Secure Your Office 365 Tenant – By Attacking It (Part 2)
By David Branscome
In my previous post (https://blogs.technet.microsoft.com/cloudyhappypeople/2018/04/04/secure-your-office-365-tenant-by-attacking-it ), I showed you how to use the Office 365 Attack Simulator to set up the Password Spray and Brute Force Password (Dictionary) Attacks.
What we often find, though, is that spear phishing campaigns are extremely successful in organizations and are often the very first point of entry for the bad guys.
Just for clarity, there are “phishing” campaigns and there are “spear phishing” campaigns.
A phishing campaign is typically an email sent out to a wide number of organizations, with no specific target in mind. They are usually generic in nature and are taking the approach of “spreading a wide net” in hopes of getting one of the recipients to click on a URL or open an attachment in the email. Think of the email campaigns you’ve likely seen where a prince from a foreign country promises you $30 million if you’ll click on this link and give him your bank account information. The sender doesn’t particularly care WHO gets the email, as long as SOMEBODY clicks on the links.
On the other hand, a spear phishing campaign is much more targeted. In a spear phishing campaign, the attacker has a specific organization they are trying to compromise – perhaps even a specific individual. Maybe they want to compromise the CFO’s account so that they can fraudulently authorize money transfers from the organization by sending an email that appears to be coming from the CFO. Or maybe they want to compromise a highly-privileged IT admin’s email account so that the attacker can send an email asking users to browse to a fake password reset page and harvest user passwords. The intent with a spear phishing campaign is to make the email look very legitimate so that the recipients aren’t suspicious – or perhaps they even feel obligated to do as instructed.
What Do I Need?
As you can imagine, setting up a spear-phishing campaign takes a little more finesse than a brute force password attack.
First, decide WHO the sender of the spear phishing email will be. Maybe it’s HR requesting that you log in and update your benefits information. Or perhaps it’s the IT group asking everyone to confirm their credentials on a portal they recently set up.
Next, decide WHO you want to target with the campaign. It may be the entire organization, but keeping a low profile as an attacker also has its advantages.
You’ll probably want to use a realistic HTML email format so that it looks legitimate. The Attack Simulator actually provides two sample templates for you, as we’ll see below. Using the sample templates makes the campaign very easy to set up, but as you get more comfortable using the Attack Simulator, you will likely want to craft your own email to look more like it’s coming from your organization.
That should be enough to get us started.
Launching a Spear Phishing Attack
In the Attack Simulator console, click on “Launch Attack”.
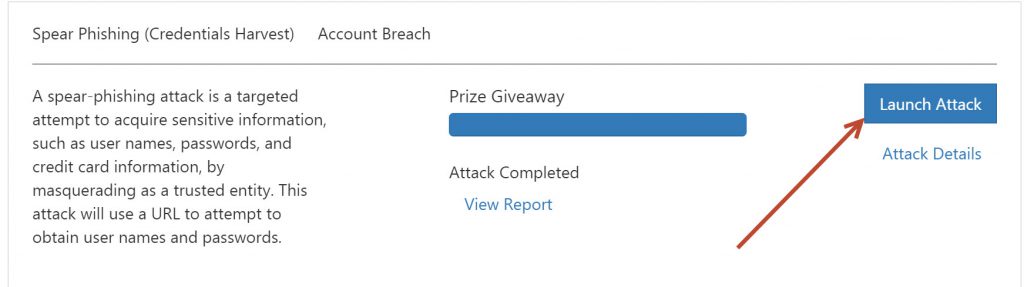
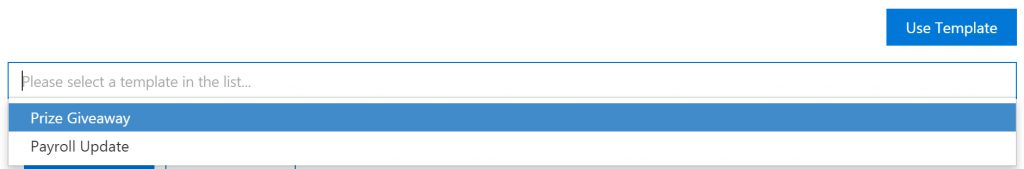
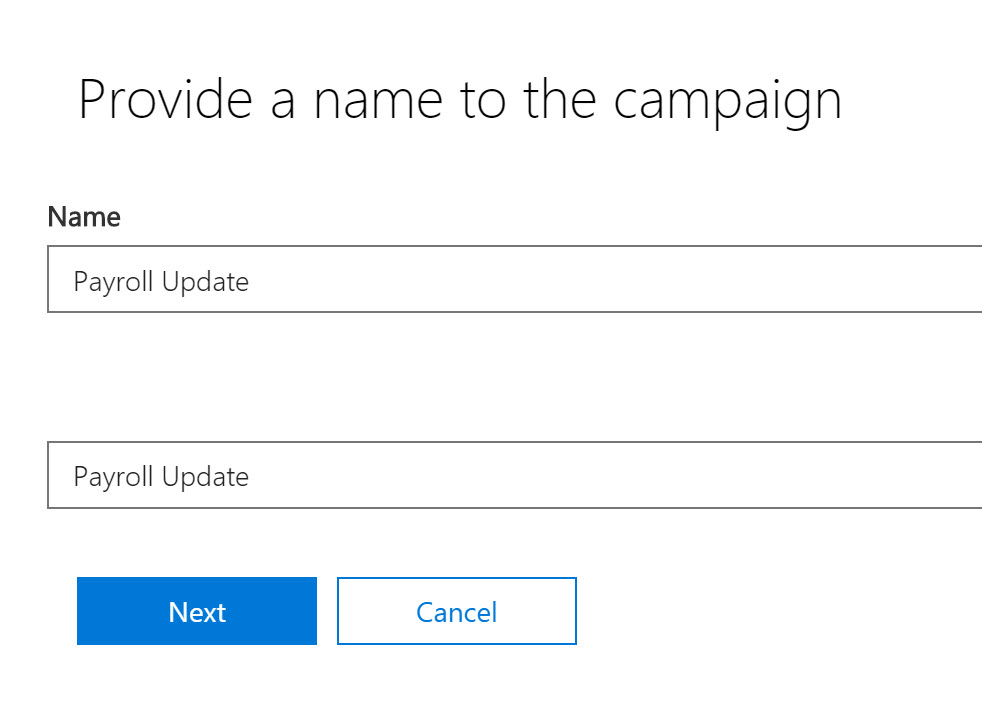
At the Provide a name to the campaign page, choose your own name, or click on “Use template”. If you click on “Use template” you will see two template options to choose from. I’ve chosen “Prize Giveaway” below:
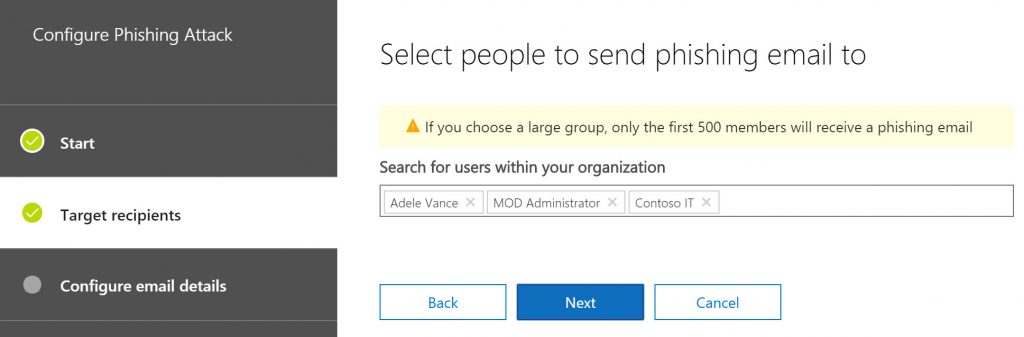
Next, select the users you want to “phish”. You can select individual users or groups.
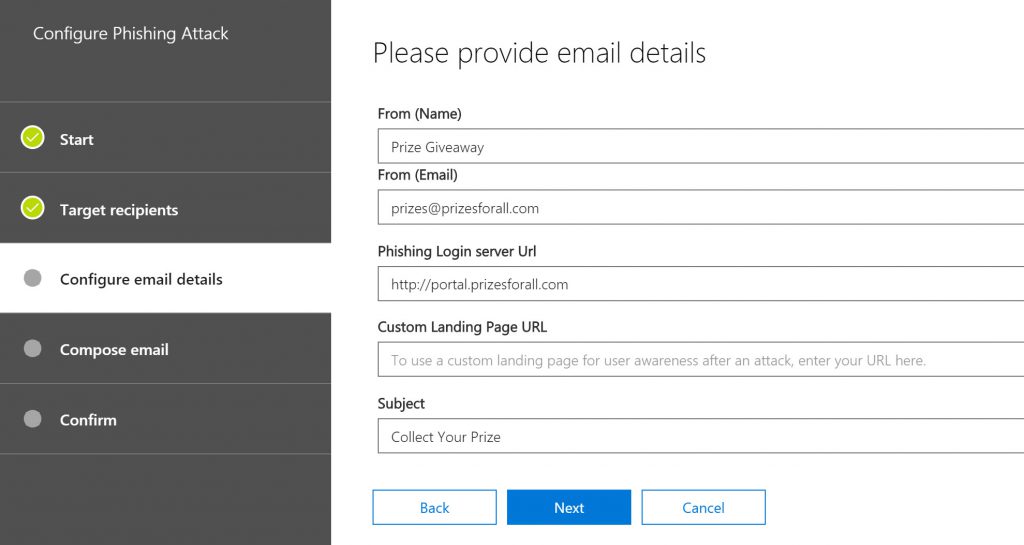
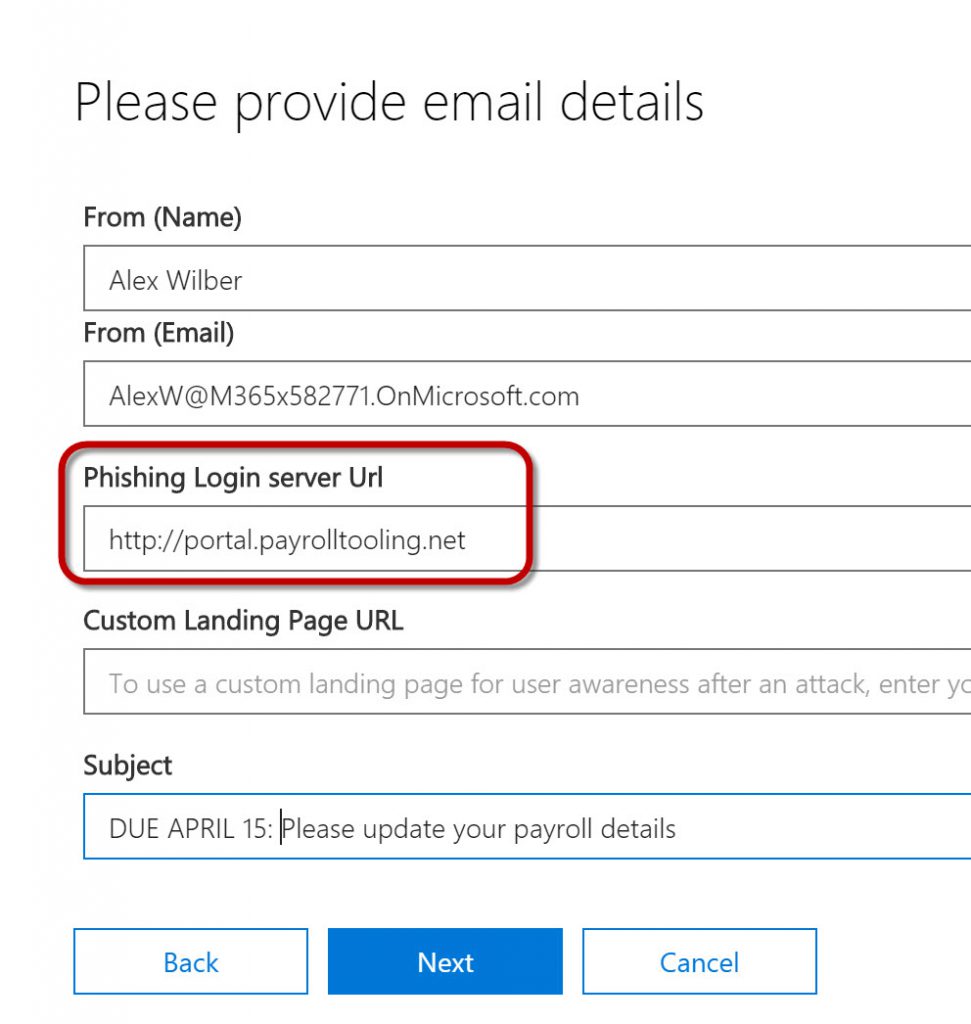
On the next page, if you’ve selected a template, all the details will be filled in for you. One important value to note here is the Phishing Login server URL. Select one of the phishing login servers from the drop down. This is the way the attack simulator is able to track who has clicked on the URL in the email and provides reporting.
Note that the URL's for the phishing login servers are NOT actually bad sites. They are sites set up specifically for the purposes of this tool's functioning.
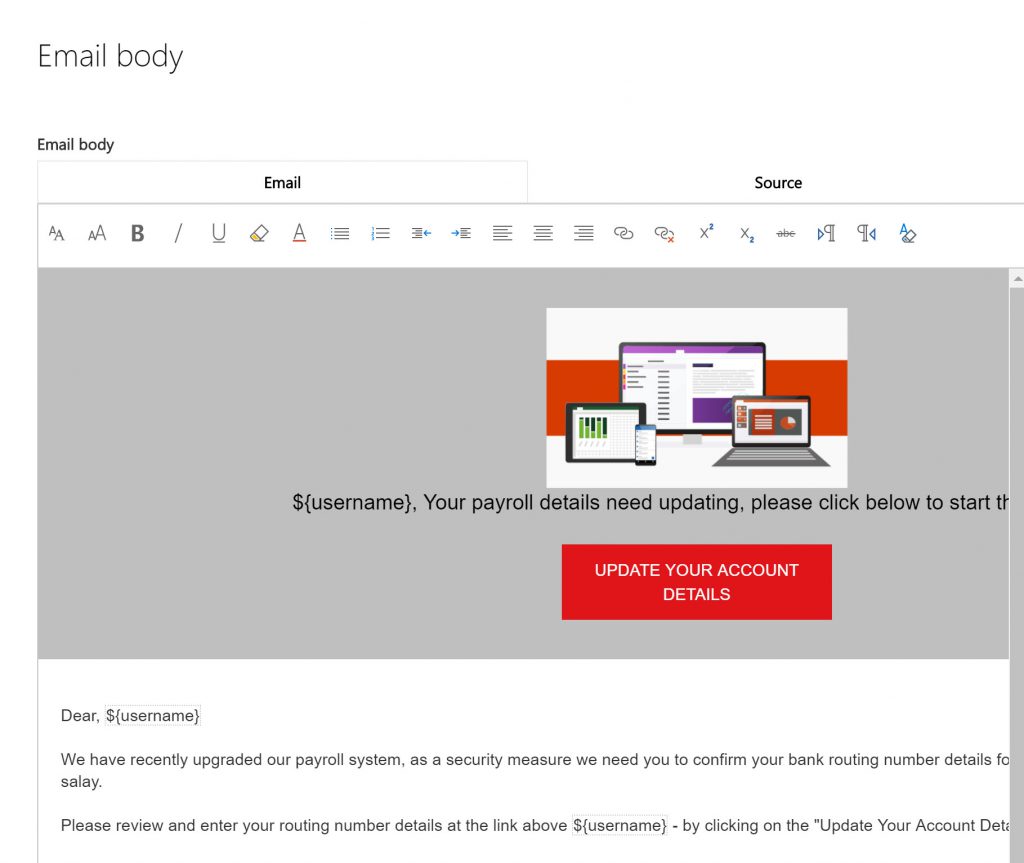
In the Email body form, you can customize the default email. Make sure that you have a variable ${username} so that the email looks like it was sent directly to the end user.
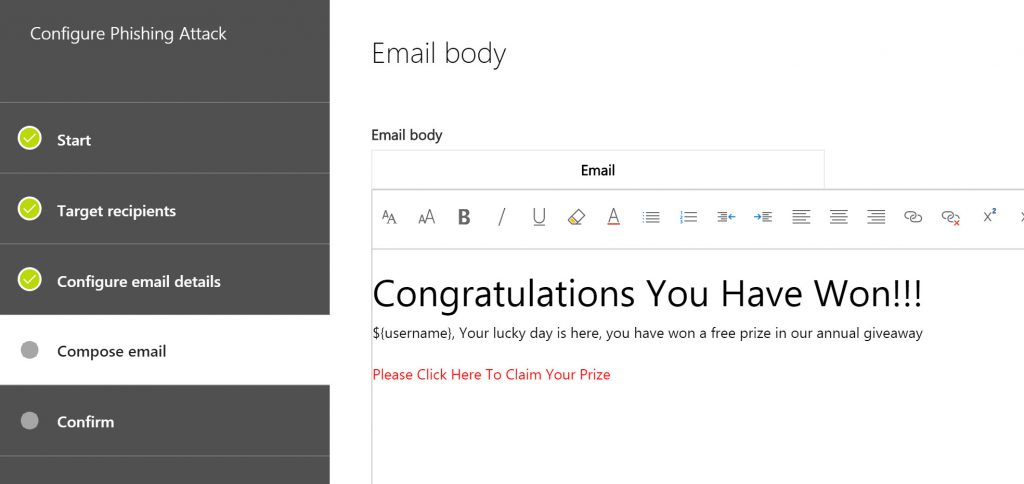
Click Confirm, and the Attack Simulator will send the email out to the end users you specified.
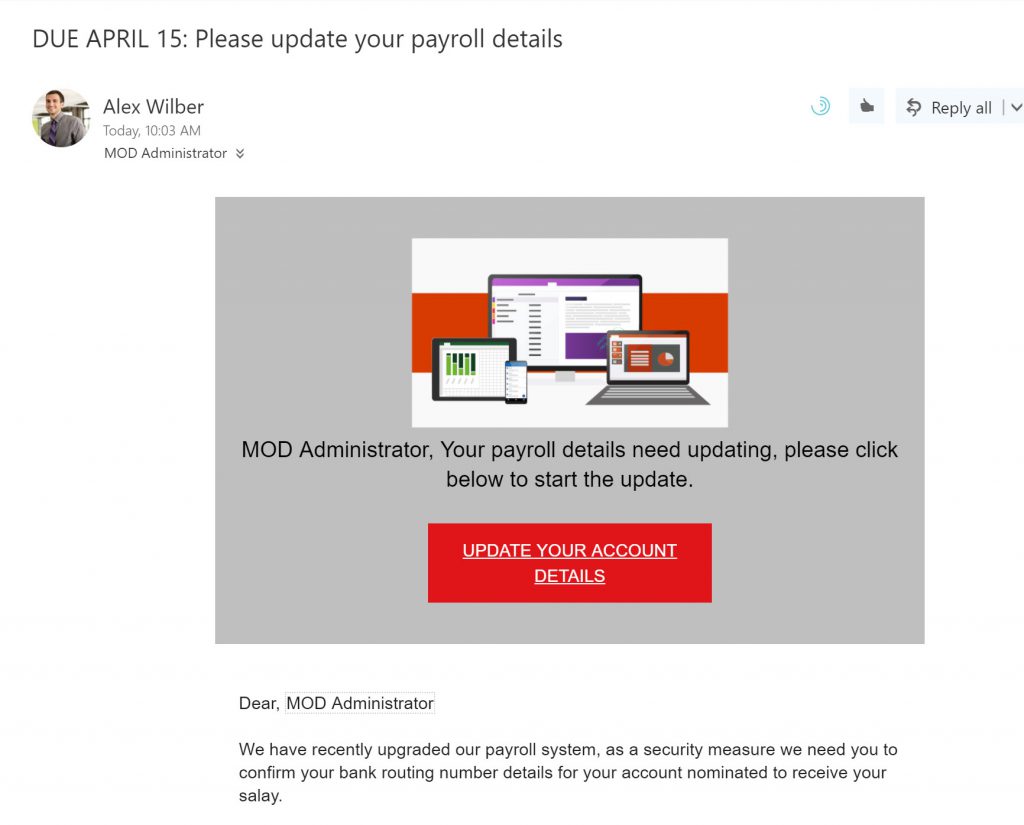
Next, I opened the Administrator email account that I targeted and saw this:
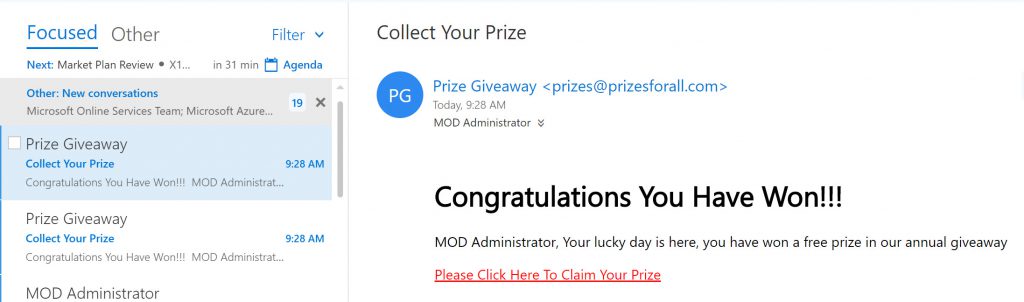
Notice that it customized the email to the MOD Administrator account in the body of the email.
If I click on the URL (which points to the https://portal.prizesforall.com URL we highlighted earlier) I get sent to a website that looks like this. 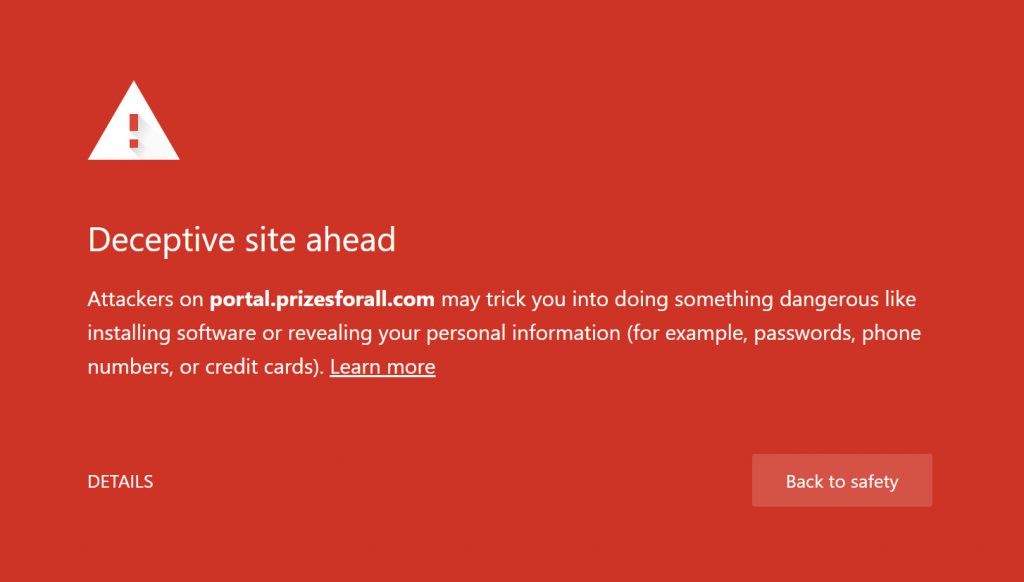
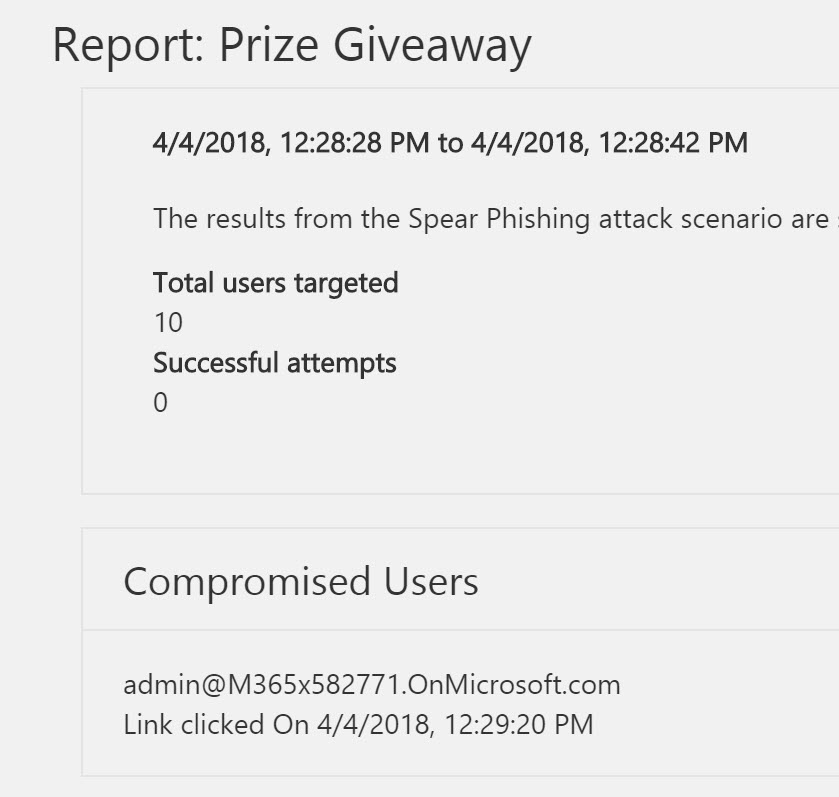
Finally, if I click on the reporting area of the Attack Simulator, I can see who has clicked on the link and when.
Okay. But seriously…would you really have clicked on that URL?
Probably not.
So how do you make it a little more sophisticated?
Let’s create a more realistic attack.
In this attack we will use the Payroll Update template, which is very similar to what you might actually see in many corporate environments. You can also create your own HTML email using your organization’s branding and formatting.
I’ll again target the MOD Administrator because he seems like a good target, since he’s the O365 global admin (and seems to be somewhat gullible).
In this situation though, instead of sending from what appears to be an external email address (prizes@prizesforall.com, used in the previous attack) I’m going to pose as someone the user might actually know. It could be the head of HR or Finance or the CEO. I’ll use the actual email address of that person so that it resolves correctly.
Notice that this templates uses a different phishing login server URL from the drop down. You’ll see why in a second.
In the Email body page, we’ve got a much more realistic looking email.
It should be noted, though, that if you make the email look ABSOLUTELY PERFECT and people click on the URL, what have they learned? It’s best to provide a clue in the email that a careful user would notice and recognize as a problem. Maybe send the official HR email from someone who isn’t actually in HR, or leave off a footer in the email that identifies it as an official HR email. Whatever it is, there should be something that you can use to train users to look out for.
So if you read the email template below carefully, you'll see some grammatical errors and misspellings that should be a "red flag" to a careful user.
Again, you Confirm the settings for the attack and the attack launches.
Going to the MOD Administrator’s mailbox….that’s much more realistic, wouldn’t you say?
When I click on the “Update Your Account Details” link, I get sent to this page, where I’m asked to provide a username and password, which of course, I dutifully provide:
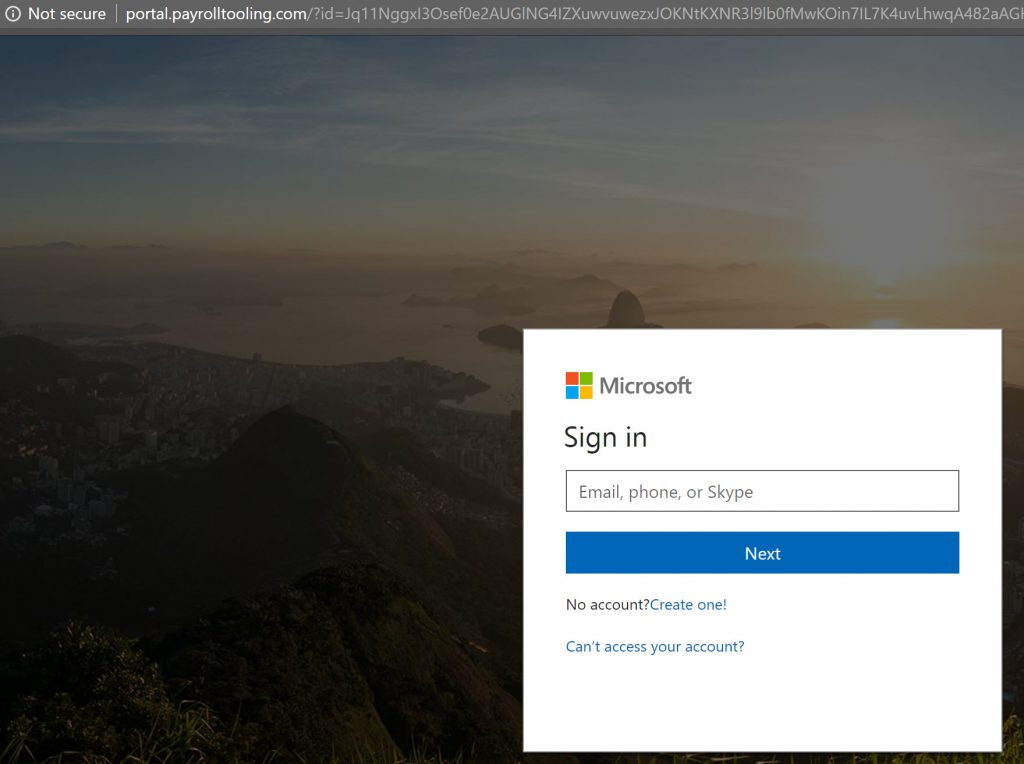
Notice, however, that the URL at the top of the page is the portal.payrolltooling.com website - even thought the page itself looks like a Microsoft login page. Many attacks will mimic a "trusted site" to harvest credentials in this manner. When you're testing you can use any email address (legitimate or not) and any password for testing - it isn't actually authenticating anything.
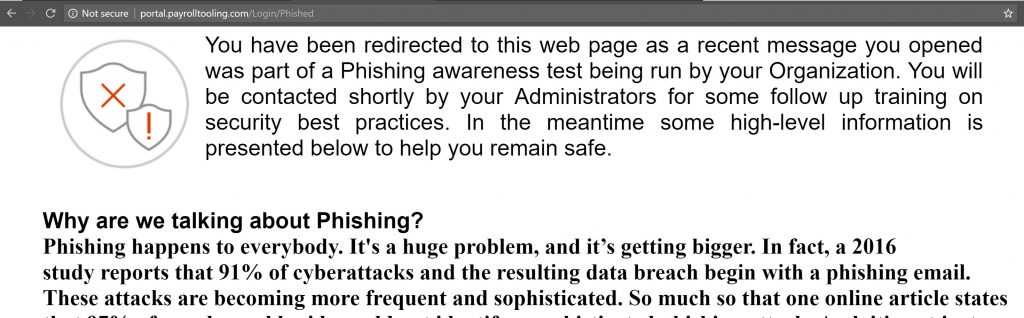
Once I enter some credentials, I am directed to the page below, which lets me know I’ve been “spear phished” and provides some hints about identifying these kind of attacks in the future:
And finally, in the reporting, I see that my administrator was successfully spear phished. 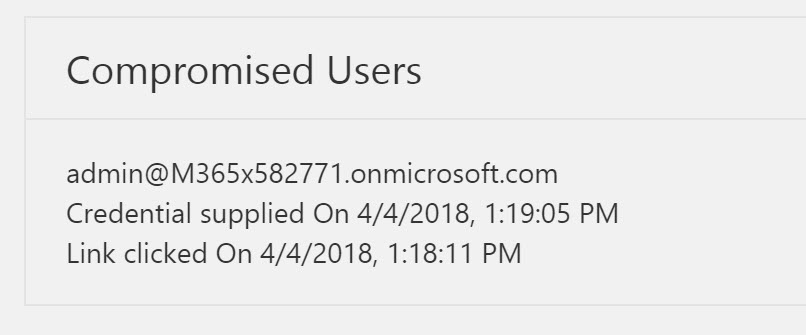
The Value of Attack Simulations
This is all interesting (and a little bit fun) but what does it really teach us? The objective is that once we know what sort of attacks our users are vulnerable to (password or phishing are the two highlighted by this tool), then we can provide training to help enhance our security posture. Many of the ransomware attacks that are blanketing the news lately started as phishing campaigns.
If we can take steps to ensure that our users are better equipped to identify suspicious email, and help them select passwords that aren't easily compromised, we help improve the organization's security posture.