Creating a Private Cloud – Part 1: Setup
Can I offer IT as a Service?
Virtualization offers many benefits; it’s the technological change in our industry that underpins the Cloud Computing wave. With Virtualization, you can reduce the number of physical servers you own and maintain, reduce energy costs, even implement high availability solutions you thought beyond your budgets. Then you look at Windows Azure, and you see the ability to provision application instances from a web portal. Scale up and down as demand requires and only pay for what you consume. The thought then maybe crosses your mind that the Windows Azure model would be great to offer inside your organization on your own infrastructure. Do you have to choose one or the other or can you provide IT as a Service internally like Windows Azure?
The answer is yes, and that is not because of the Windows Azure Appliance announcement. Appliance aside, you can offer IT as a Service using Windows Server and System Center today. So how do you do that? In these two posts I’ll explain how.
What do I need?
For a Private Cloud or Customer Cloud, whichever name you prefer, to have an effective IT as a Service offering requires some key elements to be in-place.
- First you need a management tool that allows you to monitor the servers providing the virtualization services. The tool should also allow you to easily move services around the machines, and ideally provide you with guidance on what actions to take should resource become over utilised.
- Secondly, you need a tool that allows for the Business units in your organization to be self-sufficient in requesting and managing their services, while at the same time provide you with a method to calculate charge-back costs.
Windows Server 2008 R2 out-of-the-box does not provide all of these. It does have a number of management features you will need, but for the complete solution you need to add:-
- System Center Virtual Machine Manager 2008 R2 (SCVMM)
- System Center Virtual Machine Manager Self Service Portal 2.0 (SSP)
These two System Center products provide the management, monitoring and self-service capabilities needed to run an IT as a Service operation.
What do they do?
SCVMM provides the core management functionality. Allowing you to go beyond the Hyper-V management console in R2, you can group your servers into host groups and monitor more than one host at a time. Intelligent placement built into SCVMM helps you make the best decisions about where virtual machines (VMs) should go. SCVMM also provides a library service where you hold template images, ISO images and scripts that can be easily deployed to meet different requirements. Finally Performance Resource Optimization (PRO) provides you with the ability to monitor and correct problems for VMs. PRO allows the administrator to set up information that can be displayed when certain thresholds are reached. These “Tips”, can, for example, have a messaging saying “Add another Web Server to Order Tracking Web Farm”.
SSP provides the self-service functionality. At a high level, once enabled and configured by the IT Administrator, SSP allows registered Business Units to manage their own administrative team to request resources, start or stop VMs and be entirely self-sufficient in managing their resources. At the back end, the IT Administrator can set charge back costs for both reserved resources and allocated resources.
Armed with these products we can build our Private Cloud. To test this out, all three products can be downloaded from microsoft.com under the evaluation program. I used my TechNet subscription to access the full-version software and based these posts on my testing. The software required to build this test is available in all the subscriptions models.
Where to Start?
There are requirements for the installation to work. First, there are additional roles and features that need to be installed on Windows Server 2008 R2. These are primarily driven by SCVMM. So to install SCVMM, Windows Server must have:
- Hyper-V. The SCVMM Setup Wizard automatically adds this role, which will work as long as the machine being used supports virtualization.
- Windows Remote Management (WinRM). For SCVMM setup to work, the service must be installed and in a state other than disabled and stopped.
- Internet Information Services (IIS) 7.0. You must add the Web Server (IIS) role and then install the following server role services:
- IIS 6 Metabase Compatibility
- IIS 6 WMI Compatibility
- Static Content
- Default Document
- Directory Browsing
- HTTP Errors
- ASP.NET
- .NET Extensibility
- ISAPI Extensions
- ISAPI Filters
- Request Filtering
In addition to these, the SSP also requires some additional features be installed:
- Microsoft Message Queuing (MSMQ).
- Windows PowerShell 2.0. This requirement supersedes version 1.0 that SCVMM requires.
- Microsoft .NET Framework 3.5 SP1. R2 contains 3.5.1, so if this is installed then you have met this requirement.
The final requirement for both SCVMM and SSP is a database. When installed alone, SCVMM can use the SQL Express edition, which it will install automatically if you do not provide it with an alternative. However, SSP requires either Standard or Enterprise editions of SQL Server 2008 or higher.
The other requirement for the solutions is Active Directory. Both SCVMM and SSP work best in a domain environment. As we go through SSP, it will become clear why this is so.
In my test environment I’ve mixed and matched. The base OS is R2 Enterprise edition, the database server is SQL Server 2008 R2 Standard edition. At this point that you may consider installing the beta of Service Pack 1 for Windows Server 2008 R2 to take advantage of the Dynamic Memory feature. This is an extremely useful feature for maximizing the memory usage on Hyper-V hosts; the caveat here is that the SSP documentation doesn’t yet have any recommendation on how this feature interacts with the Charge-back process. I didn’t install SP1 beta for that very reason, but I do encourage you to evaluate it for potential use on production Hyper-V hosts.
Installing stuff!
We now have our shopping list of items to setup our test Private Cloud and the installation order is:
- Install Windows Server 2008 R2,
- Add the Hyper-V and IIS 7.0 roles with the IIS requirements.
- Add the additional features, MSMQ.
- Install Active Directory Domain Services (AD DS).
- Install SQL Server. Your choice of 2008 or 2008 R2, standard or enterprise editions.
- Check for updates.
- Install SCVMM Server
- Install SCVMM Administrator Console.
- Check for Updates
- VMMSSP server component
- VMMSSP website component
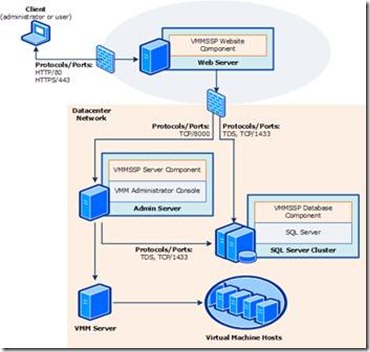 I used the default settings when installing the base products and only varied off the defaults where there were specific requirements, like with IIS 7.0. I had to run the SCVMM install twice in my environment. This is because the recommended configuration for SCVMM/SSP is at least a three server configuration with a minimum of the VMM Server, Admin Console and SQL Database on different machines. In my test environment I’ve used just one machine initially.
I used the default settings when installing the base products and only varied off the defaults where there were specific requirements, like with IIS 7.0. I had to run the SCVMM install twice in my environment. This is because the recommended configuration for SCVMM/SSP is at least a three server configuration with a minimum of the VMM Server, Admin Console and SQL Database on different machines. In my test environment I’ve used just one machine initially.
Generally one VMM server is all you need, it’s the hub of the system and is generally left alone. If you scale out the environment, you will need to install another VMM server, but we talking about where you have more than 400 hosts. The Admin console is like most admin consoles for server products, you install it on the machine used most to administer your environment, so it’s likely you won’t be doing that from the VMM Server.
The Interesting bit!
The interesting component of all these is SSP. It’s the interesting bit because it’s a combination of software and process. You are installing a web portal for others to use, so as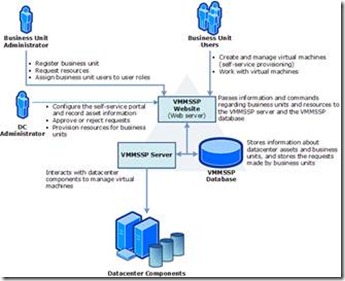 part of that you have to decide how to divide up your business units. Who the admins are for those units and then decide on the charge model you wish to follow. I’m using the diagrams from the “Getting Started” guide to illustrate the basics; the documentation that comes with SSP is very detailed.
part of that you have to decide how to divide up your business units. Who the admins are for those units and then decide on the charge model you wish to follow. I’m using the diagrams from the “Getting Started” guide to illustrate the basics; the documentation that comes with SSP is very detailed.
The SSP interaction is a workflow, there are user roles pre-defined in the SSP to help manage the process. There are three; these are DataCenter IT Admin (DCIT Admin), Business Unit IT Admin (BUIT Admin), Advanced Operator, and Business Unit User. Throughout the process the DCIT Admin is the approver of all requests. The BUIT Admin only controls who from their unit can have access and what access. The DCIT Admin first defines a BUIT Admin. Once defined, that admin then registers their BU for the portal access. The DCIT Admin approves the request thus allowing the BUIT Admin to make infrastructure requests. Again the DCIT Admin provisions the request. This now allows the Business Unit Users to create virtual machines, again using the portal and forms and manage their machines.
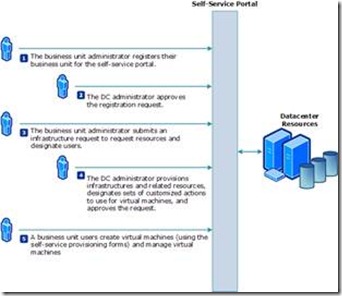 As described previously, business units can use the self-service portal to manage their own infrastructures while using the physical resources of a central datacenter.
As described previously, business units can use the self-service portal to manage their own infrastructures while using the physical resources of a central datacenter.
In the context of the self-service portal, an infrastructure is a collection of services that a business unit needs for a specific purpose. For example, a human resources business unit may create an infrastructure called “Payroll” that contains the services needed to run the payroll system. A single business unit can manage multiple infrastructures.
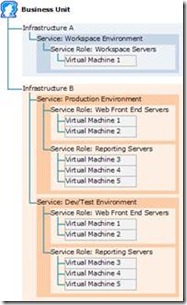 An infrastructure must contain at least one service. The service coordinates the resources needed for a specific function or set of related functions. These resources include networks, Active Directory domains and organizational units, users that have access to the service, memory and storage capacity available to the virtual machines, and locations of virtual machine templates to use in creating virtual machines. The diagram here shows the details of two infrastructures that a business unit creates. One with one service and service role, the other two services each with two service roles.
An infrastructure must contain at least one service. The service coordinates the resources needed for a specific function or set of related functions. These resources include networks, Active Directory domains and organizational units, users that have access to the service, memory and storage capacity available to the virtual machines, and locations of virtual machine templates to use in creating virtual machines. The diagram here shows the details of two infrastructures that a business unit creates. One with one service and service role, the other two services each with two service roles.
A service must contain at least one service role. A service role is a group of virtual machines that perform a single function and share some configuration settings. In our example, a Web application, a BUIT administrator can request a service role of load-balanced virtual Web servers. The load balancing configuration of the service role applies to each member virtual machine. The BUIT administrator can request new virtual machines for the service role as appropriate.
Next Steps
This post spent a lot of time on basics of SSP, which is key component for enabling users outside the IT Department to become self-sufficient. In the next post I’ll cover the actual configuration of the components.