Installing DHCP on Windows Server 2012 did not create the local groups
Hi again,
Another interesting case with a nice, easy solution.
While working with a Premier customer recently we found that the 2 local groups relating to DHCP, “DHCP Administrators” and “DHCP Users” didn’t get created on their new DHCP servers.
Only the role installation steps can do this for us as that will make sure they were actually given the required rights to manipulate or view the service.
What to do?
We couldn’t just remove and reinstall the role – there was too much configuration already done.
We couldn’t ignore it as we were installing IPAM and it needs to place the IPAM servers computer account into the group “DHCP Users” on the servers. It does this by nesting itself into new a universal group in the domain: IPAMUG. This group is the one which actually becomes a member of the “DHCP Users” group.
The role was installed by a “next-next” manual installation using Server Manager. So it wasn’t as if some PowerShell or DISM.exe switch was accidentally left off. And if we repeated the manual installation, we would likely just end up where we started.
What went wrong?
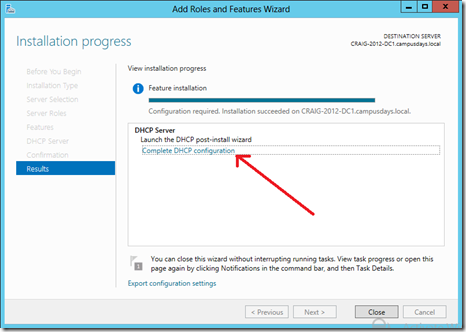
At the end of the Server Manager wizard, you get this completion message (without the big red arrow, that’s my addition).
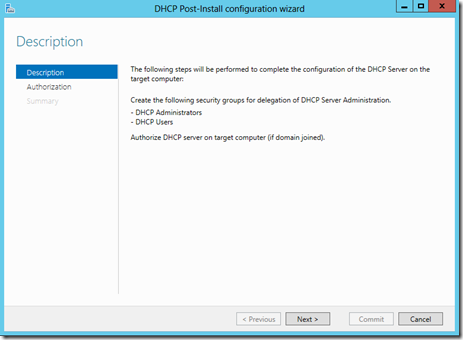
Inside there is a link to launch a wizard which will configure the DHCP server, called “Complete DHCP configuration”. This wizard does 2 things:
- It creates the 2 groups we’re after: “DHCP Administrators” and “DHCP Users”
- It authorizes the DHCP server in Active Directory if the DHCP server is joined to a domain
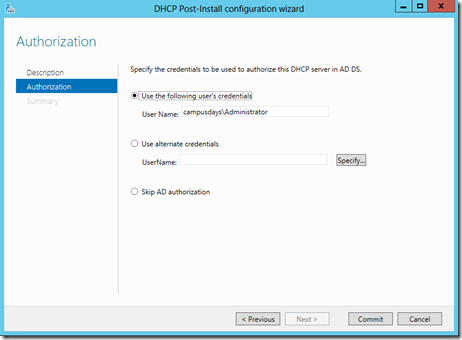
The authorization part is pretty nifty. Usually you do this by right-clicking on the server in the DHCP MMC console and selecting “Authorize”. This will create a object in the Configuration partition of the Active Forest under Services / NetServices for the DHCP server. Only members of Administrators in the forest root domain or members of Enterprise Admins can create objects here. The new wizard lets you type alternate credentials to do this job:
My customer had authorized their DHCP servers, by doing it the old way in the DHCP MMC console using an account with permission to do so.
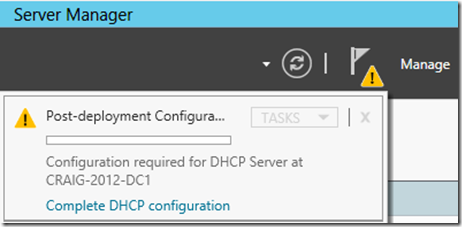
They hadn’t noticed that small blue link from the image above. There is also a outstanding notification within any Server Manager console which connects to one of these DHCP servers (or on the local host itself). But that was also quiet subtle, and requires that you click on it to see the same blue link:
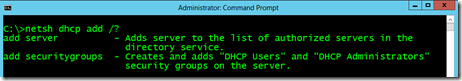
In fact, we hadn’t even noticed any of this by the time I’d found an alternative way of creating these groups on their DHCVP servers using netsh.exe:
netsh.exe dhcp add securitygroups
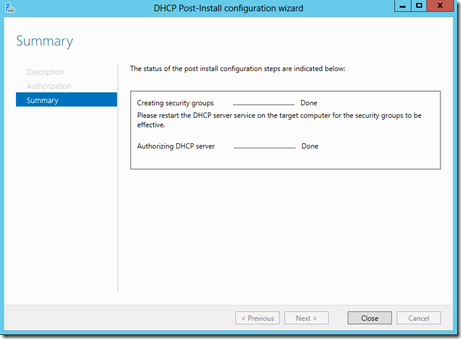
Had we run the wizard through to it’s completion, we would have got a success message like this stating that the local groups were successfully created:
I hope this helps someone avoid some troubleshooting time when deploying DHCP on Windows Server 2012.