Basic spam troubleshooting in Office 365
When talking about Spam we can define just two scenarios:
False-Positive – Valid emails are seen as spam by Office 365
False-Negative – Spam emails are delivered into my Inbox folder.
Note please that I said Inbox folder, as spam emails that are delivered into the Junk folder or to Exchange Online Protection hosted Quarantine, is expected behavior.
So let’s take each scenario and see what is the basic troubleshooting.
False-Positive Spam
I will discuss here from the perspective of an Office 365 customer who sends a valid email, but Exchange Online Protection mark it as spam.
Why this scenario? Because if you are receiving valid emails but they are seen as spam, the solution is simple
If you trust it, whitelist the domain, sender or IP on your tenant How to whitelist?
So let’s consider the below scenario.
- user@contoso. com is hosted in Office 365.
- He sends an email to another Office 365 user, user@fabrikam.com
- Emails are ending up into the Junk Folder of user@fabrikam.com
Of course user@fabrikam.com can whitelist contoso.com domain, but we cannot ask all the Office 365 users to whitelist this domain.
How will we know why the emails are marked as spam?
Troubleshooting
Obtain an exact sample of the message from user@fabrikam.com Junk Folder
- Open the user@fabrikam.com mailbox from the Outlook client
- Double Click on the affected email message
- Click on FILE, then click on SAVE AS
- Make sure to choose .MSG for the file type
- Save the file to a folder on the desktop (eg. Samples). More details can be found here
Note: You can also obtain the sample from user@contoso.com Sent Items folder, but you will not have the message header. To see the EOP spam score you will need to perform and Advanced Message Trace for the affected message.
Open the message and go to File | Properties.How to view the message properties?
Open the Microsoft Remote Connectivity Analyzer website, and go to Message Analyzer
Copy all properties of the message and paste into the Message Analyzer
Click on Analyze Headers
The most relevant fields from the Header will be:
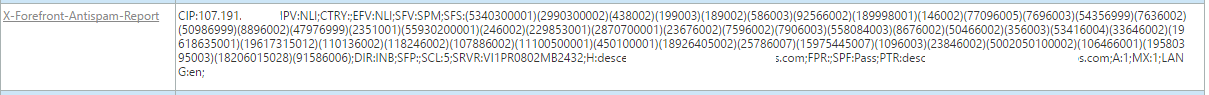
Authentication-Results and Received-SPF 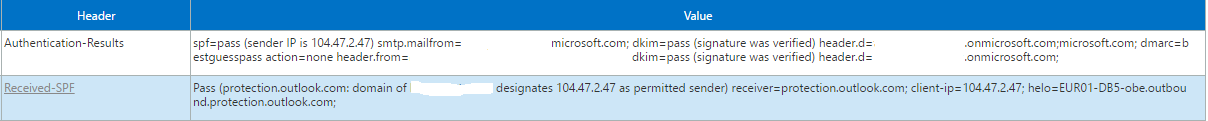
It will tell us if the SPF, DMARC or DKIM passed. It is important because:
- If SPF will Fail the emails will be seen as SPAM. More details here
- If DMARC is failing and has the Action is p=reject or p=quarantine, they will be seen as SPAM. More details here
- If DKIM fails, depending of each customer own rules, it could be marked as SPAM
X-Exchange-Antispam-Report-Test 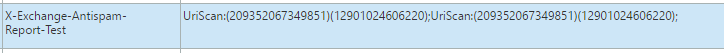
This header is very important because it will tell us that the email contained URLs.
As EOP uses 3rd Party URL blocking lists, then it is a must that you check each URLs from the email on these lists.
Check the EOP 3rd Party blocking lists on the Partner block list section
Note: It is possible that an email will have hidden links, inside the HTML code of the email.
You can view the html code by following the below steps.
- Right-click inside the email message.
- Select "View Source" from the drop-down menu.
- A window will open showing the header information of the selected message.
Very important as this will tell us why the email was seen as SPAM.
Let’s analyze this header then.
- The email was seen with SFV:SPM, meaning by content.
- Was marked as spam when it entered in EOP ,DIR:INB.
- It got a low spam score SCL:5
If the email would have got SCL 6, and SFV:BLK , then user@contoso.com it is in the individual blocking list of user@fabrikam.com
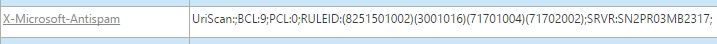
What are important from this field are BCL and PCL.
BCL - The Bulk Complaint Level (BCL) of the message. For more information, see Bulk Complaint Level values.
Why is this important?
By default, each tenant has the Bulk threshold, in the Spam Filter Policy, set to 7. This means that each message having a BCL equal or greater than 7 will be marked with SCL 9.
PCL - The Phishing Confidence Level (PCL) of the message, which indicates whether it’s a phishing message or not.
Why is this important?
The PCL values, which are from 0 to 8, will be used to determine what action your email client takes on messages. For example, Microsoft Office Outlook uses the PCL stamp to block the content of suspicious messages.
X-CustomSpam - The message matched an advanced spam filtering (ASF) option.
A detailed explanation of all the headers mentioned above, can be found here.
If you have reviewed and completed all the above steps, but cannot find a valid reason, then most likely some words or phrases from the email are the cause.
In this case you will need to open a case to Microsoft. To make sure that your case will be handled properly and in a timely manner then you need to make sure that:
- You have submitted the affected samples to Office 365 as Not Junk. Submit spam to Office 365
- You have in your possession the original affected samples. Exactly as described on Step I from Troubleshooting.Note: The samples should not be more than two days older.
- The samples are archived in ZIP format.
Very important because if you will send them to Microsoft in MSG format over the email, all the AntiSpam headers will be removed
An engineer will review the samples and if he will not find a valid reason for the emails to be marked as SPAM, then he will engage the AntiSpam team to review the samples
Note: If the emails are delivered to the EOP Hosted Quarantine, then you will need to follow the below steps to get the message header, before they are released.
- Connect to Office 365 Admin Center | Exchange | Protection | Quarantine
- Click on the quarantined email
- On the right panel click on “View message header...” How to view message header from Quarantine?
- Copy the content and Paste it into a TXT file
- Release the message and save the sample following the previous instructions
False-Negative
Very hard to be caught especially in the scenarios were the MX is not pointing to EOP, but to your on-premise server or 3rd party filtering solution.
Why?
Because EOP is using its own sender reputation lists and also 3rd party reputation list.
When the MX is pointing to yours on-premise server (or 3rd party) and after routed to the Office 365 hosted mailbox, then the email will be seen coming from yours servers and not the actual sender (spammer in this case).
This behavior is described here.
If you are in this situation, then you are practically bypassing the EOP anti-spam filters, and an investigation will be impossible.
Why?
Because EOP is not blocking your own servers as being SPAM, in a normal scenario.
Also most spammers will use words and patterns in the email that will look as legit.
Like:
Hi,
Please check this new stuff that I bought. www.fabrikam.com
Thanks,
My question to you is how will you block this, if not by IP reputation?
So, how can we protect agaist spams?
Troubleshooting
First you need to identify which type of SPAM are you receiving.
- Is your domain being spoofed? Meaning the emails seems to come from users inside your organization?yesBlock Spoofing in Office 365Spoof Attacks in Office 365 Webcast
- If
- , please refer to the below articles on how to protect.
- Are you receiving bulk emails, such as marketing campaigns?yesHow to create more aggressive Bulk email settings in Exchange Online?Use transport rules to configure bulk email filtering
- If
- , then check the below articles on how to protect yourself against them.
- Are you receiving, phishing emails, where someone pretending to be your customer is asking for money?yesWhy does spam and phishing get through Office 365?How to review and mitigate the impact of phishing attacks in Office 365?
- If
- , then check the below articles on how to protect yourself against them.
- Are you the subject of an NDR storm?yesOffice 365 NDR Backscatter protection Note: In case you are subject to an aggressive NDR storm and you cannot use the affected mailbox, then you should consider to either redirect the emails to a Shared Mailbox, or temporarily remove the SMTP address.
- If
- , then check the below article on how to protect yourself against it.
If you have reviewed and completed all the above steps, but still you are subject of aggressive SPAM, then you can open a case to Microsoft.
To make sure that your case will be handled properly and in a timely manner then you need to make sure that:
- You have submitted the affected samples to Office 365 as Junk. Submit spam to Office 365
- You have in your possession the most recent original affected samples. Exactly as described on Step I from the False-Positive scenario.Note: The samples should not be more than two days older.
- The samples are archived in ZIP format.
Very important because if you will send them to Microsoft in MSG format, all the AntiSpam headers will be removed. - An engineer will review the samples and if necessary, he will engage the AntiSpam team for further assistance