Conficker… Threat? Or April’s fool?
Regardless… Like Murphy said… “He who laughs last probably made a back-up”. In this case “He who laughs last probably applied MS08-067 to all his systems”.
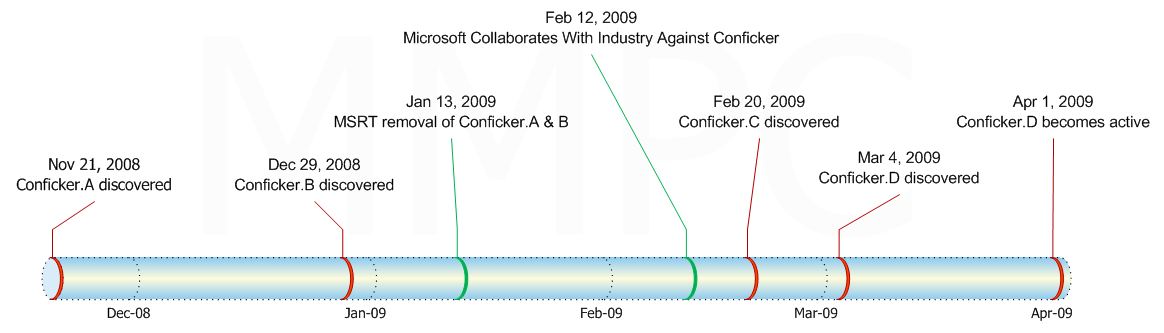
I’ve received a lot of questions from enthusiasts & customers about the latest version of Conficker discovered earlier this month, Worm:Win32/Conficker.D. Well, like it has been the case since the first discovery of Conficker, (see timeline below), Microsoft is making huge efforts to resolve this. Including offering a $250,000 reward, for information leading to the arrest and conviction of those responsible for Conficker.
So what is this about? Any computer infected with Conficker will presumably start trying to contact domains on the Internet, presumably for a new set of instructions. Tomorrow, it may begin using a new algorithm to determine what domains to contact. However Microsoft has not identified any other actions scheduled to take place on April 1, 2009.
There are 2 resources from Microsoft for the best practices to protect yourself from Conficker:
- For consumer go to “Protect yourself from the Conficker computer worm”
- for IT Pros you want to read “Protect Windows from Conficker”
Following the guidelines that Microsoft has always promoted should find this event manageable. These guidelines are in this case:
- Apply security updates
- Update security software signatures ( That means keep your anti-virus and anti-spyware up to date.)
- Clean infected systems
More that the vulnerability identified in Microsoft Security Update MS08-067 Conficker exploits weak passwords and auto-run features to spread itself. IT Pros that manage Active Directories should ensure that passwords are managed using the Group Policy Object. (AD DS Fine-Grained Password and Account Lockout Policy Step-by-Step Guide)
As for the auto-run, it’s pretty easy to spot as long as you know what you’re looking for. In the screenshot below the option Open folder to view files — Publisher not specified is not the standard Open folder to view files — using Windows Explorer that you would normally see. If you select the first option, the worm executes and can begin to spread itself to other computers.
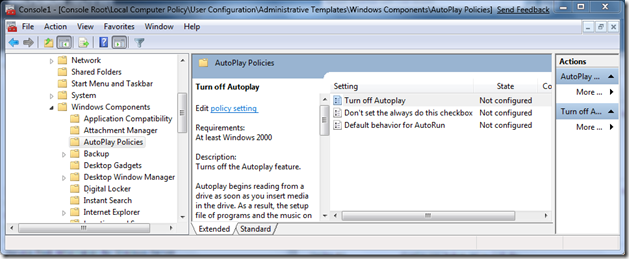
If you wish you can manage the AutoPlay behaviour through the Group Policy as well.
If you think your computer is infected, you may be unable to download certain security products, such as the Microsoft Malicious Software Removal Tool or access some sites like our own Microsoft Update. If you can't access them, try using the Windows Live OneCare Safety Scanner or there is always help from your preferred anti-malware vendors.
It’s very Important that everyone ensures that Microsoft Security Update MS08-067 has being applied to all the systems in your environment.
See also this post on the Microsoft Malware Protection Center: Information about Worm:Win32/Conficker.D.
And of course, if you’re still concerned about Conficker, you can get more information and free support by going to https://microsoft.com/protect or customers in the US and Canada can call the PC Safety hotline at 1-866-PCSAFETY
I hope this helps.
Cheers!
Pierre Roman, MCSE, ITIL| Microsoft Canada Co. | IT Pro Advisor | pierre.roman@microsoft.comphone: 613-212-2370 | mobile: 613-715-2311
IT Pro blog | Twitter | Facebook | LinkedIn