AD LDS Schema Files Demystified
Hi, Russell here. When installing Active Directory Lightweight Domain Services (AD LDS) instances, it is quite possible to paint oneself into a corner rather quickly. That’s because LDS comes with minimal schema definitions. To truly make LDS useful to your applications, one must have an understanding of how best to take advantage of the included schema definition files.
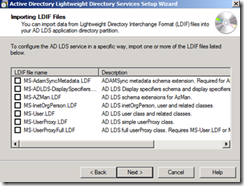
When performing an LDS installation using the AD LDS Setup Wizard, you are offered several schema options:
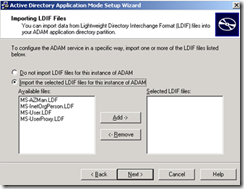
When performing an installation using ADAM SP1, the following schema options are presented:
So how do you know which LDF files to select? Well seriously, it all depends upon your intentions, and I’m not talking about whether or not you want to ask our resident Elf out on a date.
Ideally, Schema definition requirements should be defined by your Application Developers. But as an AD or Server Administrator it will greatly benefit you to assist in the decision making process as the choices made during install are permanent. So what to pick?
Let’s start with definitions of the basic LDF files included in ADAM SP1:
- MS-InetOrgPerson – Is a Microsoft implementation of the RFC 2798 LDAP Object Class. The InetOrgPerson object is used in many non-Microsoft X.500 and LDAP Directory Services to represent people within the enterprise.
- MS-User.ldf - Is a Microsoft implementation of the X.500 User Class defined in RFC 1274. The User object class is the traditional representation for people within Microsoft’s Active Directory. Import of this LDF will provide AD LDS with a base user class, which can be used to define local users
- MS-AZMan.ldf – Classes and attributes required to use ADAM/LDS as an authorization store for Windows Authorization Manager, AKA AZMan. Import of this LDF provides the base functionality to use AZMan .NET class libraries to leverage AD LDS as a role-based authentication store
- MS-UserProxy.ldf – One of two LDF files required to use ADAM/LDS Bind Redirection Features. This ldf file extends default (no ldf imports) schema to allow user synchronization with Active Directory. Useful when you want to allow your internal forest(s) users extranet access to AD LDS hosted applications
I leaned on the word “implementation” in a couple of those definitions. That’s because whenever we discuss Internet RFCs, there is much that’s open to interpretation due to the use of the words “should,” “may,” “shall,” etc. as defined in Key words for use in RFCs to Indicate Requirement Levels. I also pointed out that UserProxy.ldf is one of two ldf files required to use ADAM/LDS for Bind Redirection to Active Directory. That’s because MS-ADAMSyncMetadata.ldf is missing from the ADAM SP1 Setup Wizard. (So is UserProxyFull). Windows Server 2008 and Windows Server 2008 R2 include these additional schema definitions as part of the Setup Wizard:
- MS-ADAMSyncMetadata – Creates the ADAMSync engine classes and attributes necessary to synchronize Active Directory with ADAM/LDS. Adamsync.exe uses these classes and attributes to translate AD Users into ADAM/LDS users. This gives you the design flexibility of allowing domain users coming in via the internet, to logon to LDS & be authenticated via proxy to the domain.
- MS-ADLDS-DisplaySpecifiers – New for Windows Server 2008 (It is 2010 after all). Provides the capability to manage ADAM/LDS replication configuration with AD Sites and Services
- MS-UserProxyFull – Allows full user or inetorgperson attribute definition for synchronized Active Directory users. Originating in ADAM SP1 but hidden from the installation wizard, it is now available as an option to MS-UserProxy.ldf
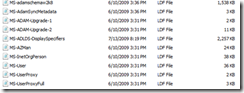
What? Hidden from the installation wizard you say? How can that be? Easy, there are actually several, optional schema mods contained within the Windows\ADAM installation directory. The LDF Files are coded with “@@UI-Description: @@excludeFromList” to keep them out of the Setup Wizard GUI. In Windows Server 2008 R2, there are four other LDF files hidden from view:
These are actually some of the best files available. It is a shame they are hidden from view:
- MS-adamschemaw2k3.ldf – This is a representation of Active Directory’s schema for Windows Server 2003 R2
- MS-adamschemaw2k8.ldf – Like its little brother (no, not Scooter) this is a representation of Windows Server 2008 Schema
- MS-ADAM-Upgrade-1 – Provides ADAM 1.0 and ADAM SP1 instances the ability to reload SSL certificates and makes the UnexpirePassword controlAccessRight to the schema.
- MS-ADAM-Upgrade-2 – Introduces Windows Server 2008 R2 Recycle Bin Features into LDS
Now why would you need this enticing new feature in 2008 R2, such as the Recycle Bin? Uh, I don’t know, perhaps you like to see your users disappear with no way to recover? (No system state backup, no recycle bin to catch mistakes.) I work nights; I see many disaster recoveries, not just for AD LDS, but for AD too. This nifty feature can save you time and money – and most importantly – your job. Until next time.
-Russell “Rusty aka R2 aka Spaniard” Despain