Remote support solution for high secure Workstations
This post is completely unrelated to all the other usual topics on this blog. But as it is related to management and might help some people I want to share this solution.
Scenario & Challenge
A lot of customers are using high secure Workstations (or Privileged Access Workstation (PAW) as we call it). These workstations may run Windows or Linux and are usually completely locked down and have no Internet access. They are used to access highly secure environments (like AD Domain Controller and other Tier 0 systems e.g.).
What if you have an issue in this environment and need vendor support (like Microsoft Support)? Giving an Engineer remote access or at least share the screen with him will usually solve issues much faster than sending log files and screenshots back and forth.
But with a high secure Workstation, that is usually impossible due to the security restrictions...
Solution
Today I was on a customer site in the exact same situation. PAW, no Internet access whatsoever, completely locked down and an urgent support case with a colleague in India waiting to have a look at the issue in real time.
Fortunately the customer was quite clever and found a solution for it, which I am allowed to share with you:
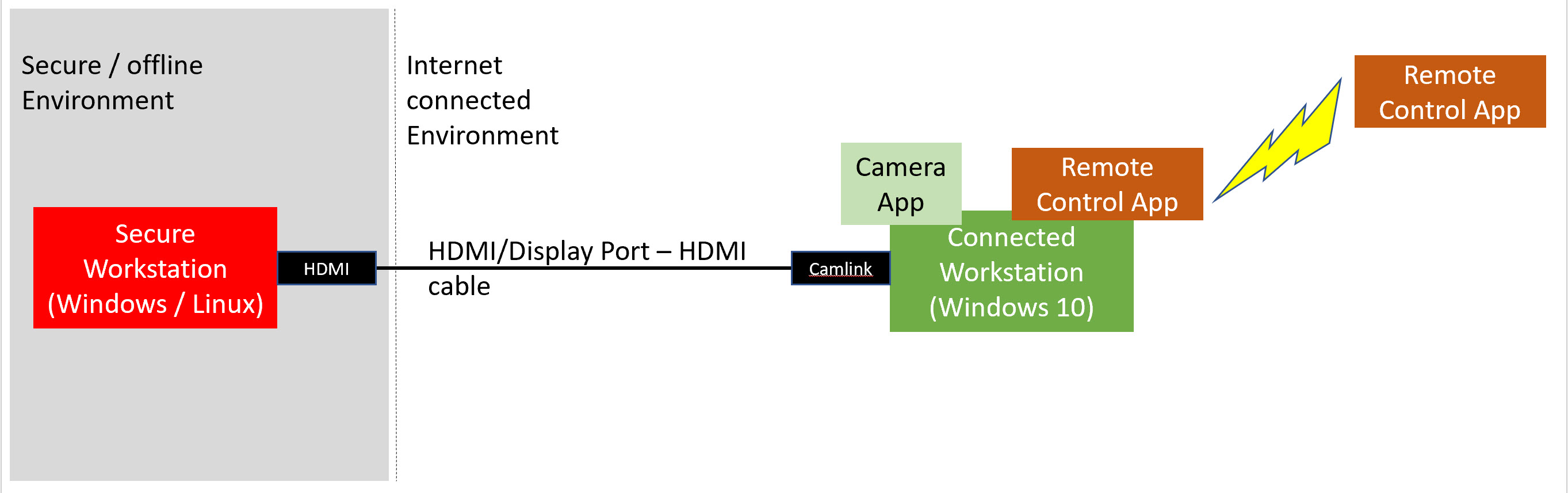
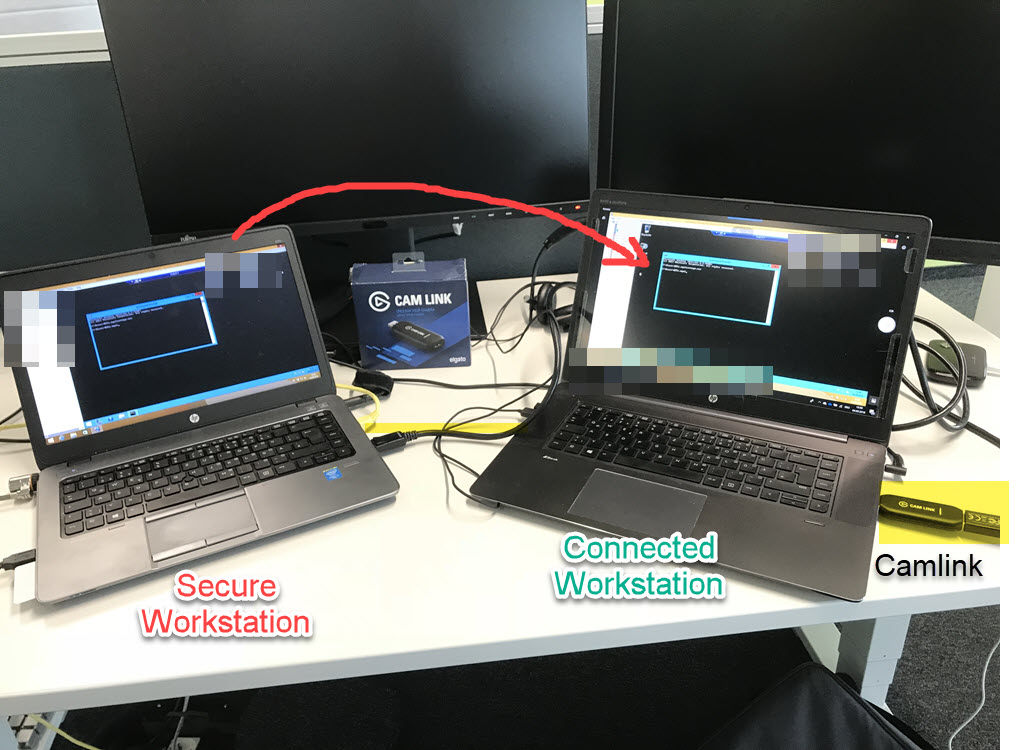
The customer found a device (Elgato Camlink), that is usually used to take high resolution screenshots for Gaming. You connect this device to your connected workstation (unsecure, Tier 2). It does not require any driver installation on Windows 10 and gets installed as a Camera device.
The other end of the Camlink device gets connected to the secure Workstation via HDMI cable. On the secure Workstation, the Camlink appears as a second screen and does not require any drivers to be installed also!
Once you did the cabling, you simply duplicate your screen on the secure Workstation and open up the Camera App on Windows 10 to see the live stream! You can then share the Camera App with the remote Support engineer.
Isn't that a neat solution?
You can share the screen without compromising the security of your secure workstation and your secure environment. No Admin rights are required and nobody can control the secure workstation, even if the connected workstation has been compromised...