Advisory-Auditing cluster regkey
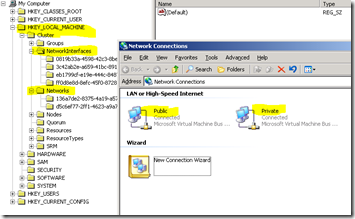
Audit any changes in the cluster registry (HKEY_LOCAL_MACHINE\Cluster) in a windows 2003 cluster environment.
Purpose:
Advisory-Auditing cluster regkey
Action Plan:
Please be aware that the type of information that the Audit gives in windows 2003 is not so explicit as it is in more recent operating systems like in windows 2008.
Identify type of changes made either manually by editing the resource in the registry or possibly some script or application that run
1:
Those action in terms of the GPO and the Registry need to be applied equally on all the nodes of the cluster.
324739 HOW TO: Use Group Policy to Audit Registry Keys in Windows Server 2003
https://support.microsoft.com/kb/324739
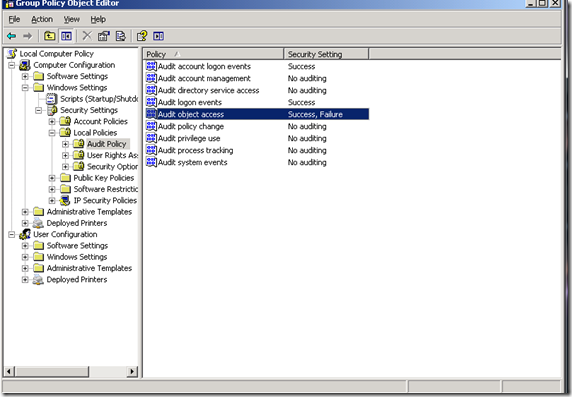
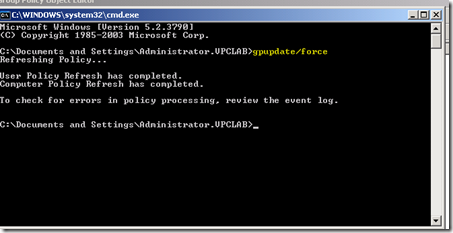
Turn On Auditing on a Computer
1. Click Start, and then click Run.
2. In the Open box, type gpedit.msc, and then click OK.
3. Under Computer Configuration, expand Windows Settings, expand Security Settings, expand Local Policies, and then click Audit Policy.
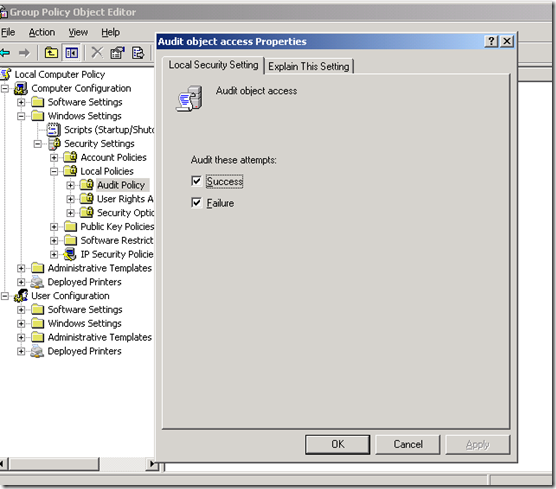
4. In the right pane, double-click Audit object access.
5. Click to select the Success check box, click to select the Failure check box, and then click OK.
NOTE: The Audit object access policy is enough to turn on auditing for the Windows registry.
6. Quit the Group Policy Object Editor snap-in.
2:
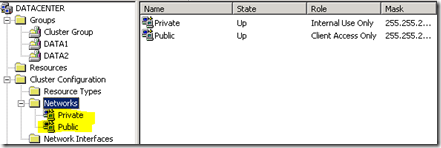
Audit a Registry Key
1. Click Start, and then click Run.
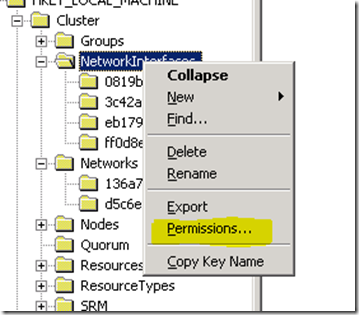
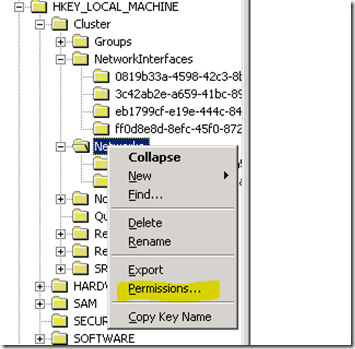
2. In the Open box, type regedit, and then click OK.
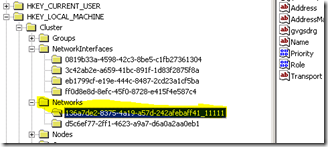
3. Locate and click the registry key that you want to audit, for example:
HKEY_LOCAL_MACHINE\Cluster\NetworkInterfaces
HKEY_LOCAL_MACHINE\Cluster\Networks
4. On the Edit menu, click Permissions.
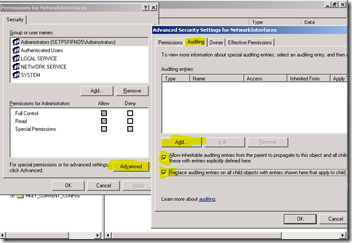
5. Click Advanced, click the Auditing tab, and then click Add.
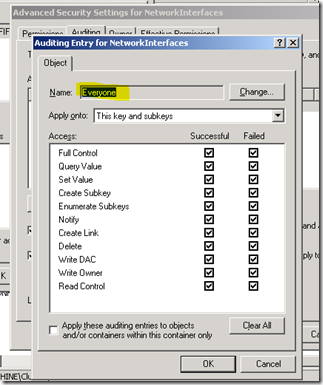
6. Type the user EVERYONE to this registry key you want to audit, click Check Names to verify the name, and then click OK.
7. In the Apply onto box, click the option that you want.
8. Click to select the Successful and Failed check boxes next to the following access types:
9. Click OK, and then click OK.
10. Quit Registry Editor.
Audit events are displayed in the Security log of Event Viewer
Example:
3:
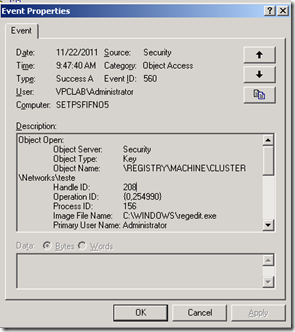
Those are the events that are generated.
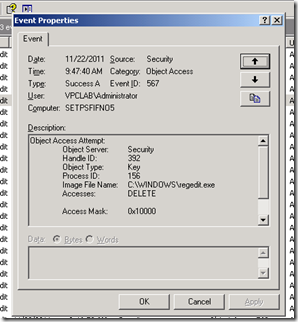
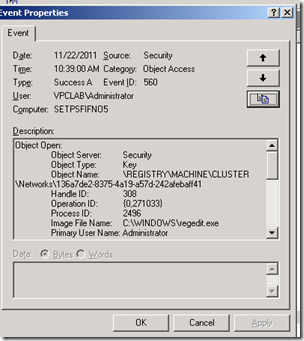
3.1:
3.2:
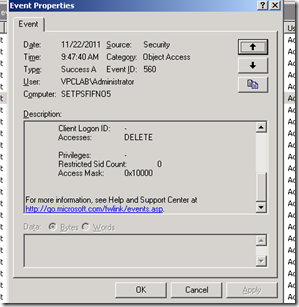
Detailed events that are reported if we delete or change any key,
3.2:
Detailed events that are reported if we delete or change any key,
Event Type: Success Audit
Event Source: Security
Event Category: Object Access
Event ID: 560
Date: 11/22/2011
Time: 10:38:59 AM
User: VPCLAB\Administrator
Computer: SETPSFIFNO5
Description:
Object Open:
Object Server: Security
Object Type: Key
Object Name: \REGISTRY\MACHINE\CLUSTER\Networks
Handle ID: 312
Operation ID: {0,270998}
Process ID: 2496
Image File Name: C:\WINDOWS\regedit.exe
Primary User Name: Administrator
Primary Domain: VPCLAB
Primary Logon ID: (0x0,0x28D54)
Client User Name: Administrator
Client Domain: VPCLAB
Client Logon ID: (0x0,0x28D54)
Accesses: READ_CONTROL
Query key value
Enumerate sub-keys
Privileges: -
Restricted Sid Count: 0
Access Mask: 0x20009
Event Type: Success Audit
Event Source: Security
Event Category: Object Access
Event ID: 560
Date: 11/22/2011
Time: 10:39:00 AM
User: VPCLAB\Administrator
Computer: SETPSFIFNO5
Description:
Object Open:
Object Server: Security
Object Type: Key
Object Name: \REGISTRY\MACHINE\CLUSTER\Networks\136a7de2-8375-4a19-a57d-242afebaff41
Handle ID: 308
Operation ID: {0,271033}
Process ID: 2496
Image File Name: C:\WINDOWS\regedit.exe
Primary User Name: Administrator
Primary Domain: VPCLAB
Primary Logon ID: (0x0,0x28D54)
Client User Name: Administrator
Client Domain: VPCLAB
Client Logon ID: (0x0,0x28D54)
Accesses: READ_CONTROL
ACCESS_SYS_SEC
Query key value
Enumerate sub-keys
Privileges: SeSecurityPrivilege
Restricted Sid Count: 0
Access Mask: 0x1020009
Event Type: Success Audit
Event Source: Security
Event Category: Object Access
Event ID: 560
Date: 11/22/2011
Time: 10:39:00 AM
User: VPCLAB\Administrator
Computer: SETPSFIFNO5
Description:
Object Open:
Object Server: Security
Object Type: Key
Object Name: \REGISTRY\MACHINE\CLUSTER\Networks\136a7de2-8375-4a19-a57d-242afebaff41
Handle ID: 308
Operation ID: {0,271033}
Process ID: 2496
Image File Name: C:\WINDOWS\regedit.exe
Primary User Name: Administrator
Primary Domain: VPCLAB
Primary Logon ID: (0x0,0x28D54)
Client User Name: Administrator
Client Domain: VPCLAB
Client Logon ID: (0x0,0x28D54)
Accesses: READ_CONTROL
ACCESS_SYS_SEC
Query key value
Enumerate sub-keys
Privileges: SeSecurityPrivilege
Restricted Sid Count: 0
Access Mask: 0x1020009
Event Type: Success Audit
Event Source: Security
Event Category: Object Access
Event ID: 560
Date: 11/22/2011
Time: 10:39:00 AM
User: VPCLAB\Administrator
Computer: SETPSFIFNO5
Description:
Object Open:
Object Server: Security
Object Type: Key
Object Name: \REGISTRY\MACHINE\CLUSTER\Networks\136a7de2-8375-4a19-a57d-242afebaff41
Handle ID: 308
Operation ID: {0,271038}
Process ID: 2496
Image File Name: C:\WINDOWS\regedit.exe
Primary User Name: Administrator
Primary Domain: VPCLAB
Primary Logon ID: (0x0,0x28D54)
Client User Name: Administrator
Client Domain: VPCLAB
Client Logon ID: (0x0,0x28D54)
Accesses: READ_CONTROL
Privileges: -
Restricted Sid Count: 0
Access Mask: 0x20000
Event Type: Success Audit
Event Source: Security
Event Category: Object Access
Event ID: 560
Date: 11/22/2011
Time: 10:39:00 AM
User: VPCLAB\Administrator
Computer: SETPSFIFNO5
Description:
Object Open:
Object Server: Security
Object Type: Key
Object Name: \REGISTRY\MACHINE\CLUSTER\Networks
Handle ID: 308
Operation ID: {0,271039}
Process ID: 2496
Image File Name: C:\WINDOWS\regedit.exe
Primary User Name: Administrator
Primary Domain: VPCLAB
Primary Logon ID: (0x0,0x28D54)
Client User Name: Administrator
Client Domain: VPCLAB
Client Logon ID: (0x0,0x28D54)
Accesses: READ_CONTROL
ACCESS_SYS_SEC
Query key value
Enumerate sub-keys
Privileges: SeSecurityPrivilege
Restricted Sid Count: 0
Access Mask: 0x1020009
Event Type: Success Audit
Event Source: Security
Event Category: Object Access
Event ID: 560
Date: 11/22/2011
Time: 10:39:04 AM
User: VPCLAB\Administrator
Computer: SETPSFIFNO5
Description:
Object Open:
Object Server: Security
Object Type: Key
Object Name: \REGISTRY\MACHINE\CLUSTER\Networks\136a7de2-8375-4a19-a57d-242afebaff41
Handle ID: 256
Operation ID: {0,271122}
Process ID: 2496
Image File Name: C:\WINDOWS\regedit.exe
Primary User Name: Administrator
Primary Domain: VPCLAB
Primary Logon ID: (0x0,0x28D54)
Client User Name: -
Client Domain: -
Client Logon ID: -
Accesses: DELETE
READ_CONTROL
WRITE_DAC
WRITE_OWNER
Query key value
Set key value
Create sub-key
Enumerate sub-keys
Notify about changes to keys
Create Link
Privileges: -
Restricted Sid Count: 0
Access Mask: 0xF003F
Event Type: Success Audit
Event Source: Security
Event Category: Object Access
Event ID: 560
Date: 11/22/2011
Time: 10:39:12 AM
User: VPCLAB\Administrator
Computer: SETPSFIFNO5
Description:
Object Open:
Object Server: Security
Object Type: Key
Object Name: \REGISTRY\MACHINE\CLUSTER\Networks\136a7de2-8375-4a19-a57d-242afebaff41
Handle ID: 304
Operation ID: {0,271256}
Process ID: 2496
Image File Name: C:\WINDOWS\regedit.exe
Primary User Name: Administrator
Primary Domain: VPCLAB
Primary Logon ID: (0x0,0x28D54)
Client User Name: -
Client Domain: -
Client Logon ID: -
Accesses: Query key value
Enumerate sub-keys
Privileges: -
Restricted Sid Count: 0
Access Mask: 0x9
Event Type: Success Audit
Event Source: Security
Event Category: Object Access
Event ID: 560
Date: 11/22/2011
Time: 10:39:12 AM
User: VPCLAB\Administrator
Computer: SETPSFIFNO5
Description:
Object Open:
Object Server: Security
Object Type: Key
Object Name: \REGISTRY\MACHINE\CLUSTER\Networks\136a7de2-8375-4a19-a57d-242afebaff41
Handle ID: 256
Operation ID: {0,271259}
Process ID: 2496
Image File Name: C:\WINDOWS\regedit.exe
Primary User Name: Administrator
Primary Domain: VPCLAB
Primary Logon ID: (0x0,0x28D54)
Client User Name: -
Client Domain: -
Client Logon ID: -
Accesses: Query key value
Enumerate sub-keys
Privileges: -
Restricted Sid Count: 0
Access Mask: 0x9
Event Type: Success Audit
Event Source: Security
Event Category: Object Access
Event ID: 560
Date: 11/22/2011
Time: 10:39:12 AM
User: VPCLAB\Administrator
Computer: SETPSFIFNO5
Description:
Object Open:
Object Server: Security
Object Type: Key
Object Name: \REGISTRY\MACHINE\CLUSTER\Networks\136a7de2-8375-4a19-a57d-242afebaff41
Handle ID: 256
Operation ID: {0,271260}
Process ID: 2496
Image File Name: C:\WINDOWS\regedit.exe
Primary User Name: Administrator
Primary Domain: VPCLAB
Primary Logon ID: (0x0,0x28D54)
Client User Name: -
Client Domain: -
Client Logon ID: -
Accesses: DELETE
Privileges: -
Restricted Sid Count: 0
Access Mask: 0x10000
Event Type: Success Audit
Event Source: Security
Event Category: Object Access
Event ID: 560
Date: 11/22/2011
Time: 10:49:40 AM
User: VPCLAB\Administrator
Computer: SETPSFIFNO5
Description:
Object Open:
Object Server: Security
Object Type: Key
Object Name: \REGISTRY\MACHINE\CLUSTER\Networks\teste
Handle ID: 308
Operation ID: {0,294077}
Process ID: 2496
Image File Name: C:\WINDOWS\regedit.exe
Primary User Name: Administrator
Primary Domain: VPCLAB
Primary Logon ID: (0x0,0x28D54)
Client User Name: -
Client Domain: -
Client Logon ID: -
Accesses: DELETE
Privileges: -
Restricted Sid Count: 0
Access Mask: 0x10000
4:
New in Windows 2008/2008 R2
Configuring Auditing for a Windows Server 2008 Failover Cluster
The Windows Server 2008 Failover Clustering auditing feature has been requested by customers and provides the capability to monitor, or audit, cluster access. The cluster auditing feature can be enabled to audit accesses (Success and\or Failure) of an object. The object, in this case, will be the Microsoft Failover Cluster. This is accomplished by auditing client accesses to a cluster using Cluster APIs. This basically means that a client trying to access a cluster using either the Failover Cluster Management snap-in (Cluadmin.msc), the cluster.exe command line or any custom application that calls cluster APIs, will be subjected to auditing events if configured.