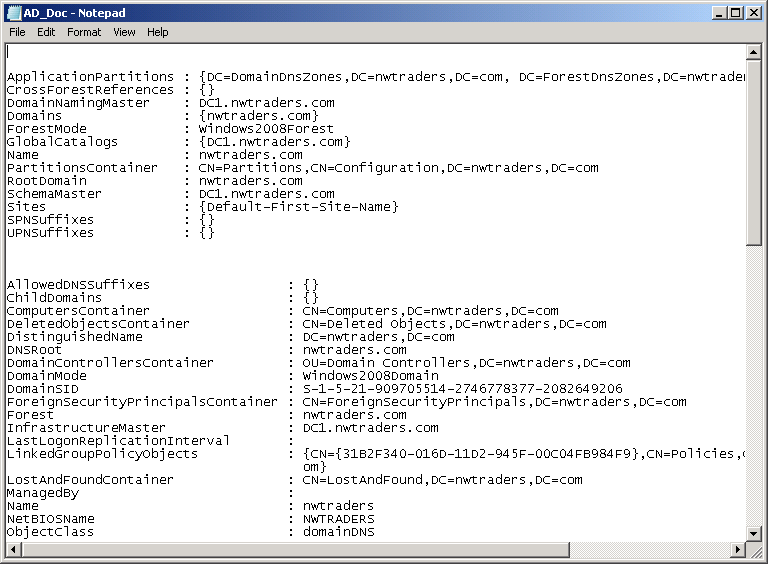
BV, you asked for a report. Now that we know what type of information to expect and how to obtain it, the report is as easy as redirecting the output to a text file. The associated commands are shown here.
Get-ADForest >> \\dc1\shared\AD_Doc.txt
Get-ADDomain >> \\dc1\shared\AD_Doc.txt
Get-ADDefaultDomainPasswordPolicy >> \\dc1\shared\AD_Doc.txt
Get-ADDomainController -Identity dc1 >>\\dc1\shared\AD_Doc.txt
The file as viewed in Notepad is shown here.
Well, that is all there is to quickly documenting a new domain and forest. Join me tomorrow for the quick way to create and manipulate user objects in Active Directory.
I invite you to follow me on Twitter and Facebook. If you have any questions, send email to me at scripter@microsoft.com, or post your questions on the Official Scripting Guys Forum. See you tomorrow. Until then, peace.
Ed Wilson, Microsoft Scripting Guy

 Light
Light Dark
Dark
0 comments