Tip o' the Week 371 – Enabling 2FA for MSA
Passwords are going out of fashion – they’re too easy to guess or hack. We now have a variety of ways to unlock our phones or sign in to services we use, from biometrics to certificates, or even a mixture of methods including behaviours. When you have a username & password, there are two things you need to know but it’s not inconceivable you could lose one or both by being coerced or tricked into action you didn’t expect. Using a mixture of “something you know” (like a username & password) and “something you have” (like a physical token or maybe something on your phone) , including even “something you are” (like your face, voice or fingerprint), is arguably more secure, since needing several “factors” means it’s harder for a potential baddy to steal your credentials and impersonate you. With identity theft becoming an ever-present problem, anything you can do to tighten access to commonly-used applications should be considered. Multi-factor authentication (MFA) is the umbrella term for using a combination of several means of authentication, but commonly used scenarios are often just 2FA or two-factor authentication. Twitter, for example, launched 2FA via text to your phone – meaning you need a username/password, the phone number you’ve already registered, and the one-time message they just sent you, to log in. It’s easily possible to enable 2-factor authentication for your Microsoft Account, ie. the credentials you might use to log in to apps on Windows 10, Outlook.com/MSN/Hotmail, Azure Portal etc.
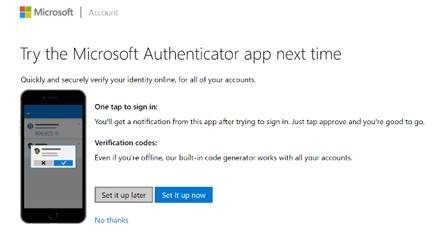
Older devices (like Xbox 360) or older software may not have awareness of 2FA, in which case a specially-created “app password” is required. More recent apps which recognise MSA authentication should support the Authenticator App (available for Windows, iOS and Android) .
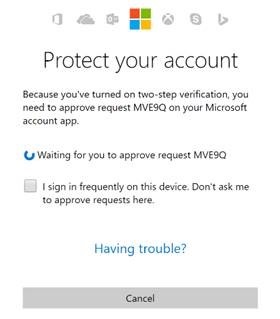
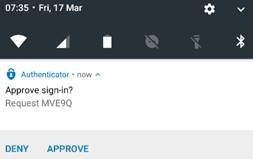
If you check the “sign in frequently” box on the prompt within the app or service (before tapping APPROVE on your phone) , this phone notification will be a periodic or even one-time option – invoked when you’re setting up a new app or access to a service from a new device like a shared computer. It’s easy enough to turn off two-step verification if you don’t like it, and frankly, the first few hours after switching it on might make you feel you’ve made a big mistake – but the blizzard of authentication requests soon dies down and it becomes an occasional thing you need to do, but you’re safe in the knowledge that your Microsoft Account is a little more protected from hackers. |