Introducing Lingering Object Liquidator v2
Greetings again AskDS!
Ryan Ries here. Got something exciting to talk about.
You might be familiar with the original Lingering Object Liquidator tool that was released a few years ago.
Today, we're proud to announce version 2 of Lingering Object Liquidator!
Because Justin's blog post from 2014 covers the fundamentals of what lingering objects are so well, I don't think I need to go over it again here. If you need to know what lingering objects in Active Directory are, and why you want to get rid of them, then please go read that post first.
The new version of the Lingering Object Liquidator tool began its life as an attempt to address some of the long-standing limitations of the old version. For example, the old version would just stop the entire scan when it encountered a single domain controller that was unreachable. The new version will just skip the unreachable DC and continue scanning the other DCs that are reachable. There are multiple other improvements in the tool as well, such as multithreading and more exhaustive logging.
Before we take a look at the new tool, there are some things you should know:
1) Lingering Object Liquidator - neither the old version nor the new version - are covered by CSS Support Engineers. A small group of us (including yours truly) have provided this tool as a convenience to you, but it comes with no guarantees. If you find a problem with the tool, or have a feature request, drop a line to the public AskDS public email address, or submit feedback to the Windows Server UserVoice forum, but please don't bother Support Engineers with it on a support case.
2) Don't immediately go into your production Active Directory forest and start wildly deleting things just because they show up as lingering objects in the tool. Please carefully review and consider any AD objects that are reported to be lingering objects before deleting.
3) The tool may report some false positives for deleted objects that are very close to the garbage collection age. To mitigate this issue, you can manually initiate garbage collection on your domain controllers before using this tool. (We may add this so the tool does it automatically in the future.)
4) The tool will continue to evolve and improve based on your feedback! Contact the AskDS alias or the Uservoice forum linked to in #1 above with any questions, concerns, bug reports or feature requests.
Graphical User Interface Elements
Let's begin by looking at the graphical user interface. Below is a legend that explains each UI element:
[caption id="attachment_16956" align="alignnone" width="1044"]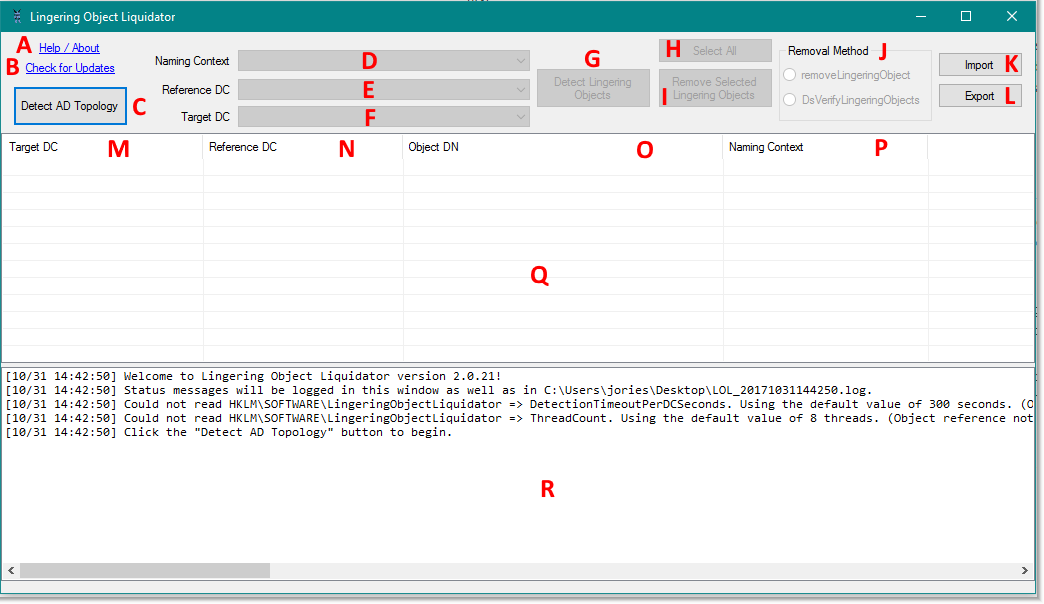 Lingering Object Liquidator v2[/caption]
Lingering Object Liquidator v2[/caption]
A) "Help/About" label. Click this and a page should open up in your default web browser with extra information and detail regarding Lingering Object Liquidator.
B) "Check for Updates" label. Click this and the tool will check for a newer version than the one you're currently running.
C) "Detect AD Topology" button. This is the first button that should be clicked in most scenarios. The AD Topology must be generated first, before proceeding on to the later phases of lingering object detection and removal.
D) "Naming Context" drop-down menu. (Naming Contexts are sometimes referred to as partitions.) Note that this drop-down menu is only available after AD Topology has been successfully discovered. It contains each Active Directory naming context in the forest. If you know precisely which Active Directory Naming context that you want to scan for lingering objects, you can select it from this menu. (Note: The Schema partition is omitted because it does not support deletion, so in theory it cannot contain lingering objects.) If you do not know which naming contexts may contain lingering objects, you can select the "[Scan All NCs]" option and the tool will scan each Naming Context that it was able to discover during the AD Topology phase.
E) "Reference DC" drop-down menu. Note that this drop-down menu is only available after AD Topology has been successfully discovered. The reference DC is the "known-good" DC against which you will compare other domain controllers for lingering objects. If a domain controller contains AD objects that do not exist on the Reference DC, they will be considered lingering objects. If you select the "[Scan Entire Forest]" option, then the tool will (arbitrarily) select one global catalog from each domain in the forest that is known to be reachable. It is recommended that you wisely choose a known-good DC yourself, because the tool doesn't necessarily know "the best" reference DC to pick. It will pick one at random.
F) "Target DC" drop-down menu. Note that this drop-down menu is only available after AD Topology has been successfully discovered. The Target DC is the domain controller that is suspected of containing lingering objects. The Target DC will be compared against the Reference DC, and each object that exists on the Target DC but not on the Reference DC is considered a lingering object. If you aren’t sure which DC(s) contain lingering objects, or just want to scan all domain controllers, select the "[Target All DCs]" option from the drop-down menu.
G) "Detect Lingering Objects" button. Note that this button is only available after AD Topology has been successfully discovered. After you have made the appropriate selections in the three aforementioned drop-down menus, click the Detect Lingering Objects button to run the scan. Clicking this button only runs a scan; it does not delete anything. The tool will automatically detect and avoid certain nonsensical situations, such as the user specifying the same Reference and Target DCs, or selecting a Read-Only Domain Controller (RODC) as a Reference DC.
H) "Select All" button. Note that this button does not become available until after lingering objects have been detected. Clicking it merely selects all rows from the table below.
I) "Remove Selected Lingering Objects" button. This button will attempt to delete all lingering objects that have been detected by the detection process. You can select a range of items from the list using the shift key and the arrow keys. You can select and unselect specific items by holding down the control key and clicking on them. If you want to just select all items, click the "Select All" button.
J) "Removal Method" radio buttons. These are mutually exclusive. You can choose which of the two supported methods you want to use to remove the lingering objects that have been detected. The "removeLingeringObject" method refers to the rootDSE modify operation, which can be used to "spot-remove" individual lingering objects. In contrast, the DsReplicaVerifyObjects method will remove all lingering objects all at once. This intention is reflected in the GUI by all lingering objects automatically being selected when the DsReplicaVerifyObjects method is chosen.
K) "Import" button. This imports a previously-exported list of lingering objects.
L) "Export" button. This exports the selected lingering objects to a file.
M) The "Target DC Column." This column tells you which Target DC was seen to have contained the lingering object.
N) The "Reference DC Column." This column tells you which Reference DC was used to determine that the object in question was lingering.
O) The "Object DN Column." This column contains the distinguished name of the lingering object.
P) The "Naming Context Column." This column contains the Naming Context that the lingering object resides in.
Q) The "Lingering Object ListView". This "ListView" works similarly to a spreadsheet. It will display all lingering objects that were detected. You can think of each row as a lingering object. You can click on the column headers to sort the rows in ascending or descending order, and you can resize the columns to fit your needs. NOTE: If you right-click on the lingering object listview, the selected lingering objects (if any) will be copied to your clipboard.
R) The "Status" box. The status box contains diagnostics and operational messages from the Lingering Object Liquidator tool. Everything that is logged to the status box in the GUI is also mirrored to a text log file.
User-configurable Settings
The user-configurable settings in Lingering Object Liquidator are alluded to in the Status box when the application first starts.
Key: HKLM\SOFTWARE\LingeringObjectLiquidator
Value: DetectionTimeoutPerDCSeconds
Type: DWORD
Default: 300 seconds
This setting affects the “Detect Lingering Objects” scan. Lingering Object Liquidator establishes event log “subscriptions” to each Target DC that it needs to scan. The tool then waits for the DC to log an event (Event ID 1942 in the Directory Service event log) signaling that lingering object detection has completed for a specific naming context. Only once a certain number of those events (depending on your choices in the “Naming Contexts” drop-down menu,) have been received from the remote domain controller, does the tool know that particular domain controller has been fully scanned. However, there is an overall timeout, and if the tool does not receive the requisite number of Event ID 1942s in the allotted time, the tool “gives up” and proceeds to the next domain controller.
Key: HKLM\SOFTWARE\LingeringObjectLiquidator
Value: ThreadCount
Type: DWORD
Default: 8 threads
This setting sets the maximum number of threads to use during the “Detect Lingering Objects” scan. Using more threads may decrease the overall time it takes to complete a scan, especially in very large environments.
Tips
The domain controllers must allow the network connectivity required for remote event log management for Lingering Object Liquidator to work. You can enable the required Windows Firewall rules using the following line of PowerShell:
Get-NetFirewallRule -DisplayName "Remote Event Log*" | Enable-NetFirewallRule
Check the download site often for new versions! (There's also a handy "check for updates" option in the tool.)
Final Words
We provide this tool because we at AskDS want your Active Directory lingering object removal experience to go as smoothly as possible. If you find any bugs or have any feature requests, please drop a note to our public contact alias.
Download: https://aka.ms/msftlol
Release Notes
v2.0.19:
- Initial release to the public.
v2.0.21:
- Added new radio buttons that allow the user more control over which lingering object removal method they want to use - the DsReplicaVerifyObjects method or removeLingeringObject method.
- Fixed issue with Export button not displaying the full path of the export file.
- Fixed crash when unexpected or corrupted data is returned from event log subscription.