[技术分享 – ISA 篇] 20100630 - 2, 网卡相关四不要 - 网络设置篇
不要在单网卡的 ISA 上设置外部网络。
对于单网卡的 ISA 而言,所有网段 (除了本机网络) 都会被看作是内部网络。如果设置外部网络,不符合 ISA 的网络逻辑,会造成意想不到的问题,影响正常访问。只在单网卡的 ISA 上设置缺省的内部网络,建议使用 Add Adapter 来进行添加。
参考
Configuring ISA Server 2004 on a Computer with a Single Network Adapter https://technet.microsoft.com/en-us/library/cc302586.aspx
- Multi-network firewall policy. In single network adapter mode, ISA Server recognizes itself (the Local Host network). Everything else is recognized as the Internal network. There is no concept of an External network. Microsoft Firewall service and application filters operate only in the context of the Local Host network. (ISA Server protects itself no matter what network template is applied.) Because the Firewall service and application filters operate in the context of the Local Host network, you can use access rules to allow non-Web protocols to the ISA Server computer itself.
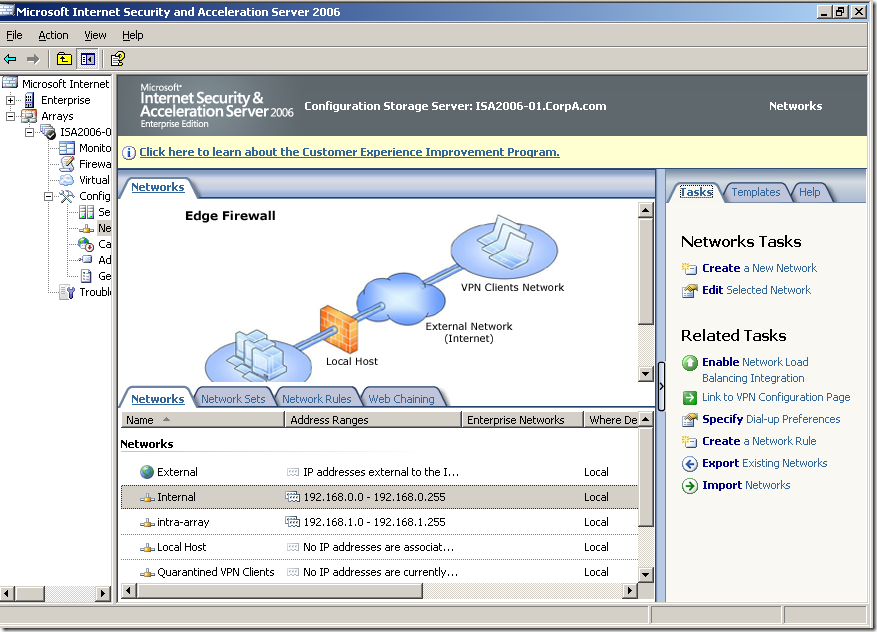
不要在多网卡的 ISA 上随意删改添加 ISA 的网络,或者自行创建新的网络。
ISA 对网络的识别和划分是跟据 ISA 上对应的网卡来自动识别和划分的。如果随意自定义 ISA 的网络,或者自行创建新的网络,会造成路由的冲突与访问的问题。在多网卡的 ISA 上设置网络时,请使用 Add Adapter 来进行添加,这样添加的网段与 ISA 的网卡和路由一致,不会造成问题。注意每个物理网卡只能对应一个 ISA 网络。
参考
Network Concepts in ISA Server 2006
https://technet.microsoft.com/en-us/library/bb794774.aspx
- A network adapter can have zero or more addresses, and only be associated with one ISA Server network, so that each address only belongs to a single network. There should be no overlap of address ranges on a network.
- If you create a custom Internal or perimeter network, you must have an adapter installed to associate with the new network. For example, if you have an ISA Server computer with two network adapters, one connected to the Internet, and the other connected to the Internal network, you will need a third network adapter to define a perimeter network.
- All IP addresses that can be reached directly from a network adapter must be defined as part of the same ISA Server network. To ensure that remote subnets that are reachable by ISA Server through a router are correctly configured:
- Be sure that remote subnets are added correctly to the network definition for the adapter where that traffic will be received.
- Verify that the network's IP address range matches the routing table, and that routes are defined in the routing table for each remote subnet.
Cherry Qian, James Yi
微软安全支持专家