Step-By-Step: Setup and Enablement of Office 365 Message Encryption
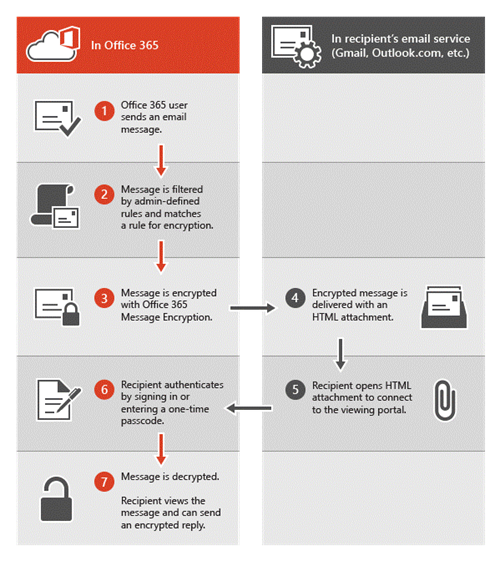
Office 365 Message Encryption is an online service which is built on Microsoft Azure Rights Management (Azure RMS) offering. With Azure RMS set up for an organization, administrators can enable message encryption by defining transport rules that determine the conditions for encryption. A rule can require the encryption of all messages addressed to a specific recipient, for example.
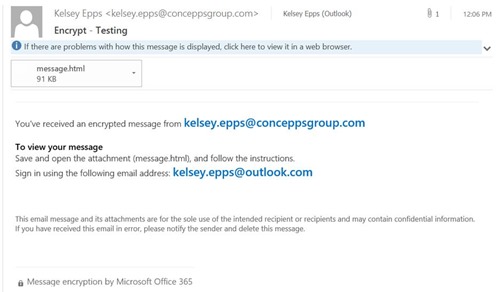
When a user sends an email message in Exchange Online that matches an encryption rule, the message is sent out with an HTML attachment. The recipient opens the HTML attachment in the email message, recognizes a familiar brand if that’s present, and follows the embedded instructions to view the encrypted message on the Office 365 Message Encryption portal. The recipient can choose to view the message by signing in with a Microsoft account or a work account associated with Office 365, or by using a one-time passcode. Both options help ensure that only the intended recipient can view the encrypted message.
The following diagram summarizes the passage of an email message through the encryption and decryption process.
Diagram showing the path of an encrypted email
The process to setup and enable Office 365 Message Encryption is really easy. There are three main steps that need to be followed
- Activate Azure Rights Management
- Setup Azure Rights Management for Exchange Online
- Setup transport rules to enforce message encryption in Exchange Online
The steps to enable this are as follows:
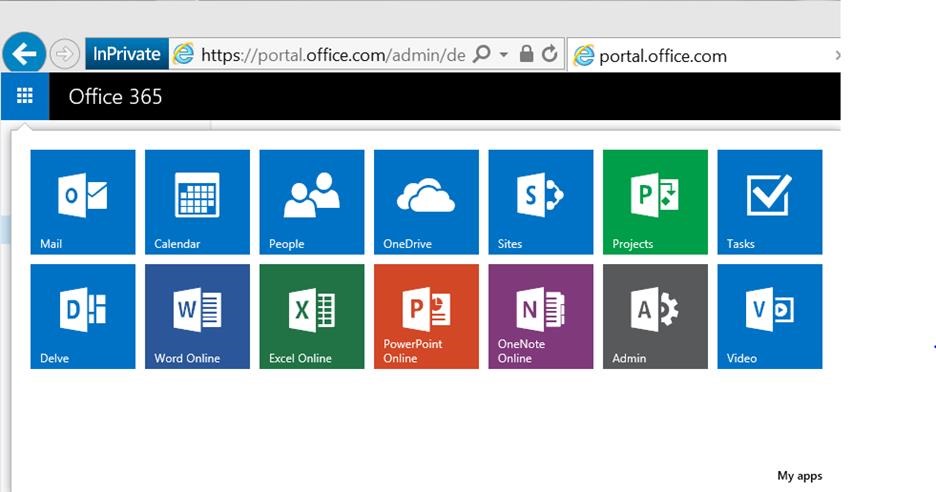
Step 1: Activate Azure Rights Management for Office 365 Message Encryption
- Login to Microsoft Online Portal with a Global Admin Account
- Open the App Launcher (waffle)
- Select Admin
- Select SERVICE SETTINGS from the left pane
- Click Rights Management
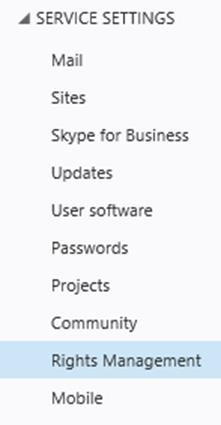
- From within RIGHTS MANAGEMENT click Manage
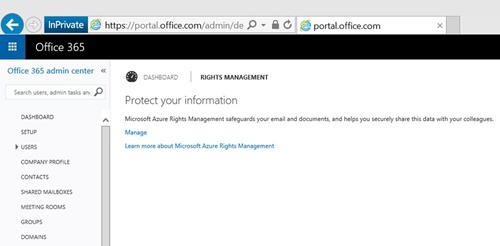
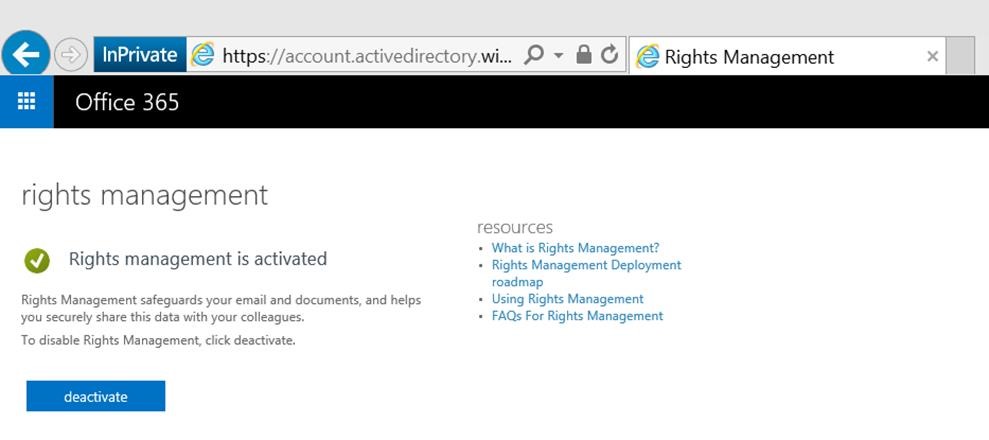
- On the management page, click Activate
- Click Activate again on the popup asking if you are sure you want to activate Rights Management
Step 2: Set up Azure Rights Management for Office 365 Message Encryption
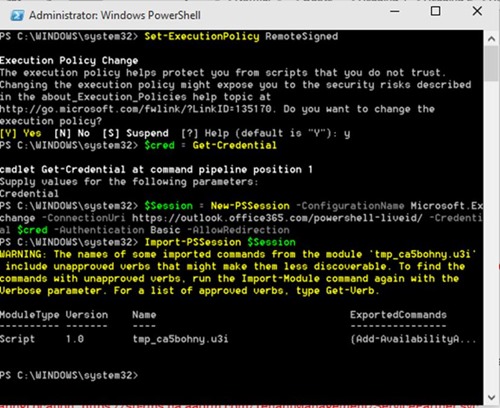
The next steps are completed via connecting to Exchange Online with PowerShell
Open PowerShell as Administrator
Enter the following commands to connect and import the session
Set-ExecutionPolicy RemoteSigned
$cred = Get-Credential
$Session = New-PSSession -ConfigurationName Microsoft.Exchange -ConnectionUri https://outlook.office365.com/powershell-liveid/ -Credential $cred -Authentication Basic –AllowRedirection
Import-PSSession $Session
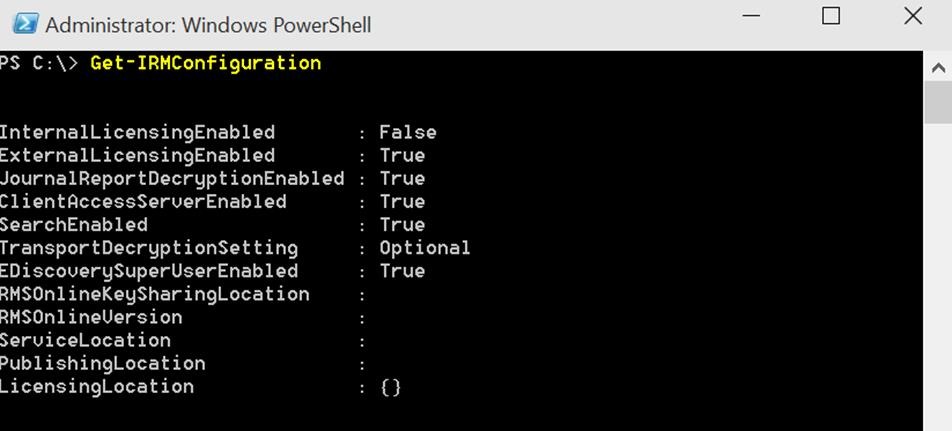
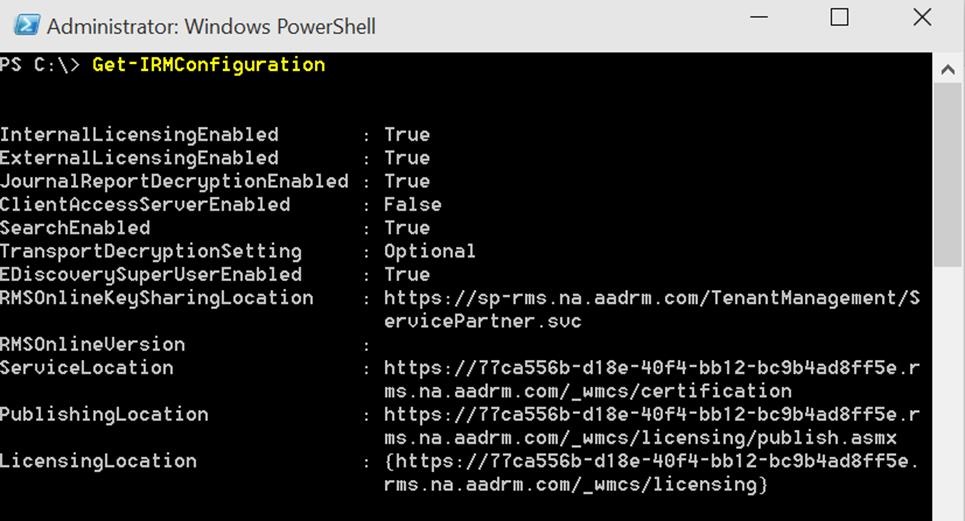
Verify your IRM isn’t configured already
Get-IRMConfiguration
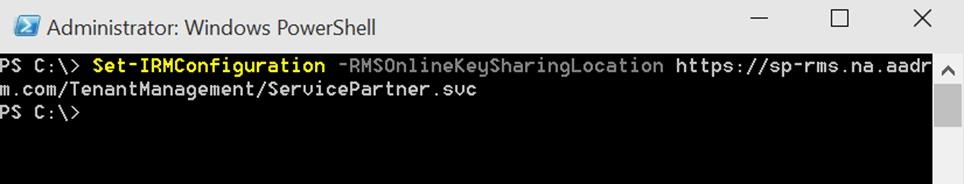
Configure RMS with the online key-sharing location for Exchange Online with PowerShell (locations below). For my example I am using North America, but the table below shows all the locations
Set-IRMConfiguration -RMSOnlineKeySharingLocationhttps://sp-rms.na.aadrm.com/TenantManagement/ServicePartner.svc
Location
RMS key sharing location
North America
https://sp-rms.na.aadrm.com/TenantManagement/ServicePartner.svc
European Union
https://sp-rms.eu.aadrm.com/TenantManagement/ServicePartner.svc
Asia
https://sp-rms.ap.aadrm.com/TenantManagement/ServicePartner.svc
South America
https://sp-rms.sa.aadrm.com/TenantManagement/ServicePartner.svc
Office 365 for Government
https://sp-rms.govus.aadrm.com/TenantManagement/ServicePartner.svc1
Import the Trusted Publishing Domain (TPD) from RMS Online
Import-RMSTrustedPublishingDomain -RMSOnline -name "RMS Online"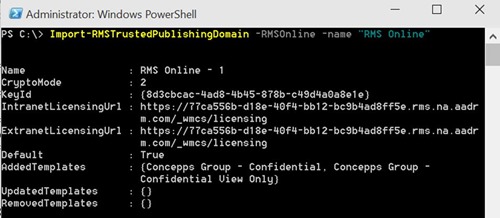
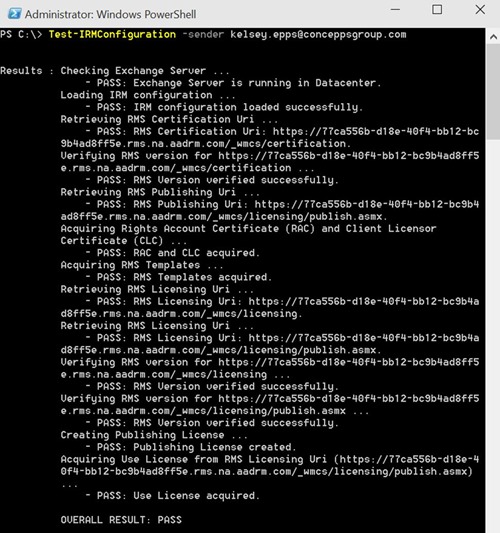
Verify successful setup of IRM in Exchange Online
Test-IRMConfiguration –sender admin@domain.com
Disable IRM templates in OWA and Outlook
Set-IRMConfiguration -ClientAccessServerEnabled $false

Enable IRM for Office 365 Message Encryption
Set-IRMConfiguration -InternalLicensingEnabled $true
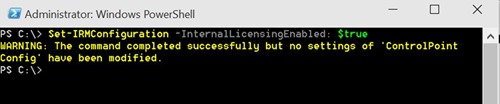
NOTE: You shouldn’t see that warning, but if you do it’s safe to ignore. I got it because I ran the command and forgot to grab the screen shot before clearing the screen, thus I had to run the command again.
View the IRM Configuration
Get-IRMConfiguration
Step 3: Create Transport Rules to Encrypt Messages
- Open the Office 365 Admin Portal (https://portal.microsoftonline.com)
- Open Exchange Admin Center
- Click Mail Flow
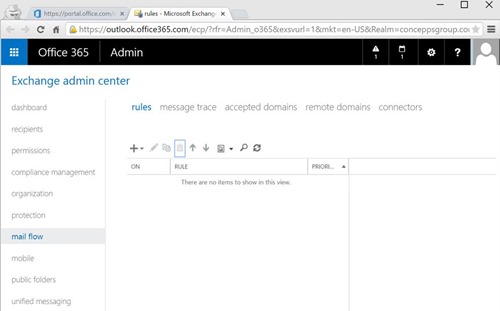
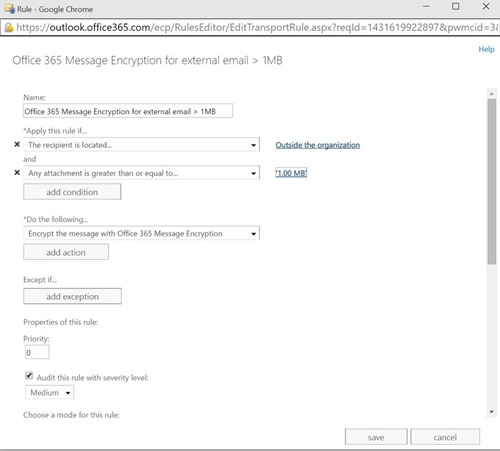
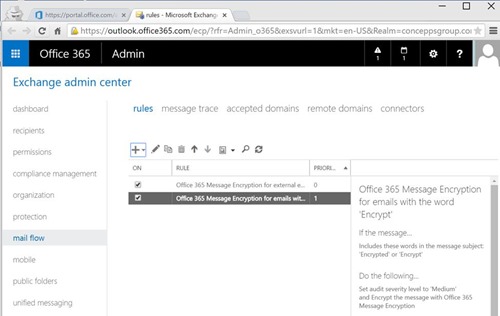
- Click the + and create your transport rule. I have created two simple rules.
- This rule will encrypt anything that is sent external with an attachment larger than 1MB
NOTE: This rule will encrypt the email if the word ‘Encrypt’ is in the subject line of the email. This will give the users (once trained) the flexibility to encrypt emails they deem sensitive.
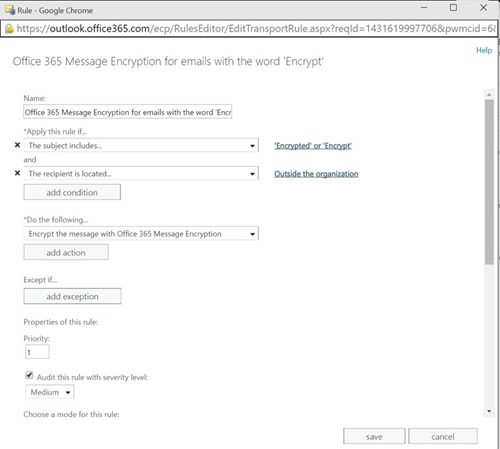
- Make sure the rules are active and test
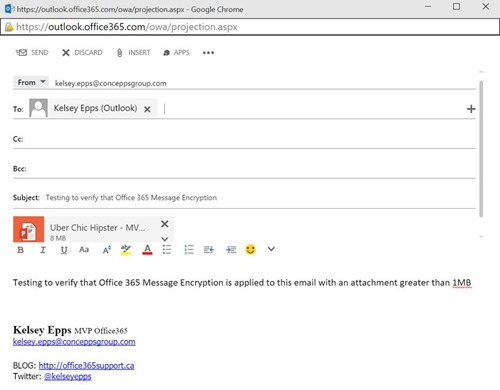
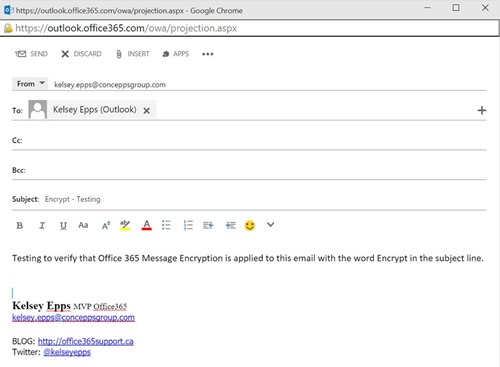
- Testing that the transport rule apply Office 365 Message Encryption
Testing Transport Rule 1
Testing Transport Rule 2
When the user gets the email, this is how its presented to them