Security: Hype vs. Reality
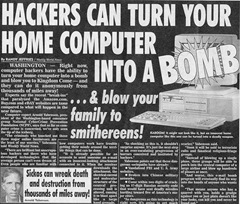 Over the past few weeks I’ve been reading a few stories on vulnerabilities found in various operating systems. You might have seen the headlines like Attack Sneaks Rootkits Into Linux Kernel or Security Team Shows Unfixable Windows 7 Hack or First Mac OS X Botnet Activated and while all are valid (both as exploits and as ultra scary headlines) they are so easily mitigated that I have to call them out.
Over the past few weeks I’ve been reading a few stories on vulnerabilities found in various operating systems. You might have seen the headlines like Attack Sneaks Rootkits Into Linux Kernel or Security Team Shows Unfixable Windows 7 Hack or First Mac OS X Botnet Activated and while all are valid (both as exploits and as ultra scary headlines) they are so easily mitigated that I have to call them out.
Lets look at the first one on the Linux rootkit. There is a feature in the Linux kernel 2.4 and up that is used by developers to perform kernel debugging. This feature allows someone to mount memory as /dev/mem and read and write directly to the memory. Great feature for kernel debugging but someone could exploit this and mount memory, write to memory and insert malicious code. So what is the catch, you need to have root access. Mitigation? Let’s look a the first two rules of computer security…
Law #1: If a bad guy can persuade you to run his program on your computer, it's not your computer anymore
Law #2: If a bad guy can alter the operating system on your computer, it's not your computer anymore
I especially like the “new” and “unfixable” flaw in Windows 7. This is the same exploit, by the same researchers, demoed on Windows Vista two years ago, updated to work on Windows 7 so not really new and the unfixable part? VBootkit is a piece of code that is loaded into memory on boot and allows an attacker to take control of the machine, log keystrokes, change passwords and more. The catch? The attacker needs to have PHYSICAL access to the machine when it boots to inject the code into memory. In fact they need to have physical access each and every time the machine boots as the code is memory resident and does not survive a reboot and it cannot be done remotely. It can be mitigated with BitLocker configured in TPM mode (does that count as a fix?). Simple physical security practices also mitigate this risk reminding me of computer security rule #3…
The last one makes me laugh and actually reminds me of a few sayings; “buyer beware” and “you get what you pay for”. The OSX botnet has been made possible by injecting malicious code into downloadable copies of pirated versions of iWork ‘09 and Photoshop CS4 for OSX. A user simply has to download and install this software from a P2P site for the machine to join the botnet. While pirated software is tempting to a lot of people it reminds me of the 6th rule of computer security…
Law #6: A computer is only as secure as the administrator is trustworthy
If you are installing software from untrustworthy sources there is no way you can be sure your PC is secure anymore. I met a few people on the Energize IT tour with newer builds of the Windows 7 beta that they downloaded from P2P networks and it is shocking to see. Not only are they admitting to a Microsoft employee that they downloaded and installed pirated Microsoft software (can you say DUH!), they are also oblivious to the fact that a WIM image can be mounted, edited (to lets say run a custom key logger) and then repacked into an installable format. I know someone who had their identity stolen using a pirated version of Windows Vista in which the attacker placed a small custom application that recorded all saved passwords and login information and uploaded it to an FTP site.
Security is something that will always be a concern and will always make headlines. Just remember headlines are meant to generate traffic and think about the 10 Immutable Laws of Security while reading.
