Active Directory OU Permissions Report: Free PowerShell Script Download
Who owns your OUs?
Have you ever lost your keys? It is a scary feeling. Someone out there could have keys to your house and your car. Your personal safety could be at risk. The same is true in Active Directory. Do you know who has the keys to all of your accounts?
The Problem
In Active Directory we need to know who has the keys to our organizational units (OUs), the place where our users and computers live. Over the years OUs have grown to meet needs. Different teams may have been delegated access for managing users, groups, and computers. Then you come along as the new administrator. You probably have no idea where permissions have been granted to your OUs. And the scary thing is… neither does anyone else. I know, because I’ve been there. I hear the same thing from our customers.
Out-of-the-box we do not have a specific tool to report all of the OU permissions. You have to click each OU and view the security tab one-by-one, and we all know that is entirely impractical. Today’s post contains a script download to generate a report of this vital information.
OU Permissions
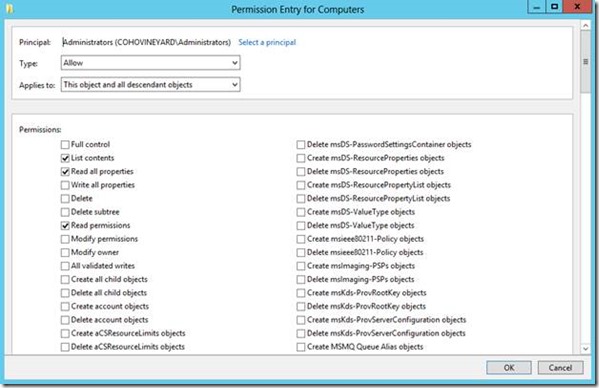
OU permissions are multi-faceted. In other words… it’s complicated. They have a number of properties:
- Principal
- Allow/Deny
- Scope
- Applies To
- Permissions
You’ll see the following dialog when you add a permission. This is enough to explain the complexity of the group access notation:
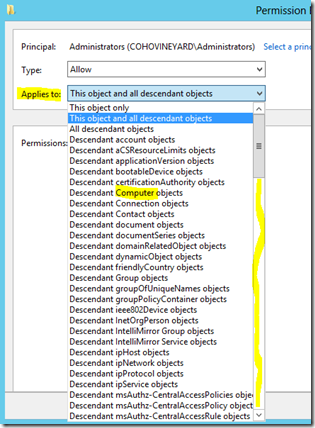
Now look how many Applies to: options there are. Notice that this box scrolls a long way.
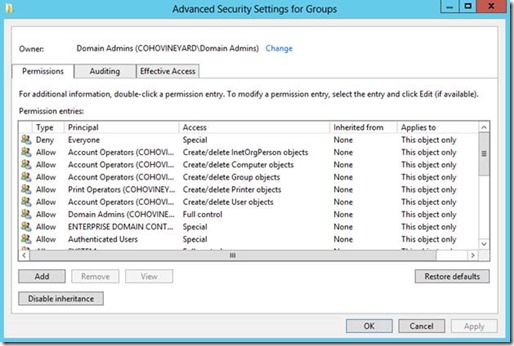
What we need is a report that lists the contents of the Advanced permissions GUI like this for every OU:
The matrix of potential permission configurations is mind-blogging.
The Solution: PowerShell
I had wondered if a report like this could be as simple as:
Import-Module ActiveDirectory
cd AD:
dir –recurse –directory | Get-ACL
Of course what works in our imaginations is rarely as simple in real life. No, that code would not do it. However, the concept is the same:
- Get a list of all OUs
- Loop through the OUs to retrieve their permissions
- Export all data to a CSV file
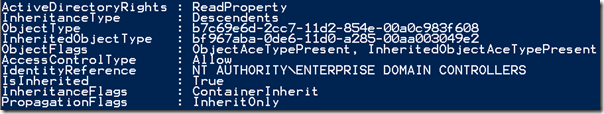
Our good friend Get-ACL reports on more than file system permissions. We can use this same cmdlet to query OU permissions as well. Notice that we preface the OU distinguished name with AD:\. Any time you query permissions with Get-ACL you need to expand the Access property to see the list of permission entries (ACEs):
Get-Acl -Path "AD:\OU=Domain Controllers,DC=wingtiptoys,DC=local" |
Select-Object -ExpandProperty Access
Here is an example of an ActiveDirectoryAccessRule object that is returned for an OU:
We get an entry like this for every permission assigned to the OU. My first instinct was to simply dump a list of these to CSV and be done with it. But then I noticed the ObjectType and InheritedObjectType properties. Hmmmm. These are ugly GUIDs… not what we need for the report. We need to translate these to the names of the objects that receive the permissions. These names are what we see in that long drop-down list in the screenshot above.
To make a long story short I stayed up until 3AM researching this and traced it all down in the Active Directory Technical Specifications (MS-ADTS) here:
You are welcome to read these pages for yourself to understand the relationships. Essentially these GUID values are stored on attributes of selected objects in the schema and configuration partitions of the AD database. You can query these to build a list of names that will make the report readable. So that’s what I did and put them into a hash table for quick look-ups when we generate the report.
The Big Finish
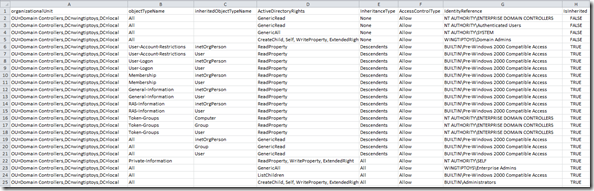
When we script it all out we get a report that looks something like this:
Obviously there are too many columns to read in the screenshot, but it is quite thorough. Now you can use filters and pivot tables in Excel to analyze the data and produce reports showing exactly which OUs have delegated permissions, what kind of permissions, and who has them. Likewise you can pivot the report by group to see a list of all OUs that a group can control. You may want to filter the output by the IsInherited property. By filtering for FALSE you will find everywhere that permissions are explicitly delegated in the OU tree.
Conclusion
I would advise all Active Directory shops to run and review this report on a quarterly basis to make sure there are no surprise administrators lurking in your domain. The report can be quite large for any size organization. Perhaps this would be a good report to feed to the Information Security team, if you have one. Now you know who holds the keys.
Download the full script from the TechNet Script Gallery.