Step-By-Step: Managing Your Nano Servers
Hello folks,
On November 19th 2015 we released the latest technical previews of Windows Server 2016 . I’m actually looking forward to wipe my lab clean and start again with TP4.
Technical Preview 4 includes significant enhancements, many of which reflect customer feedback on the previews released earlier this year.
- Application platform features, including new capabilities for
- Nano Server
- Windows Server Containers updates
- And – new in this release – Hyper-V Containers
- Software-defined datacenter capabilities, across storage, networking, and compute, let you reduce cost and increase agility.
- New security features to help address evolving threats and new threat vectors.
Until now, Nano Server only supported specific roles.
- Hyper-V
- Scale-Out File Server (SOFS)
The Technical Preview 4 now adds support for:
- DNS Server
- IIS server
- as well as MPIO, VMM, SCOM, DSC push mode, DCB, Windows Server Installer, and the WMI provider for Windows Update.
- Its Recovery Console supports editing and repairing the network configuration.
- A Windows PowerShell module is now available to simplify building Nano Server images.
If you have not heard of Nano server, please watch the following 14 minute video where Jeffrey Snover walks you through it.
For today. let’s look at how we manage Nano servers in our lab environment. We already discussed the installation of Nano server in an earlier post Step-By-Step: Installing a Nano server in my test domain. So this is where we will pick things up.
Manage Nano Server
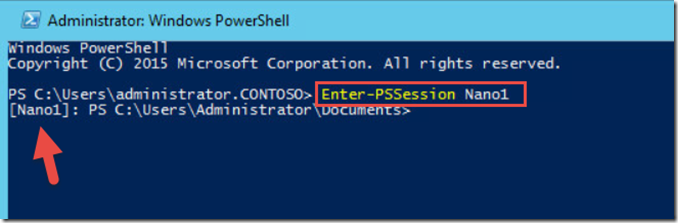
1- Open PowerShell on your existing Windows Server 2016. (our lab environment is still using TP3 the rebuild is scheduled for next week) and type Enter-PSSession Nano1 and Enter. You will notice that the prompt changes to indicate that we are now connected to the Nano1 server.
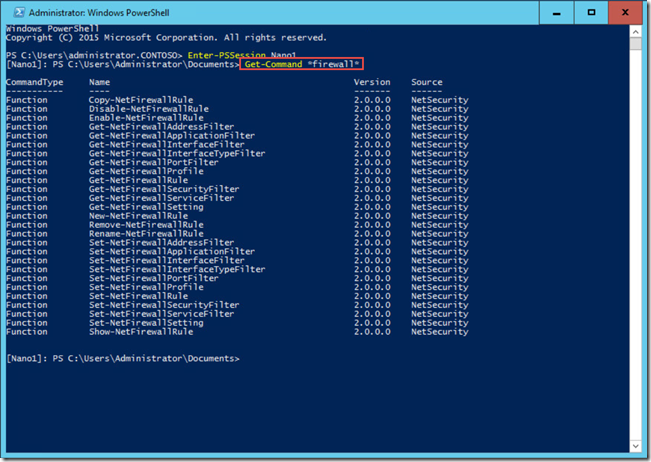
2- The first thing we want to do is open the proper ports in the firewall in order to be able to connect to it and manage the server. Let’s look at the firewall cmdlets by typing Get-Command *firewall* and enter
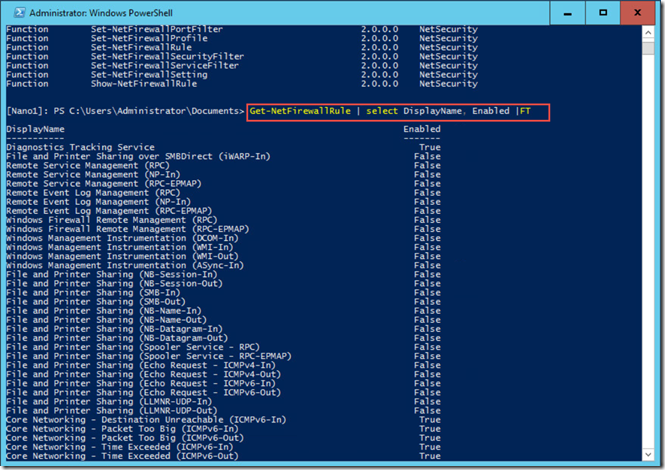
3- To list the current firewall rules we will use the following command
Get-NetFirewallRule | Select DisplayName, Enabled | FT
The list of current firewall Rules is pretty long. take a minute to check it out.
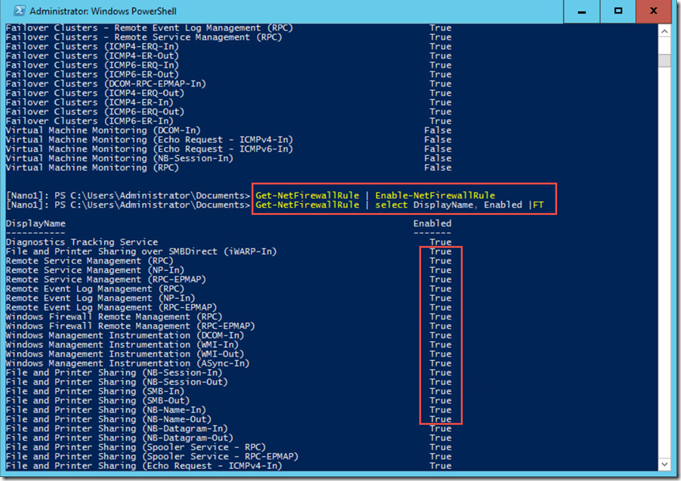
4- In the Powershell command windows, Type Get-NetFirewallRule | Enable-NetFirewallRule. This will enable any rules that were not enabled in the listing above.
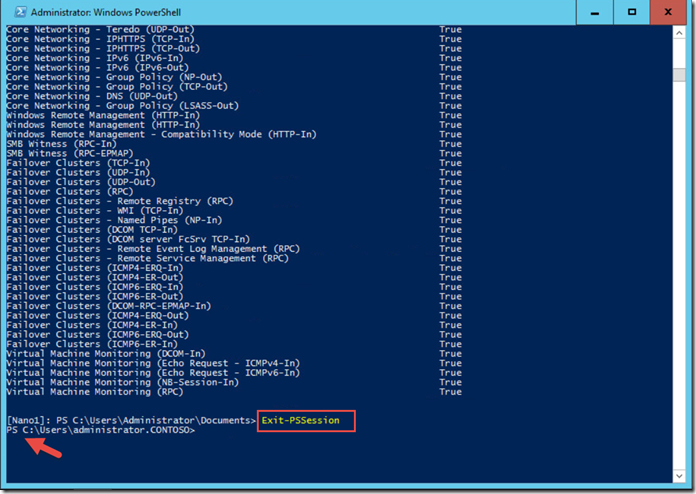
5- We are now done in PowerShell so we can close the remote PowerShell session by typing Exit-PSSession, and then press ENTER
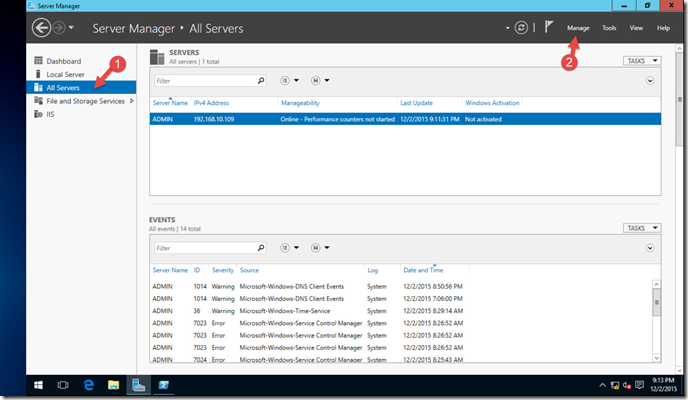
6- We can now open Server Manager on our Windows Server 2016 box, and then in Server Manager, click All Servers, Click Manage,
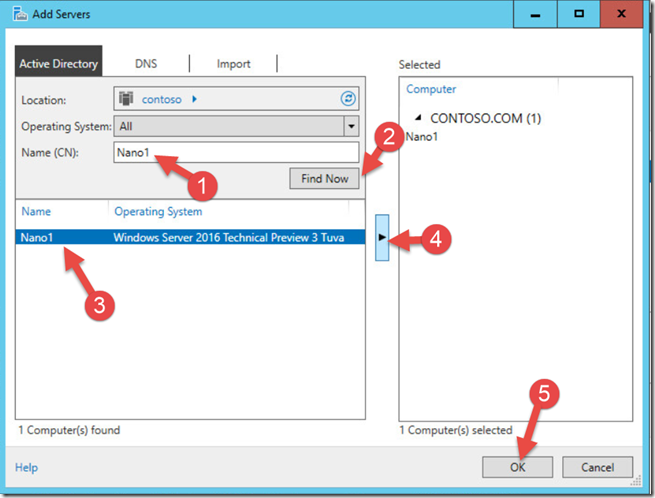
7- In the Manage menu, click Add Servers, type Nano1 in the Name (CN) field, click Find Now, click Nano1, click the Add button, and then click OK
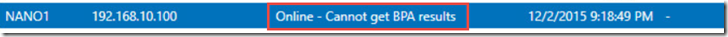
Note that the error regarding not being able to get the BPA results is expected.
8- from now on you can manage the server through this interface like you would do any other.
For example: I navigated in the left navigation pane to File and Storage Services. Reviewed the drive configuration and In the left navigation, clicked Volumes. Under Nano1 (1) and selected C:
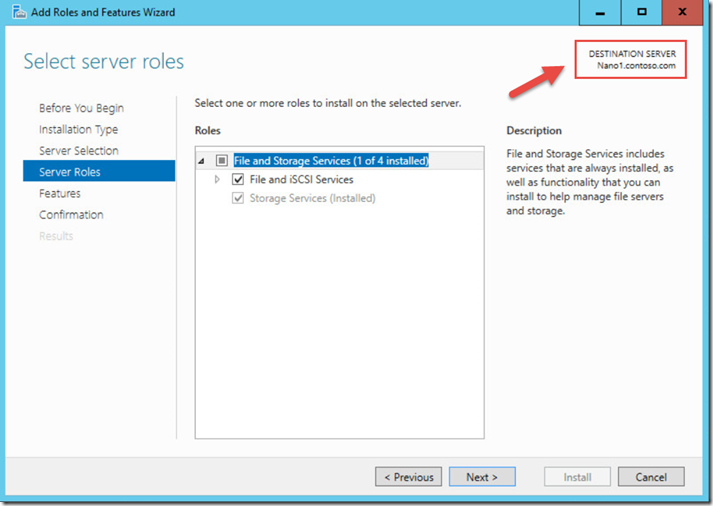
To create a share on that disk, in the Shares tile, I clicked Start the Add Roles and Features Wizard. Clicked Next twice, accepting the defaults, and then clicked Install. When the wizard completed I closed it.
As you can see, Nano servers for the roles that it support provides you with a more secure, lighter, and robust platform to build your services on. Whether you use PowerShell or MMC consoles to manage them is completely up to you.
Hope this helps!
Cheers!
Pierre Roman
@pierreroman