BATCHman Foils the Fowl Ping Win and Repairs the Registry
Summary: In this episode, superhero BATCHman foils the fowl villain Ping Win and repairs the registry.
Microsoft Scripting Guy Ed Wilson here. Today is Episode 5 of the BATCHman series by Sean Kearney.
Note You can read all gripping, engaging, informative, and downright funny BATCHman episodes.
Whenever trouble happens in systems and people will call,
and darkness rolls out causing your fall,
Creatures of bits roam in the night,
Shine to the sky, the bright bluish light,
and call to…BATCHman !
…and, oh yes, his sidekick Boy Blunder Cmdlet, too.
In Today’s Episode, BATCHman Encounters Ping Win
Flying through the night in the new BATCHcopter, BATCHman begins veering off course dramatically.
“Aiaighahighiahgihi!!! My eyes! Such BRIGHT BLUE LIGHT!”
“Holy bluebird of sharpness!” screams Cmdlet. “It’s the BATCHsignal!”
“Yes, Boy Blunder, trouble calls us.” BATCHman calls up the new crime fighting one-liner:
GET-TROUBLE | INVOKE-LAND –location $_.Source
In moments, they are at the scene, the trouble, the issue at hand. It appears that all the firewalls at the Redmond Community Center have been shut down somehow! Home pages have been set to “pingwinrulez.com”! All search queries have been routed to pingwinrulez.com. What dastardly villain would do such a thing?
“Holy earthworm, BATCHman! All of these computers accessed by kids! Surfing whatever they want unprotected! What villain, what creature of the night, who would do.…”
BATCHman taps Cmdlet on the shoulder and points to a rather obvious character off to his left.
Cmdlet looks. “Holy mackerel, BATCHman! It’s the Pin…”
“Ahh, Boy Blunder.” BATCHman taps the side of his nose shaking his head.
“Oh…er…uh…right…it’s…it’s…” Cmdlet stammers staring at the oddly dressed black-and-white flightless fowl-looking person.
The strange character sees the Static Duo. “Meh. Allow me to introduce myself. I am…,” he pauses dramatically before he rips open his jacket, “…PING WIN! Meh heh hehe!”
The words “PING WIN” flash in a mad pulsing fashion, surrounded in blinking lights from a large, very expensive-looking neon sign hanging over his shirt.
BATCHman pauses for a moment, looking. “Ah” is all he can say. He looks at Cmdlet. “Was this really necessary?”
Cmdlet nods. “The blog post went way under budget. We had to burn up some funds. Cool shirt, eh?”
Getting a hold of himself, BATCHman gets back into character. “So Ping Win, you’ve downed all the firewalls, eh? To what end? Why?”
“Antivirus Software! To rid themselves of this problem and all the annoying popups, it will advertise nothing but PingWin-Nev-R-Fayl Antivirus! I will become a trillionaire! Muah har herh hah!”
As Ping Win dances his previctory dance, he trips over one of fifty wires running the neon lights on his shirt and collapses, knocked senseless by his own silliness.
“I thought he’d never shut up!” muttered Cmdlet. “So BATCHman, how do we solve this?”
“How else? With a BATCH file and some Windows PowerShell!” he proudly declares with his hands on the BATCH module belt, standing heroically. First, we must ensure the firewall service is started on all of these systems. We will get the status of it using the Get-Service cmdlet.”
GET-SERVICE “Windows Firewall”
“We can see on this machine that it’s stopped.”
“To restart it, we can pipe it into the Start-Service cmdlet.”
GET-SERVICE “Windows Firewall” | START-SERVICE
Cmdlet is rapidly opening up his copy of PowerGUI to begin building the script for rapid deployment.
“Now,” he mumbled as he gnawed on his cape, “to reset those home pages. Need to get this done fast.”
For a moment, he eyed a large cache of energy drinks and pictured Cmdlet running about like a gerbil clicking away on GUI options. He smiled.
“Nah! Let’s use the registry!” he thought aloud. “So to change these home pages and how he’s redirected the search, we’ll need to directly access the registry for each user. The settings we need are all under this key.”
“HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\”
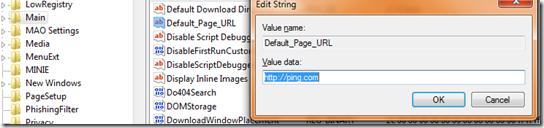
Using Regedit, BATCHman shows Cmdlet an example of what Ping Win had done.
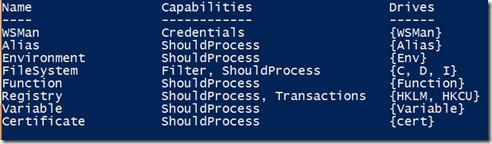
“And there are three values we need to fix: Start Page, Search Page, and possibly even Default_Page_Url. As you can see, Cmdlet, he’s modified Default_Page_Url to point to his own private dastardly site. But we can easily access the registry using Windows PowerShell. We can access the registry using a built-in provider. To get the list of available providers, we simply type this.”
GET-PSPROVIDER
“Holy convenience store, BATCHman! HKCU is marked as a drive! Do you mean if I were to type SET-LOCATION HKCU:, I would be navigating the registry?”
“Not only that but if you ran a GET-CHILDITEM against it, you would see that part of the registry: GET-CHILDITEM HKCU: Or we can even recurse: GET-CHILDITEM HKCU: –recurse.”
Cmdlet pauses in thought. “So to access the available registry keys for HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\ all I have to do is enter:
GET-CHILDITEM HKCU:\Software\Microsoft\Internet Explorer\Main\
BATCHman smiled. “Close, my little digital partner, but not quite. You would need to execute a GET-ITEM because that is how the registry tree branches are recognized by Windows PowerShell. The CHILDITEMs in this case are actually just other available branches under HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\. To see what is attached to the main branch, we type this.”
GET-ITEM HKCU:\Software\Microsoft\Internet Explorer\Main\
“And that shows us it has Properties attached to it.”
“To access and see what values are available under the main branch, we need only attach the property name, which oddly in this case is called Property, to the original line in Windows PowerShell.”
(GET-ITEM HKCU:\Software\Microsoft\Internet Explorer\Main\).Property
“Now if we need to pull down the values of a PROPERTY from an ITEM in the registry, we do this.”
GET-ITEMPROPERTY –path “Registry::HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main“
Cmdlet blinked as he saw all the registry values from the Main key appear on the screen. “Holy Bee Hive!” he muttered.
“Now of course if we need to see a particular value, such as say Default_Page_Url, we type this.”
GET-ITEMPROPERTY –path “Registry::HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main“ –name “Default_Page_Url”
“But BATCHman, you’ve forgotten the most important part! We need to fix them and fix them now! Kids are due to arrive in minutes!”
BATCHman realized he got a little too carried away in chatting about Windows PowerShell and had almost forgotten the task at hand. “Yes! Of course! So all we need to do to set the value in a key.”
SET-ITEMPROPERTY –path “Registry::HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main“ –name “Default_Page_Url” –Value “http://www.msn.com”
Cmdlet looked and took the initiative. “So for the remaining keys to put in some proper values, I need only do this?”
SET-ITEMPROPERTY –path “Registry::HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main“ –name “Start Page” –Value “http://www.msn.com”
SET-ITEMPROPERTY –path “Registry::HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main“ –name “Search Page” –Value “http://www.bing.com”
“Exactly! Now let’s save this script and try it on a machine!”
“But BATCHman! We need to alter their personal settings as well! How will we do that easily? And quickly?! We only have moments before the center opens!”
BATCHman thought about it. How to alter those settings automatically with this script? “Of course!” his fingers snapped, sending shockwaves. “We’ll use Group Policy and set it as a startup script! As they log in, it will overwrite all the mess Ping Win turned loose!”
BATCHman quickly navigated to the computer configuration and dropped in a reference to his script in the SYSVOL share. Soon, people began to arrive. They logged in. Nobody noticed anything odd.
Ping Win began to recover from his trip over the chords. He looked. No disgusted reactions. Happy people. “Meeeeeea! FOILED!” he screamed and fell over another power cord.
“Cmdlet,” the BATCHman said watching Ping Win “Next time, let’s avoid buying the arch villain a big neon sign he can trip over. We could have spent that money on tires for the WinMobile”
Sean, thanks for another awesome episode of BATCHman. Everyone, join us tomorrow for Episode 6.
I invite you to follow me on Twitter and Facebook. If you have any questions, send email to me at scripter@microsoft.com, or post your questions on the Official Scripting Guys Forum. See you tomorrow. Until then, peace.
Ed Wilson, Microsoft Scripting Guy



 Light
Light Dark
Dark
0 comments