How to see the IP addresses from where your Office 365 users are accessing their mailbox
In our support experience we had multiple cases where customers wanted to know the IP address from where some of their users have logged in to Outlook Web App or in Outlook client. In the past, this kind of information could not be retrieved from the Office 365 side and only the customers with an Azure subscription had access to these details.
UPDATE:
As per the last news, we will enable mailbox auditing by default in the near future, for all cloud mailboxes.
So the steps below from 1 to 3, to enable mailbox auditing for mailbox login events, will not be needed, once the auditing will be enabled automatically for all Office 365 mailboxes: https://techcommunity.microsoft.com/t5/Security-Privacy-and-Compliance/Exchange-Mailbox-Auditing-will-be-enabled-by-default/ba-p/215171
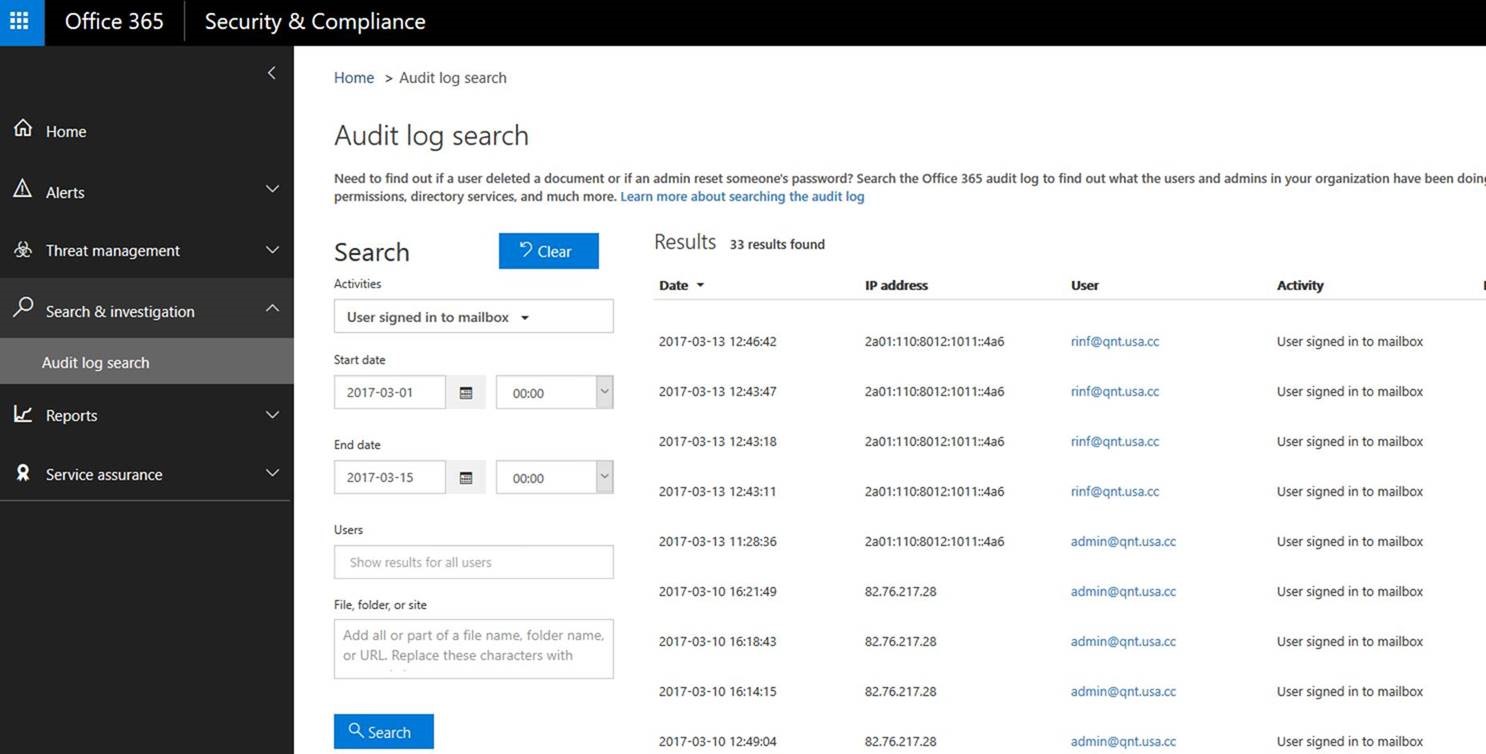
Now this information can be retrieved from new Office 365 Compliance Center(https://protection.office.com) , from the Audit log search, under “Search and Investigation” section.
In order to be able to see the connecting IP address for your users, you have to follow next steps:
1. First you need to enable company auditing from Compliance Center. For this step you can find guidance in the next article:
2. Since the activity that you need to look for is called “User signed in to mailbox” and it is a mailbox activity, this requires to enable mailbox auditing for that user from Exchange Online:
You can do this via PowerShell, using below command:
Set-Mailbox -Identity user@domain.com-AuditEnabled $true
3. At the same time “User signed in to mailbox” action is a mailbox owner activity. In Exchange Online, even if you enable mailbox auditing, this does not mean that all the activities from that mailbox will be recorded.
Mailbox auditing has 3 types of recorded activities levels, which can be seen with below command:
$FormatEnumerationLimit = -1
Get-Mailbox user@domain.com |fl *audit*
AuditEnabled : true
AuditLogAgeLimit : 90.00:00:00
AuditAdmin : {Update, Move, MoveToDeletedItems, SoftDelete, HardDelete, FolderBind, SendAs, SendOnBehalf, Create}
AuditDelegate : {Update, SoftDelete, HardDelete, SendAs, Create}
AuditOwner : {}
As you can notice, by default, we have no action recorded for AuditOwner .
So if you need to record the user login activity, you can easily do it with below command:
Set-Mailbox user@domain.com -AuditOwner MailboxLogin
Please refer to below article for more details about what kind of actions you can audit in Exchange Online and about how to enable the auditing for them:
https://technet.microsoft.com/en-us/library/dn879651.aspx
4. Once you finished this setup for each user that you want to audit, you should perform the search from Compliance Center. Please be aware that auditing will record only the actions that were performed after the moment you enabled it, as per above procedure.
The result should be similar to the one from picture below :