How to use Bitlocker Data Recovery Agent to unlock Bitlocker Protected Drives
Hello, my name is Manoj Sehgal. I am a Senior Support Escalation Engineer in the Windows group and today’s blog will cover “How to use Bitlocker Data Recovery Agent (DRA) to unlock Bitlocker Protected Drives
In Windows 7, we have option to unlock devices using Bitlocker DRA if you have a PKI Infrastructure in place.
What is a Data Recovery Agent?
Data recovery agents are individuals whose public key infrastructure (PKI) certificates have been used to create a BitLocker key protector, so those individuals can use their credentials to unlock BitLocker-protected drives. Data recovery agents can be used to recover BitLocker-protected operating system drives, fixed data drives, and removable data drives. However, when used to recover operating system drives, the operating system drive must be mounted on another computer as a data drive for the data recovery agent to be able to unlock the drive. Data recovery agents are added to the drive when it is encrypted and can be updated after encryption occurs.
Pre-requisites:
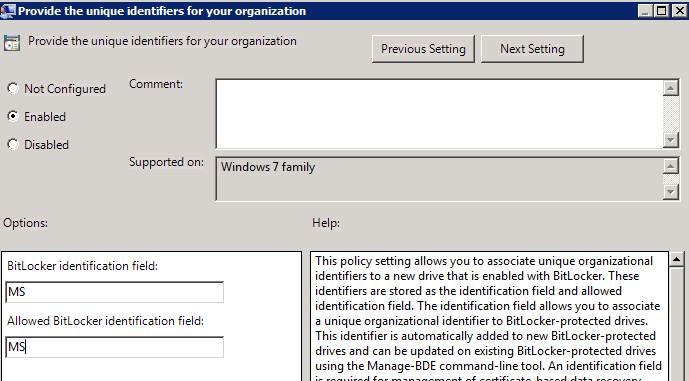
To use DRA for BitLocker, make sure the GPO for Unique ID is enabled.
To Configure the GPO,
1. Expand Computer Configuration, Administrative Templates, Windows Components, BitLocker Drive Encryption.
“Provide Unique Identifiers for your organization”
Enable this Policy (see screenshot below).
For BitLocker Identification Field you can give your company name or any name.
Make sure BitLocker Identification Field and Allowed BitLocker Identification field are the same.
When do we use Bitlocker DRA?
In Windows 7, we introduced feature of Bitlocker DRA which can be used to unlock fixed data drives and removable data drives.
Generally when we encrypt the USB flash Drives or fixed data drive, we give a password to unlock the drive. By using a file based certificate we get an additional protector for the drive and we can use it to unlock the drive.
When you connect to a Windows 7 client machine and Open Control Panel –> Bitlocker Drive Encryption, you will see all your Data drives.
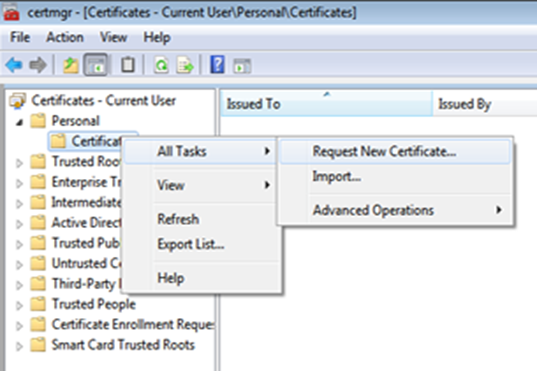
Open Certificate Manager on the client computer.
Expand Personal and click Certificates. Right Click on Certificates and Select All Tasks and then select Request New certificate.
Under the Certificate Templates, select Bitlocker DRA certificate template.
If you do not have the bitlocker DRA template, you can copy the Key Recovery Agent template and then add Bitlocker Drive Encryption and Bitlocker Drive Recovery Agent from the application policies.
NOTE: In case you do not see attributes listed under the Application polices, you should re-login to the domain controller using a schema admin account and install the Bitlocker feature. The ‘Bitlocker Drive Encryption’ and ‘Bitlocker Data Recovery Agent’ application policies will be listed upon installation of the bitlocker feature.
Install the certificate on the computer.
Export the Certificate.
Save the certificate to a location on your computer.
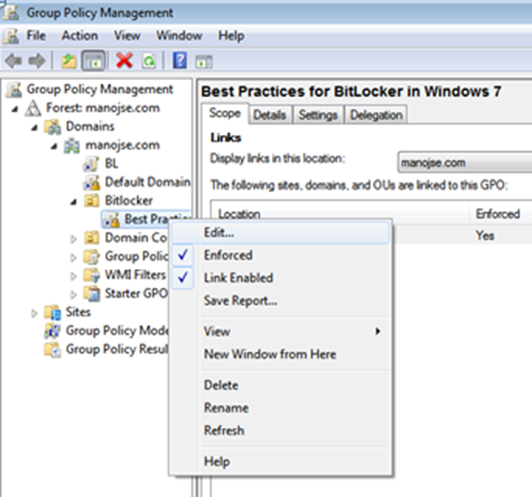
Now we can use a Group Policy to apply the certificate to all machines in the OU.
Open Group Policy Management Console and then add the bitlocker DRA.
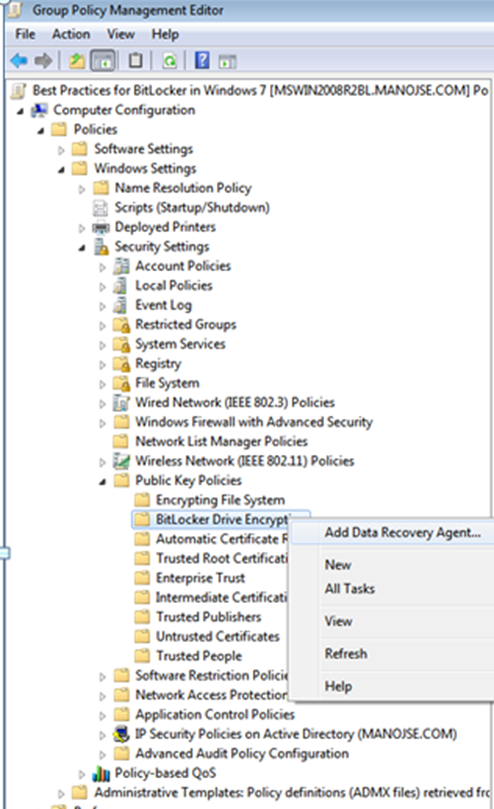
Expand Computer Configuration –> Windows Settings –> Security Settings –> Public Key Policies –> Bitlocker Drive Encryption.
Right click on Bitlocker Drive Encryption and then click Add Data Recovery Agent.
Note:
If a user wants to add additional Bitlocker DRA for his drive, he can add it by using the local security policies.
- Open Group Policy Management Editor (gpedit.msc) on Windows 7 client machine.
- Expand Computer Configuration –> Windows Settings –> Security Settings –> Public Key Policies –> Bitlocker Drive Encryption.
- Right click on Bitlocker Drive Encryption and then click Add Data Recovery Agent
Click Browse Folders and then select the exported certificate (.DER) file which we exported above.
After adding the DRA, go to windows 7 client machine.
After Adding the certificate, run ‘gpupdate /force’ on the client machine.
On Windows 7 client machine, open an elevated command prompt and use the following commands:
To get the protectors, run:
C:\>manage-bde -protectors -get f:
BitLocker Drive Encryption: Configuration Tool version 6.1.7600
Copyright (C) Microsoft Corporation. All rights reserved.
Volume F: [New Volume]
All Key Protectors
Numerical Password:
ID: {FB4FF4B1-AAA3-4BB6-937E-80E7241CA2F2}
Password:
526108-505340-456258-529034-347050-022297-147796-530310
Password:
ID: {96C170CF-65AF-42A7-BEF8-0AD21667C02B}
Smart Card (Certificate Based):
ID: {7BBF31F5-DEBD-4C24-B76F-012855B4EF39}
Certificate Thumbprint:
09141e2c459016b5c51754503956c1d62efeee62
Data Recovery Agent (Certificate Based):
ID: {E1749014-6760-4501-9A48-58152A587279}
Certificate Thumbprint:
1e66a3476615d9a1e51f56aec49024bb34b8a688
To lock the drive, use:
C:>manage-bde -lock f:
BitLocker Drive Encryption: Configuration Tool version 6.1.7600
Copyright (C) Microsoft Corporation. All rights reserved.
Volume F: is now locked
To unlock the device, using the certificate thumbprint, use:
C:\>manage-bde -unlock f: -cert -ct 1e66a3476615d9a1e51f56aec49024bb34b8a688
BitLocker Drive Encryption: Configuration Tool version 6.1.7600
Copyright (C) Microsoft Corporation. All rights reserved.
The certificate successfully unlocked volume F:.
I hope the above information would be useful to everyone. Thanks for your time to read the above information.
More Information:
https://blogs.technet.com/b/bitlocker/
Manoj Sehgal
Senior Support Escalation Engineer
Microsoft Enterprise Platforms Support
![clip_image004[4] clip_image004[4]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/59/75/metablogapi/0181.clip_image0044_thumb_4EAFDE36.jpg)
![clip_image006[4] clip_image006[4]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/59/75/metablogapi/8030.clip_image0064_thumb_6873EE98.jpg)
![clip_image008[4] clip_image008[4]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/59/75/metablogapi/3162.clip_image0084_thumb_3B4EDBFD.jpg)
![clip_image010[4] clip_image010[4]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/59/75/metablogapi/5722.clip_image0104_thumb_6EE7228E.jpg)
![clip_image012[4] clip_image012[4]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/59/75/metablogapi/6305.clip_image0124_thumb_3B7B3965.jpg)
![clip_image013[4] clip_image013[4]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/59/75/metablogapi/6242.clip_image0134_thumb_3F38DE35.png)
![clip_image019[4] clip_image019[4]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/59/75/metablogapi/3007.clip_image0194_thumb_7D1161B2.jpg)
![clip_image021[4] clip_image021[4]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/59/75/metablogapi/0842.clip_image0214_thumb_687BEC67.jpg)