AzMan MMC with a sample application
Hey everyone, Mark from Directory Services again. Just the other day I ran across something that may be useful to the public. Here in Directory Services we support the Authorization Manager snap-in, aka AzMan.msc. This tool can configure role-based access control on applications using an AzMan store. The Azman store can be in an XML file, Active Directory, ADAM/AD LDS or in SQL. In this article we will focus on using XML for a store. Unless you have an application that can use the AzMan store it is hard to really know how this works. Well you are now in luck!
Before we go any further I want to make sure everyone understands that this article is not how to write an application to use the AzMan store. This article will not involve any coding at all, script writing, etc. Please note that all the sample applications provided are just that, samples, and are not supported by Microsoft.
Setting up a sample AzMan Store and Application
Ok, with that being said lets learn a little about Azman.
1) First thing we need is a Windows Server 2008 member server, an Active Directory domain and a client machine. I will be using a Windows Server 2003 domain where the member server is running Windows 2008 and the client is running Windows XP SP3. Both of these computers are joined to the domain.
2) Download the Windows 2008 SDK from here. It does not matter which server we download it to and install on. By default it will install to the Program Files directory so open windows explorer and drill down to:
Microsoft SDK\Windows\v6.1\Samples\Security\Authorization\AzMan
Inside this folder you will see a folder called WebExpense. Copy this entire folder to your Windows 2008 member server so that the folder resides underneath the inetpub\wwwroot directory. This sample application will only work on Windows 2008 using the steps described below.
3) Next run the Server Manager snap-in on the 2008 server and install the Web Server (IIS) role. During the installation of the role when you get to the Select Role Services page, select the ASP.Net under Application Development. This will cause a window to popup stating it needs to install some other services. Go ahead and select the Add Required Role Services. Before clicking on Next, make sure you check the box under Security for Windows Authentication. Now click Next, confirm your selections and then click on Install. Once the install is done, go ahead and close the installation page.
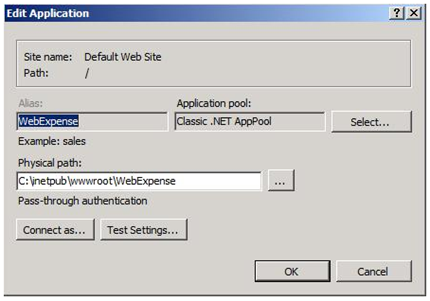
4) Now go to the Administrative Tools and open the Internet Information Services (IIS) Manger. In the left hand pane expand the connections and drill down so that you see the WebExpense folder underneath the Default Web Site. Right click the WebExpense folder then select Convert to Application. In the Add Application popup window for the Application Pool click on the Select button, then in the drop down box select Classic .Net AppPool then Ok twice.
5) With the WebExpense highlighted in the center pane (/WebExpense Home) find the Authentication icon and double click on it. Verify that Anonymous Authentication is Disabled and Windows Authentication is Enabled.
6) Now we are moving right along, go to Start – Run – azman.msc – Ok on the 2008 server. Right click in the left hand pane on Authorization Manger then Open Authorization Store. Verify we have XML file selected and then click on Browse. Browse to the folder:
inetpub\wwwroot\WebExpense folder
Select the AzStore XML file. Let’s leave this for now and come back to it shortly.
7) Go to your XP client and open IE then go to the 2008 server’s URL as:
https://<2008servername>/webexpense/index.asp
The page should open as Trey Research and WebExpense – online expense reporting and auditing. Then you should see Welcome <username>: Sorry <username> you do not have permission to use this application. Please contact your manager. This is telling us that we do not have the proper permissions to run the web application.
Using the Sample Application
Before starting to learn how to use the MMC let’s learn a little bit about Groups, Tasks and Operations:
Groups: We can create different type of groups. We can create a Basic Application Group which is much like a local group. We can add users/groups from Active Directory or another group from Authorization Manager. We can even exclude users/group as well. Say you have a group of 200 users in AD where you want to add all the users but one user. We could add the group then go in and exclude the one user.
An LDAP Query Application Group could be created that determine who is a member by running a LDAP query. If the user matches the query then the user is deemed to be a member of the group. You could use a simple LDAP query or you could make it more complex to fit your needs.
Business Rule Application Group is the third type of group that can be created. In this type of group you will need to have a script that defines the members of this type of group. The script will need to be constructed either in VB or Java.
Role Definitions: A role definition is defined as a set of permissions that a user must have to perform a job or task. A role can have lower level tasks, roles and operations associated with it.
Task Definitions: A task definition is smaller than a role definition and can be use to define other roles and tasks.
Operation Definitions: This can only be seen in Developer mode. Operation definitions are small computer level actions that are used to define tasks and usually are not relevant to an administrator.
1) Now let’s go back to the 2008 server and the Authorization Manger MMC. In the MMC in the left hand pane under the AzStore.xml go to Groups. This is where you can create groups for different uses in AzMan. The default ones here should be Managers and Admins. Let’s experiment here a little and right click Groups and select New Application Group. Call the new group Submitters, in the Group Type select LDAP Query Application Group then ok.
2) Now right click the new group you created and select Properties and go to the Query tab. Click inside the box and type in: (objectSid=*) then Ok.
3) Now expand Expense Web in the left hand pane, expand Role Assignments then go to Submitter. Right click Submitter and select Assign Users and Groups – From Authorization Manager. Place a check mark in the box next to the group we just created then Ok.
4) Now let’s test this from the XP client. If the IE window is still open close it. Open IE again and go to the WebExpense URL like we did before. You should see the icon and Submit an Expense. Now you have permissions to submit an expense!
Note: The reason you can see this now is that we authenticate to the web site via integrated authentication meaning we are using our logged on credentials at the XP client to authenticate with to the application. We gave the Submitters group we created the permission on the Submitter Role. When we created the Submitters group we went back into the properties of the group to the query tab. There we defined the query to Active Directory (AD) as objectSid=*. This is basically saying if the user has an objectSid in AD then they meet the requirement of being a member of this group. By setting it up this way we are basically saying everyone has the permission to submit an expense. You can get more granular if you want by changing the query for the Submitters group.
5) Now let’s try something a little different. Under your Role Assignments – Submitter, right click the group we added and delete it. Go to one of your domain controller and open Active Directory Users and Computers. Create a new Global Group, I called mine AzManSubmitters. Add a user to the group, I added the account I was logged onto the XP client with named Mark.
6) Now add this new group to the Submitter role in AzMan. Go to the XP client and log off then back on. We need to do this to update our security group membership as we just added ourselves to a group.
7) Now go back to the URL for the WebExpense application. You should still see the Submit an Expense. The reason why we can still see it is due to we are a member of the AzManSubmitters group and we had added that group to the Submitters role.
8) Let’s explore even more now. In Azman MMC, under the Expense Web expand Definitions and go to the Role Definition. Here you see several roles. Take the Submitter for an example. Go to the properties of Submitter then to the Definition tab. Here you can see what Tasks the Submitter role can perform. In this case the Submitters can Submit Expense.
9) Now go to the Task Definitions folder under Definitions. Go to the properties of Submit Expense and its Definition tab. Here you can see that within the Submit Expense task it breaks it down further to Read Expense and Submit operations. All this defines what the particular Role can perform within the application.
10) Take a look on the Definitions\Task Definitions\Definition Tab\Submit\Authorization Rule. Here you can define some script code and tweak the rule to fit your business needs. In this example you cannot submit an expense if the amount is 500 or greater. You can try this by connecting to the application and if you have the Submit permission click on the link then fill in all the boxes. Enter an amount that is greater than 500 then click on the Submit button. This should return a runtime error due to the application is configured to use a backend SQL server to store the data and we do not have one configured. Again, we are not concerned with that in this article.
AzMan can be run in one of the following two modes, Developer or Administrator. To select or find out which you are running right click Authorization Manager in the left hand pane and select Options. The default mode is Administrator. When in Developer mode you can create, deploy and maintain applications. You also have unrestricted access to all of AzMan features. When in Administrator mode you can maintain and deploy applications. You still have access to all AzMan features except you cannot create new applications or define operations.
Summary and Notes
Let’s recap some of the information and make a few notes.
Now that we know a little bit about the type of groups that can be used, here is a little bit of low level troubleshooting information. When using an LDAP Query Application Group the web server will need to make an LDAP call to a DC (or ADAM as the case may be) to verify that you meet the requirements set in the LDAP query for the group. If you take a network trace of the user connecting to the web application from the web server then you will see the LDAP traffic. You will not be able to see the exact LDAP query being made in the network trace as the information will be encrypted. Other than that you should authenticate using Kerberos when using either Basic Application Groups or if you use Active Directory groups directly on the Role. Another piece of advice is to pay attention to the Role Definitions and Role Assignments. Let’s say you have a user that needs to approve expenses and you add the user one way or another to the Approver role. They connect to the web application and they state that they cannot see the Approve Expenses icon. Look at the Role Definitions. You will find that the Approver role only has the Approve Expense task. You will need to add the user to the Expense Manager role as well as they have View Pending Expenses. You need to be able to view the pending expenses in order to be able to approve them.
To dig in and learn more about AzMan see the help file that is associated with the MMC. We have come a long ways with the help files over the years and they can be a good resource for you. Here are some other good references:
Role-Based Access Control for Multi-tier Applications Using Authorization Manager
Windows Platform Software Development Kit (SDK): Authorization Manager Model
Role-Based Access Control Using Windows Server 2003 Authorization Manager
Using Dynamic Business Rules in Windows Server 2003 Authorization Manager
Dynamic Groups in Windows Server 2003 Authorization Manager
Use Role-Based Security in Your Middle Tier .NET Apps with Authorization Manager
Mark ‘Ned can’t think of a funny nickname for me’ Ramey