Addressing Shadow IT Via Enabling Azure Active Directory Services
The age of Shadow IT was introduced not so long ago via the plethora of devices (smartphones / tablets / notebooks) brought by employees into their respected organizations. With employee hopes of being able to use said device to address both work and personal needs all but dashed by IT’s possible lack of knowledge or then inability to secure said device, some end users took it upon themselves to find a way to enable that device and circumvent IT all together. The dangers of this meant no one in the organization other than the employee was aware of the data being consumed on the unauthorized device. Should that device become lost or stolen, there would be no means for IT to lock that device.
In this new cloud era, Shadow IT no longer maliciously enables just hardware, but unauthorized SaaS applications as well. In a report recently published by Gigaom entitled Shadow IT: data protection and cloud security, it is estimated that 70 percent of unauthorized data access is committed by an organization’s own employees. Like the introduction of unauthorized devices, SaaS applications are being introduced into organizations at a staggering rate. IT professionals tasked with testing and possibly approving use of said SaaS apps cannot keep up with the demand and so employees install and use these apps without the telling the rest of the organization.
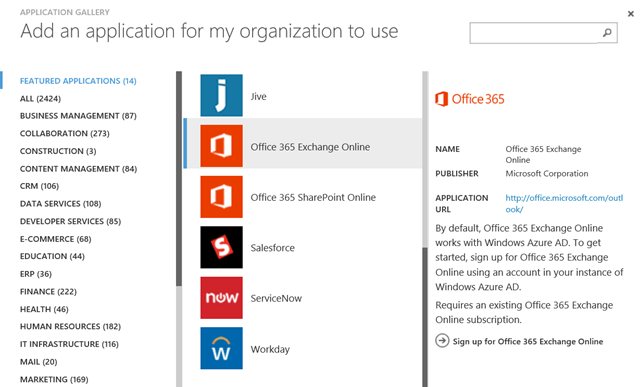
Microsoft, through Azure Services, has introduced solutions to better support IT professionals in their quest to enable fellow employees use desired SaaS applications. Azure Active Directory provides the means to enable Single Sign-On (SSO) service to 2400+ SaaS applications ranging from storage apps to social apps to even education, health and of course productivity apps through pre-integrated templates. Integration of Azure Active Directory SSO consists of four parts:
- Users are enabled to access SaaS applications via their organizational account in Azure AD
- User provisioning and deprovisioning into target SaaS applications is based on changes made either Azure Active Directory, Windows Server Active Directory or both
- Azure Management Portal enables single point of SaaS application management and access
- Unified monitoring and reporting of malicious user activity
Once steps have been followed to enable Azure Active Directory Authentication, all that is required is for the IT professional is to select from the 2400+ template made available to allow for SSO enablement.
To reach this point, one must:
- Sign into their Azure Management Portal
- Select Active Directory
- Select the active directory instance they wish to add SSO to
- Select Add an application found under the Explore section
Be sure to complete the Microsoft Virtual Academy jumpstart entitled, Azure IaaS for IT Pros, to further extend knowledge around Azure Active Directory Services.