Best Practices for Finding Executable Content
UPDATE (October 14, 2016): We now recommend using the Common Attachment Types Filter to block file types as opposed to using transport rules. Take a look at my updated post, Common Attachment Types Filter, for more information on this new filter.
This article may be common knowledge for some, but it is important to revisit and refresh ourselves on. You may be aware of what content EOP will flag as being executable, or you may not. In either case, I think this is an important topic so sit back, relax, and read on.
Transport Rules
One of our best practices is to create a transport rule which blocks executable content. This would look as follows. 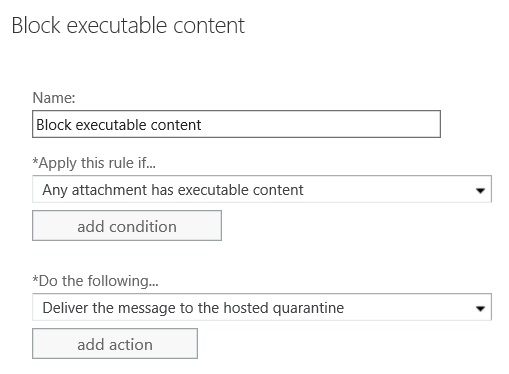
The reason we suggest creating this rule is that it acts as a second line of defense for catching zero day malware. If a zero day attack is missed by the EOP malware filters but is being delivered in the form of an executable attachment, this rule will stop those messages from reaching your end users.
The beauty of this transport rule predicate is that it will also catch executable files that have had their extensions renamed. For example, if the file notavirus.exe is renamed to notavirus.txt and attached to an email, this transport rule will still fire.
If you instead created a transport rule with the predicate, Any attachment’s file extension matches… 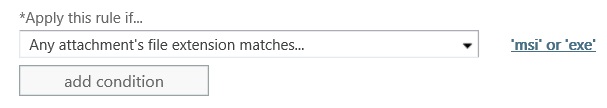
This transport rule WOULD NOT fire if a file with a matching extension has its extension renamed. With this rule, if the executable notavirus.exe was renamed to notavirus.txt, this rule would not fire. This predicate should only be used to block extensions that do not fall under what we consider “executable content.”
What is considered an executable?
What EOP considers as executable is nicely documented on TechNet, however it is a little buried. The list of file types can be found on the TechNet page Using transport rules to inspect message attachments. Scroll to the bottom of this article and look for the table under the heading Supported executable file types for transport rule inspection.
To save you a click, the current list is as follows.
| Type of file | Native extension |
| Self-extracting archive file created with the WinRAR archiver. | .rar |
| 32-bit Windows executable file with a dynamic link library extension. | .dll |
| Self-extracting executable program file. | .exe |
| Java archive file. | .jar |
| Uninstallation executable file. | .exe |
| Program shortcut file. | .exe |
| Compiled source code file or 3-D object file or sequence file. | .obj |
| 32-bit Windows executable file. | .exe |
| Microsoft Visio XML drawing file. | .vxd |
| OS/2 operating system file | .os2 |
| 16-bit Windows executable file. | .w16 |
| Disk-operating system file. | .dos |
| European Institute for Computer Antivirus Research standard antivirus test file. | .com |
| Windows program information file. | .pif |
| Windows executable program file. | .exe |
If your transport rule is set to look for Executable Content, the above file types will cause the rule to trigger even if their extension is renamed.
Last Words
I mentioned above that one of our best practices is to create a transport rule which will trigger on executable content. I would highly recommend this, along with other great best practices can be found on the TechNet page Best practices for configuring EOP. This page also lists other file extensions that you may wish to block through a transport rule that looks at an attachments extension (see the section Extension Blocking).
Resources
Using transport rules to inspect message attachments Best practices for configuring EOP